Exposed server leaks TheGentlemen ransomware toolkit, victim credentials, and ngrok tokens

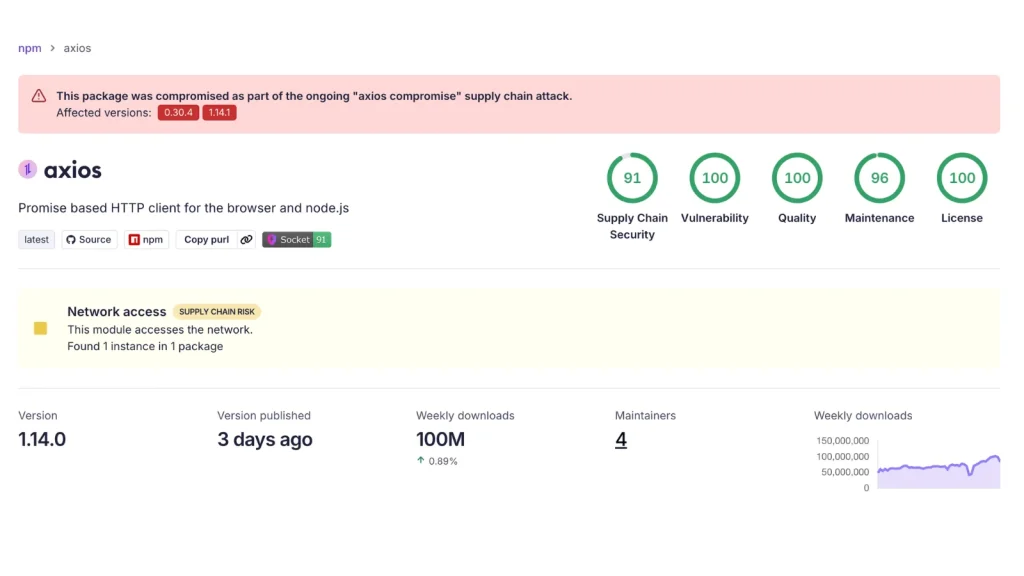
An exposed server has revealed what looks like the full working toolkit of a TheGentlemen ransomware affiliate, giving defenders a rare look at how one operator prepared systems for encryption, disabled defenses, and maintained remote access. Hunt.io said the open directory sat on infrastructure tied to Proton66, a Russia-linked bulletproof hosting provider, and contained both attack tools and data tied to real victim activity.
The leak matters because it does not show a single malware sample in isolation. It shows how an affiliate appears to move from initial access to full ransomware deployment, with scripts for defense evasion, credential theft, persistence, and remote tunnel setup already staged on one exposed server.
TheGentlemen itself is not a fringe name at this point. Trend Micro described the group in September 2025 as a ransomware operation that uses legitimate tools, privilege escalation, and environment-specific evasion to move quickly inside victim networks, while FortiGuard now tracks The Gentlemen as an active ransomware threat actor that targets organizations with double-extortion tactics.
What the exposed server reportedly contained
According to Hunt.io, the exposed system was reachable at 176.120.22[.]127 over port 80 and had been live long enough to hold a substantial archive of operational material. The directory reportedly contained about 140 MB of data, including scripts, logs, and configuration files with sensitive tokens.
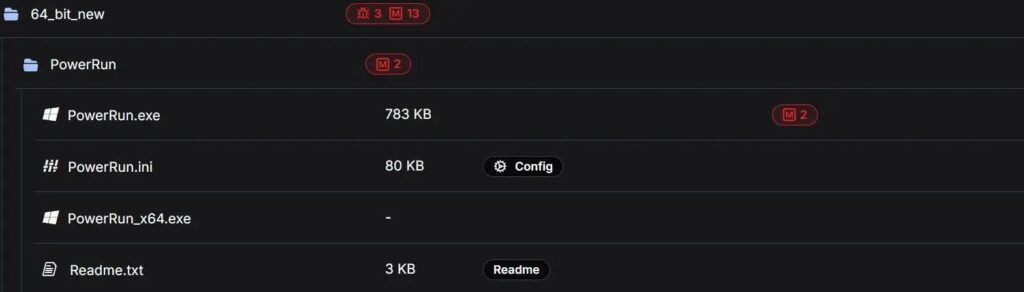
The most important file was z1.bat, a large pre-ransomware deployment script that Hunt.io said bundled together many of the steps attackers usually perform right before encryption. The report says the script disabled or removed security products, stopped enterprise services, opened SMB shares, enabled remote access, weakened Windows protections, deleted shadow copies, and cleared event logs to make recovery harder.
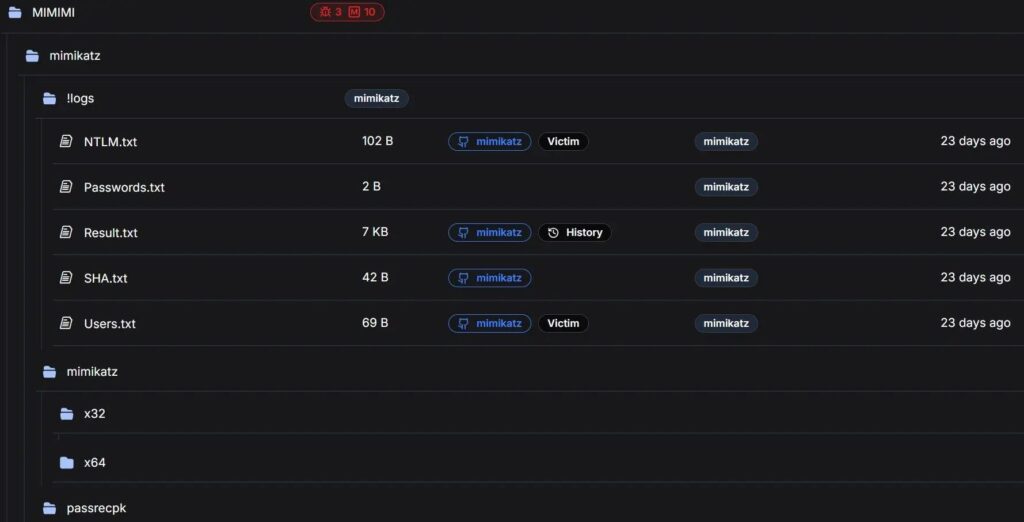
Your sample also notes that the server held Mimikatz logs, plaintext ngrok authentication tokens, and evidence of real-world deployment rather than unused tooling. Hunt.io’s findings align with that description, which makes this leak especially serious because it suggests the infrastructure had already supported live intrusions, not just testing or staging.
Why defenders should pay attention
Security teams should treat this leak as a practical map of affiliate behavior. Hunt.io says defenders should watch for bulk service disabling, Windows Defender tampering, IFEO debugger changes on accessibility binaries, WDigest-related registry activity, LSASS access tied to credential theft, mass network share creation, and vssadmin shadow copy deletion.
Those recommendations line up with long-standing government guidance. CISA’s StopRansomware guide urges organizations to harden backups, segment networks, enforce MFA, patch exposed services, and prepare incident response procedures before an attack hits, while its response checklist tells victims to isolate affected systems immediately and preserve forensic evidence.
The wider lesson is simple. Ransomware crews no longer rely only on the final encryptor to do damage. They build repeatable pre-encryption workflows that disable security controls, weaken recovery options, and leave defenders racing against a process that can unfold in hours. That is exactly why exposed affiliate infrastructure like this gives defenders useful insight even when the operators themselves remain active.
Key takeaways
- Hunt.io said the exposed server sat on Proton66 infrastructure and contained 126 files across 18 directories.
- The leaked material reportedly included victim credentials, Mimikatz logs, and ngrok tokens.
- The z1.bat script appeared designed to disable defenses and prepare systems for fast ransomware deployment.
- Trend Micro and FortiGuard have both documented The Gentlemen as an active ransomware threat.
- CISA recommends isolation, backup protection, MFA, segmentation, and response planning to reduce ransomware impact.
Indicators and behaviors to watch
| Area | Reported behavior | Why it matters |
|---|---|---|
| Endpoint defense | Security tools disabled or removed | Cuts visibility before encryption |
| Credential access | Mimikatz logs and LSASS-related activity | Helps attackers expand access |
| Persistence | IFEO debugger changes on accessibility tools | Can preserve elevated access |
| Remote access | ngrok tunnel setup and token storage | Hides attacker connectivity |
| Recovery sabotage | Shadow copies deleted, logs cleared | Slows restoration and investigation |
| Network spread | SMB shares opened across drives | Improves lateral reach |
FAQ
It appears to expose the affiliate’s working environment, not just a malware sample or victim note. That gives defenders a broader view of how tools, scripts, and credentials fit together before encryption starts.
Hunt.io said the directory contained signs that the tools had already been used against real victims, including harvested credentials and operational logs. Your sample makes the same point, and the Hunt.io report supports it.
Hunt.io described z1.bat as the most operationally revealing file in the directory because it bundled many pre-encryption steps into one script. It reportedly disabled protections, stopped services, enabled access, deleted backups, and cleared logs.
CISA says organizations should isolate impacted systems right away, determine what was affected, preserve forensic evidence, and begin response procedures using a prepared checklist.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages