Fake IT support campaign uses customized Havoc C2 to breach organizations

A new social engineering campaign is using fake IT support calls and spam email to gain remote access, steal credentials, and deploy a customized version of the Havoc command-and-control framework inside victim networks. Huntress says it identified the activity across five partner organizations in February 2026 and observed one case where the attackers moved from the initial victim to nine additional endpoints in about 11 hours, a pace that suggests preparation for data theft, ransomware, or both.
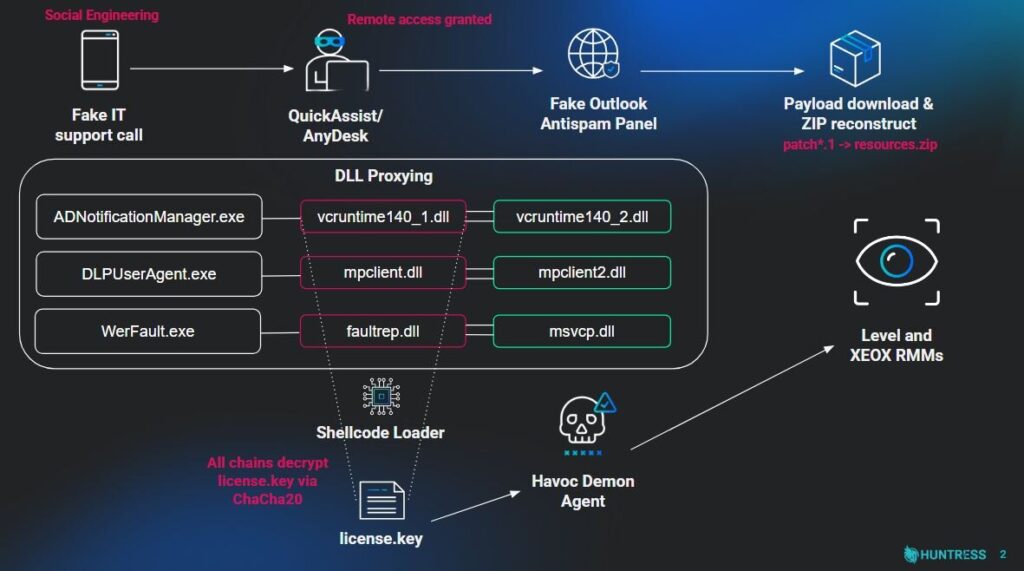
What makes this campaign dangerous is not one single malware file. It is the layered workflow. Huntress says the attackers first flooded targets with spam, then called them while posing as internal IT staff, and finally convinced them to grant remote access through Quick Assist or install tools such as AnyDesk. Once inside, the attackers used a fake Microsoft-themed page hosted on AWS to harvest credentials and trigger a malware chain that sideloaded malicious DLLs and launched customized Havoc Demon payloads.
The playbook strongly resembles techniques Microsoft tied to Black Basta operations in 2024. Microsoft said those attacks also relied on voice phishing, impersonation of IT support, abuse of Quick Assist, and follow-on deployment of malware and remote management tools. Huntress stops short of firmly attributing the 2026 activity to Black Basta, but it says the tradecraft is consistent with that earlier pattern.
How the attack unfolds
| Stage | What happens | Why it matters |
|---|---|---|
| Spam flood | Victims receive large volumes of junk email | Creates confusion and makes the “IT support” call seem believable. |
| Fake helpdesk call | Attacker poses as IT staff and asks for remote access | Social engineering creates the initial foothold without exploiting a software bug. |
| Remote access | Victim launches Quick Assist or installs a remote tool like AnyDesk | Gives the attacker hands-on access to the system. |
| Fake Microsoft page | Victim is sent to an AWS-hosted page that asks for an email address and password | Huntress says this step both steals credentials and makes the workflow look legitimate. |
| Malware execution | A legitimate binary sideloads a malicious DLL that launches Havoc Demon | Lets the attacker evade detection and establish command-and-control. |
| Lateral movement and persistence | Attackers spread to other machines and set scheduled tasks or deploy RMM tools | Keeps access alive and speeds movement toward data theft or ransomware. |
What Huntress found on infected systems
Huntress says the attackers used legitimate files such as ADNotificationManager.exe, DLPUserAgent.exe, or WerFault.exe to sideload malicious DLLs. One observed DLL, vcruntime140_1.dll, used added defense-evasion measures including control-flow obfuscation, timing-based delay loops, and syscall-related techniques such as Hell’s Gate and Halo’s Gate to reduce visibility to endpoint defenses. After deployment, the attackers created scheduled tasks to relaunch Havoc on reboot and, on some hosts, used legitimate remote monitoring and management tools such as Level RMM and XEOX instead of Havoc for backup persistence.
Huntress says the hands-on-keyboard work after the initial compromise was fairly direct. Once the first machine was under control, the attackers moved laterally, reused persistence techniques, and expanded their foothold quickly. The sophistication was concentrated in the entry and evasion phases, not in the later manual activity.
Why this campaign stands out
The biggest lesson is that modern intrusion chains no longer need an exploit to become serious. Microsoft said in 2024 that attackers were already abusing Quick Assist by pretending to be technical support, then dropping malware and ransomware after the user granted access. Huntress’s 2026 findings show that same approach has now evolved into a broader intrusion pipeline with customized Havoc payloads, credential harvesting, and diversified persistence.
This also shows how fast these operations move once the victim cooperates. Huntress’s example of nine additional endpoints in eleven hours means defenders do not get much time to debate whether an event looks serious. By the time the first alert is reviewed, the attacker may already be spreading.
What organizations should do now
- Train employees to distrust unsolicited calls from “IT support,” especially after spam or account issues. Microsoft says users should only accept Quick Assist help if they started the support interaction themselves.
- Consider blocking or removing Quick Assist and other remote management tools if your organization does not need them. Microsoft explicitly recommends that step for environments that do not rely on the tool.
- Watch for unusual launches of Quick Assist, AnyDesk, or similar tools on endpoints that do not normally use them. Huntress says those tools formed part of the access chain.
- Hunt for suspicious scheduled tasks, DLL sideloading, and legitimate binaries loading DLLs from strange paths. Huntress tied those behaviors directly to the malware chain.
- Review remote monitoring and management software exposure. CISA has repeatedly warned that attackers abuse RMM software in broader ransomware operations, including through unpatched or misused deployments.
FAQ
Havoc is a command-and-control framework attackers can use to maintain remote access and issue instructions on compromised hosts. Huntress says the threat actors in this campaign used customized Havoc Demon payloads, not just stock versions.
Not definitively. Huntress says the tactics are consistent with the playbook previously used in Black Basta-related social engineering campaigns, but it presents that as overlap in tradecraft rather than a firm public attribution.
Because the attacker needs the victim to grant remote access. Microsoft has already warned that threat actors misuse Quick Assist by pretending to be trusted technical support and then using that session to start a broader compromise.
User verification and remote-tool control. Microsoft says organizations should only allow Quick Assist sessions that users initiated themselves and should consider blocking the tool if it is not required. Huntress’s findings reinforce that advice.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages