Fake Google Forms job lures now push PureHVNC malware in multi-stage attack
Attackers have started using fake Google Forms as the front end for a malware campaign that delivers the PureHVNC remote access trojan. Security researchers say the lures mimic job interviews, project briefs, and business documents, then push victims toward ZIP files hosted on file-sharing services. The goal is simple: get users to trust a familiar workflow long enough to infect their Windows machines.
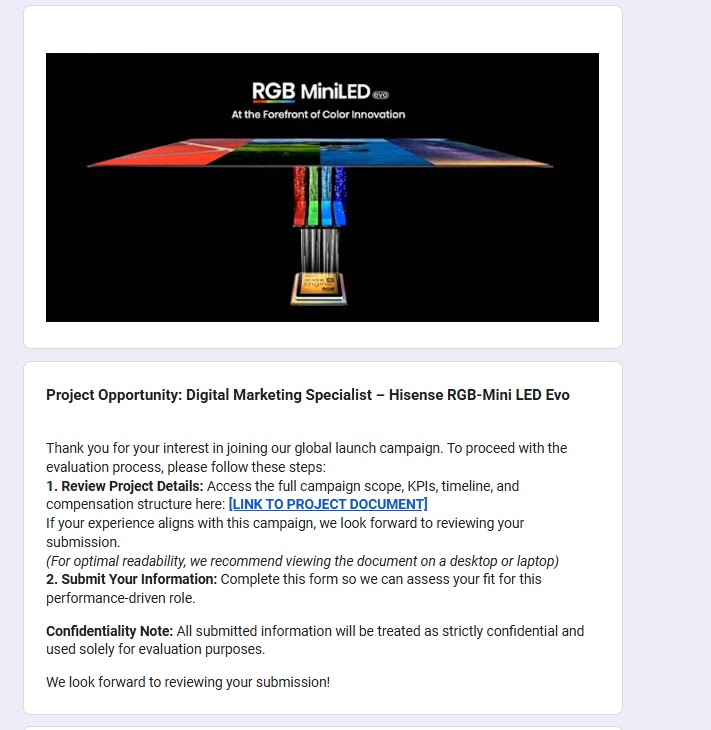
Malwarebytes said the campaign stands out less for the malware itself and more for how it starts. Instead of a standard phishing email or fake download page, the attackers use Google Forms that look like real recruiting or business intake forms, often with company branding and professional questions. Once the victim submits the form or follows the next step, they land on a ZIP file hosted through services such as Dropbox, filedn.com, and fshare.vn, or through shortened links that hide the final destination.
The campaign also spreads through LinkedIn, which gives it a natural path to job seekers and professionals who already expect to receive resumes, interview packs, project summaries, and shared documents. That makes the lure far more believable than a random email attachment. Malwarebytes said the forms impersonate real companies across finance, logistics, tech, sustainability, and energy, using recognizable names and logos to lower suspicion.
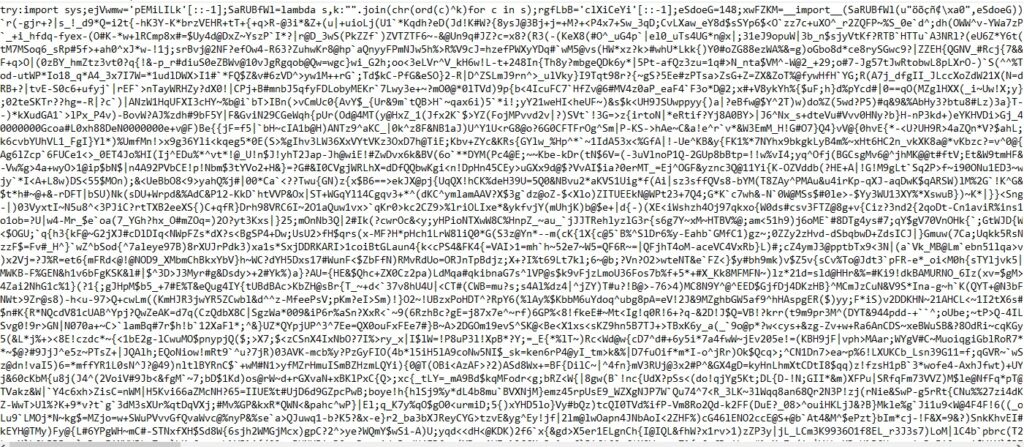
Once the ZIP file is opened, the infection chain turns much more technical. Malwarebytes said victims typically find job-related or business-themed files alongside a hidden executable and a malicious msimg32.dll file. The attack then uses DLL hijacking to load that malicious code through a legitimate application, which helps it stay quieter during the early stages of infection.
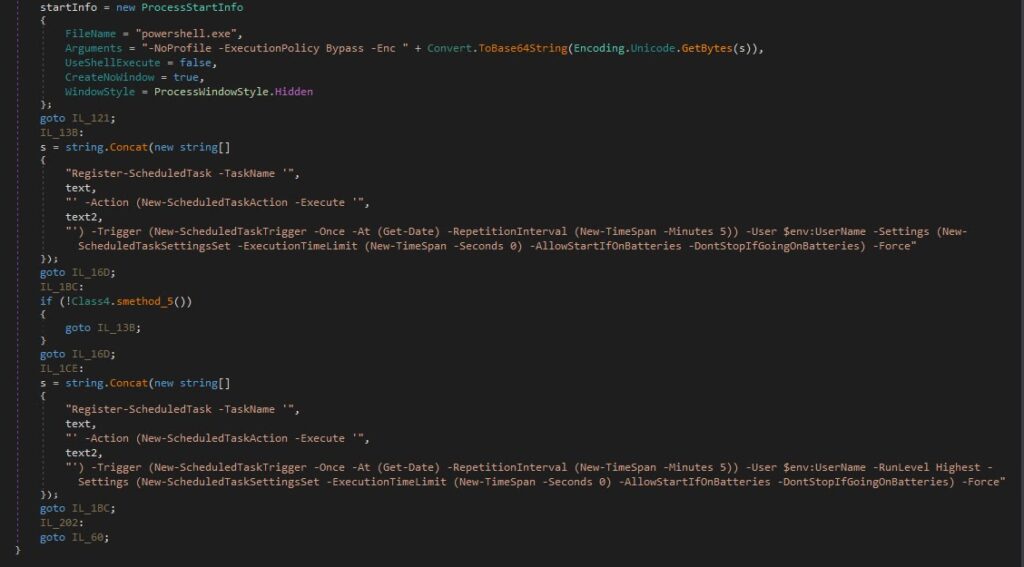
Researchers said the malware checks whether it runs in a sandbox or under debugging tools, then stops if it detects analysis. If it does not, it deletes parts of itself from disk, shows a decoy PDF to distract the victim, and creates persistence through the Windows Run registry. Later stages unpack another archive, launch an obfuscated Python script, and load Donut shellcode in memory, which then injects PureHVNC into SearchUI.exe.
PureHVNC itself is not new, but it remains dangerous. Malwarebytes describes it as a modular .NET RAT from the “Pure” malware family that can give attackers remote control of a device, steal browser and crypto wallet data, collect host details, extract information from apps such as Telegram and Foxmail, and install additional plugins. Broadcom’s protection bulletin also said recent attacks used fake business workflows on Google Forms to deliver PureHVNC, reinforcing Malwarebytes’ findings.
What makes this campaign more troubling is how well it fits everyday work behavior. Job seekers often fill out forms. Contractors download project briefs. Marketing and logistics teams exchange ZIP archives. That normal behavior gives attackers a cleaner social engineering path and reduces the odds that a victim will stop and question the file before opening it. This is the real story here: trusted cloud tools now help hide the first steps of malware delivery.
Quick breakdown
| Area | What researchers found | Why it matters |
|---|---|---|
| Initial lure | Fake Google Forms posing as job or business workflows | Trusted platform lowers suspicion |
| Delivery path | ZIP files on Dropbox, filedn.com, fshare.vn, and shortened URLs | Hides malicious payload behind normal file sharing |
| Malware family | PureHVNC RAT | Gives attackers broad remote access |
| Execution | DLL hijacking with malicious msimg32.dll | Helps malware blend in |
| Later stages | Obfuscated Python, Donut shellcode, injection into SearchUI.exe | Increases stealth and complexity |
| Persistence | Registry Run key and scheduled task creation | Helps attackers stay on the system |
How the infection chain works
- The victim receives or opens a Google Form dressed up as a job interview, project brief, or business document flow.
- The form leads to a ZIP file hosted on a file-sharing service or hidden behind a shortened link.
- The ZIP includes decoy business files plus a malicious DLL used for DLL hijacking.
- The malware checks for analysis tools, drops a decoy PDF, and sets persistence.
- A later stage runs obfuscated Python and Donut shellcode, then injects PureHVNC into SearchUI.exe.
What users and companies should do
- Verify any Google Form tied to a job offer, project request, or financial document before entering information or downloading files.
- Avoid ZIP archives delivered through unexpected forms, especially when the sender pushes urgency or uses shortened links.
- Confirm job offers and project requests through official company websites or known contacts instead of trusting branding inside a form.
- Watch for suspicious DLL loading, encoded PowerShell, Python execution from unusual folders, and process injection into SearchUI.exe.
- Keep endpoint detection tools current so they can catch staged loaders and memory-only payloads.
FAQ
PureHVNC is a modular .NET remote access trojan that can let attackers control a device, steal data, and add more malicious plugins later.
Because users trust them. A Google Form looks like a normal recruiting or business workflow, so it lowers suspicion and makes the next malicious step feel routine.
Not always. Malwarebytes said the campaign often starts through Google Forms and also spreads via LinkedIn, rather than relying only on standard phishing emails.
Look for suspicious DLL hijacking, PowerShell-based scheduled tasks, unexpected Python activity in ProgramData, and process injection into SearchUI.exe.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages