Fancy Bear server exposure reveals stolen credentials, 2FA secrets, and European defense targets

A server linked to Fancy Bear appears to have exposed a rare inside view of an active cyberespionage operation aimed at government and military organizations in Europe. Researchers say the infrastructure hosted a full Roundcube exploitation toolkit, stolen mailbox data, credential material, and operational artifacts that map how the campaign worked.
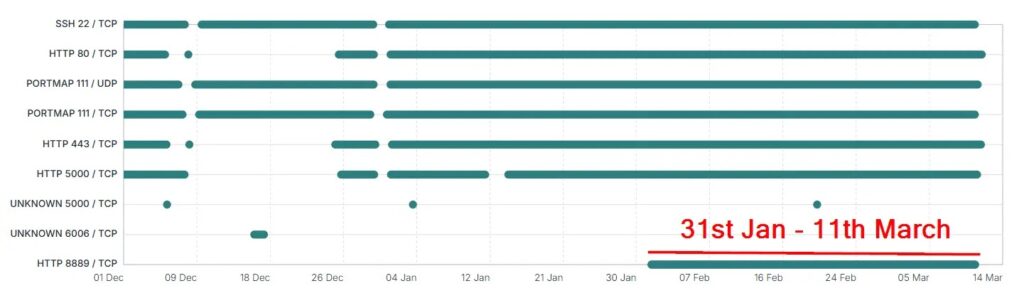
Hunt.io published its findings on March 11, 2026, after identifying an exposed open directory on IP address 203.161.50.145 in January. The company says the directory contained XSS payloads, a Flask-based command-and-control server, tooling for credential theft and mail forwarding, operator artifacts, and malware tied to compromises in Ukraine.
The operation has been linked to APT28, also known as Fancy Bear. The UK’s National Cyber Security Centre has previously attributed APT28 to Russia’s GRU Unit 26165, giving broader context to why the exposed infrastructure matters beyond a single intrusion set.
What makes this case stand out is the amount of victim data researchers say they found. Ctrl-Alt-Intel, which reported on a second exposed directory on the same server, says the infrastructure held more than 2,800 exfiltrated emails, more than 240 stolen credential sets that included passwords and TOTP data, more than 140 silent forwarding rules, and over 11,500 harvested contact addresses.
What the exposed server reveals
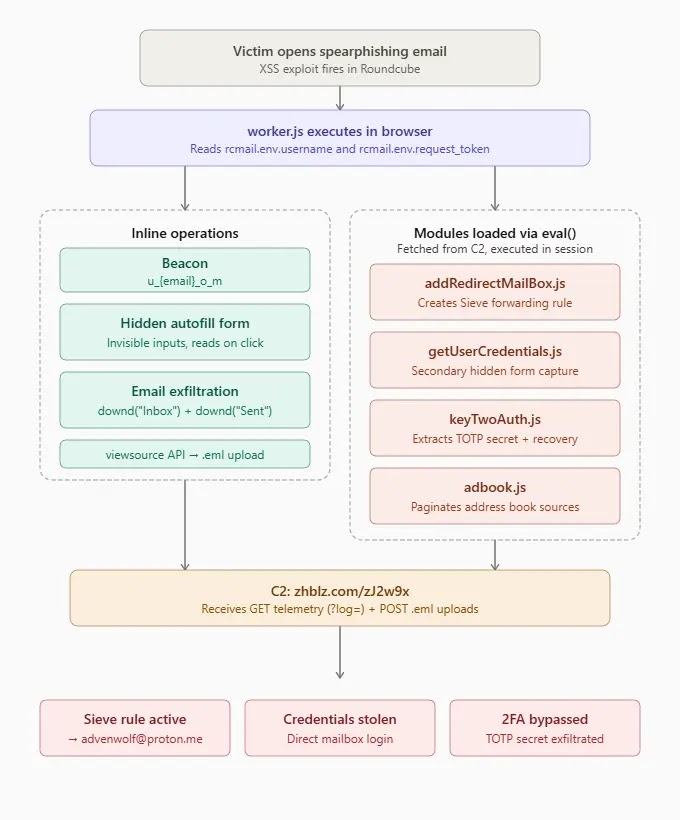
The Hunt.io report says the toolkit focused on Roundcube webmail and supported credential harvesting, persistent mail forwarding, bulk email theft, address book collection, and two-factor secret extraction. It also tied the infrastructure to the domain zhblz.com, which resolved to the same IP and had been registered through Namecheap in July 2024.
Ctrl-Alt-Intel says the same server exposed a second directory that included command-and-control source code, extra JavaScript payloads, and campaign telemetry. Based on those artifacts, the researchers say victims included organizations in Ukraine, Romania, Bulgaria, Greece, Serbia, and North Macedonia, with contact data that touched four NATO member states.
That victim pattern points to intelligence collection, not broad cybercrime. The reporting centers on defense, government, and public-sector mailboxes, especially in countries connected to Ukraine and regional security cooperation.
How the attackers got past two-factor authentication
One of the more serious parts of the campaign involved theft of TOTP secrets from already authenticated webmail sessions. Hunt.io says the toolkit supported 2FA secret extraction, while Ctrl-Alt-Intel identified a JavaScript module called keyTwoAuth.js that allegedly pulled TOTP secrets and recovery codes from Roundcube sessions using the twofactorgauthenticator plugin.
If attackers steal both the account password and the TOTP seed, they no longer need the victim’s phone to generate future login codes. That turns two-factor authentication into a weaker barrier because the attacker can produce valid one-time codes on demand. This is an inference based on how TOTP works and on the researchers’ claim that the stolen data included both passwords and TOTP secrets.
The underlying access path appears tied to Roundcube XSS exploitation. NVD says CVE-2023-43770 is a cross-site scripting flaw in Roundcube that affects versions before 1.4.14, 1.5.4, and 1.6.3, and Hunt.io says the toolkit used Roundcube-focused exploitation and credential theft workflows.
Why this exposure matters now
This leak gives defenders unusually useful insight into the attackers’ workflow. Instead of relying only on victim-side artifacts, researchers could examine live infrastructure, payload logic, domains, and stolen-data handling on the server itself. That kind of visibility helps incident responders validate indicators, understand the campaign’s priorities, and look for the same tradecraft in other environments.
It also shows how long an espionage server can stay useful when no one disrupts it. Hunt.io says certificate history suggested the infrastructure had operated since at least early 2025, and the same IP resolved the main command domain and related subdomains used in the campaign.
Key details at a glance
| Item | Details |
|---|---|
| Threat group | APT28 / Fancy Bear |
| Main target type | Government and military webmail |
| Primary platform | Roundcube |
| Exposed IP | 203.161.50.145 |
| Main domain | zhblz.com |
| Reported capabilities | Credential theft, mail forwarding, email exfiltration, address book theft, 2FA secret extraction |
| Relevant flaw | CVE-2023-43770 |
| Affected Roundcube versions | Before 1.4.14, 1.5.4, and 1.6.3 |
What organizations should do
- Patch Roundcube if any exposed system still runs versions affected by CVE-2023-43770.
- Rotate passwords and re-enroll TOTP secrets for accounts that may have touched compromised webmail infrastructure.
- Review Sieve and mailbox forwarding rules for suspicious entries.
- Block known malicious infrastructure tied to the campaign, including domains and IPs named in the research.
- Hunt for XSS artifacts, unusual session behavior, and unexplained mailbox exports on webmail servers.
FAQ
Hunt.io uses that name for a Roundcube-focused exploitation toolkit tied to APT28 activity against Ukrainian government targets.
The available reporting says yes. Hunt.io said the toolkit supported 2FA secret extraction, and Ctrl-Alt-Intel said the exposed data included TOTP secrets and recovery data from affected accounts.
They suggest the attackers cared about defense and diplomatic networks, not random victims. The reports describe contacts and victims tied to several European military and government entities.
Patch vulnerable Roundcube systems and rotate authentication material for any accounts that may have been exposed. Patching alone does not fully solve the problem if attackers already stole passwords or TOTP seeds.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages