EngageLab SDK flaw exposed millions of Android crypto wallet users to data theft risk

A security flaw in the EngageLab Android SDK exposed more than 30 million crypto wallet app installations to possible data theft, according to Microsoft. The company said the bug allowed a malicious app on the same device to bypass Android’s sandbox protections and gain unauthorized access to private app data.
The issue affected EngageSDK, a third-party library developers use for push notifications and in-app messaging. Microsoft said the broader impact stretched beyond crypto wallets, with total exposure across all affected Android apps topping 50 million installations.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
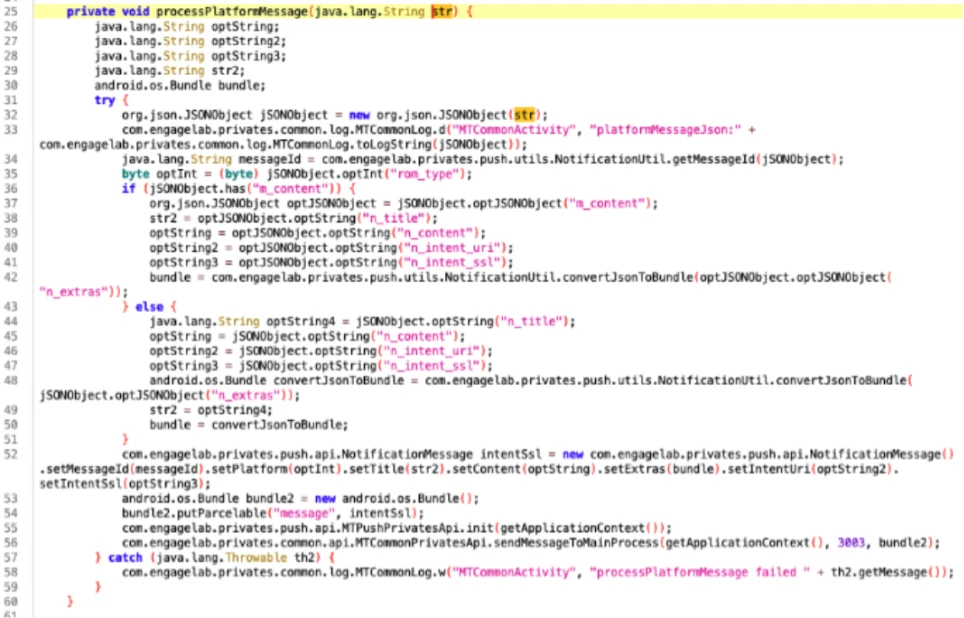
Microsoft said the flaw was an intent redirection vulnerability inside an exported activity called MTCommonActivity. Because the activity was added to the merged Android manifest during the build process, developers may not have noticed it in their original source code.
How the flaw worked
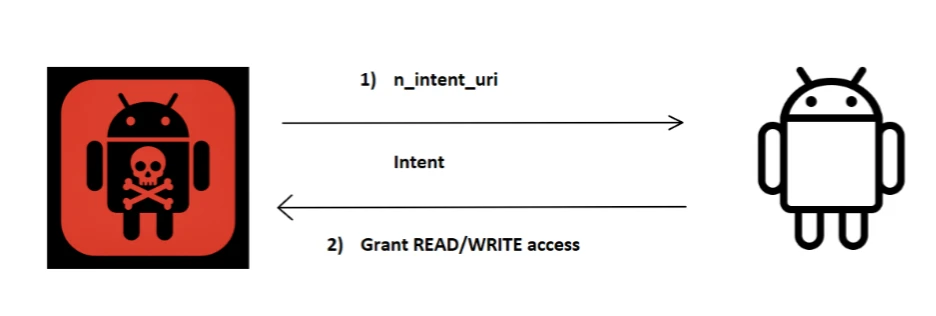
On Android, apps communicate through intents. Microsoft said a malicious app could send a crafted URI to the exposed MTCommonActivity, which then passed it through internal methods and launched a new intent using the trusted app’s own permissions.
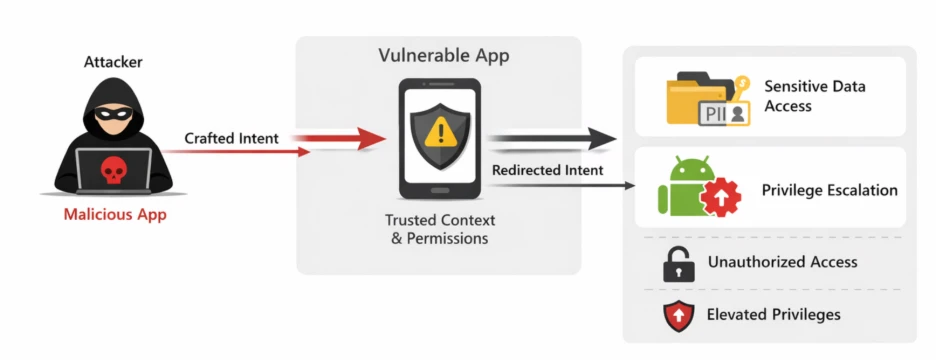
That flow created a dangerous trust break. Microsoft said the SDK used the URI_ALLOW_UNSAFE flag, which let attacker-controlled input carry read and write permission flags and potentially gain persistent access to sensitive app storage.
In affected wallet apps, that could expose credentials, financial data, and other private information. Microsoft said all detected apps using vulnerable SDK versions were removed from Google Play, and it found no evidence of active exploitation at the time of disclosure.
Why this bug matters
This case shows the risk that comes with third-party mobile libraries. A single vulnerable SDK can spread the same weakness across many unrelated apps, including apps that handle money, credentials, and highly sensitive personal data.
Microsoft said the flaw was first found in EngageSDK version 4.5.4 in April 2025. It reported the issue to EngageLab through coordinated disclosure, then escalated it to the Android Security Team in May 2025 because the problem affected apps distributed through Google Play.
EngageLab fixed the issue in version 5.2.1 on November 3, 2025 by marking the vulnerable activity as non-exported. Microsoft also said Android’s layered security model can provide added mitigations against some intent-based abuse, which helped reduce exploitation risk while the ecosystem patched.
Key details
| Item | Details |
|---|---|
| Affected component | EngageLab EngageSDK for Android |
| Vulnerability type | Intent redirection |
| Risk | Unauthorized access to private app data |
| Crypto wallet exposure | 30M+ installations |
| Total app exposure | 50M+ installations |
| First affected version identified | 4.5.4 |
| Fixed version | 5.2.1 |
| Fix date | November 3, 2025 |
| Exploitation seen in the wild | No evidence reported by Microsoft |
The figures and timeline above come from Microsoft’s April 9 security write-up and follow-on reporting.
What developers and users should do
- Upgrade to EngageSDK 5.2.1 or later immediately.
- Inspect the merged Android manifest after every build, not just the original source files.
- Review exported activities and permissions introduced by third-party SDKs.
- Validate all incoming intent data before the app processes it.
- Remove or replace outdated app dependencies that quietly expand app attack surface.
For users, the immediate risk appears lower now than it was before disclosure because vulnerable apps identified by Microsoft were removed from Google Play and Android has deployed automatic mitigations for this specific issue. Still, anyone using sideloaded or outdated wallet apps should update as soon as a patched version becomes available.
The bigger lesson is that mobile app security no longer depends only on the code a developer writes directly. It also depends on every SDK that enters the build, every manifest change added during compilation, and every trust assumption made between apps on the same device.
FAQ
It is an Android software development kit from EngageLab that helps apps add push notifications and real-time messaging features.
Microsoft said more than 30 million crypto wallet app installs were exposed, and total exposure across all affected apps exceeded 50 million installs.
Microsoft said it had no evidence of in-the-wild exploitation at the time it published the disclosure.
EngageLab fixed the bug in EngageSDK version 5.2.1 on November 3, 2025.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages