FBI asks victims of malware-laced Steam games to come forward

The FBI is asking gamers who installed several malicious Steam titles to contact the bureau as part of an ongoing malware investigation. The agency says it is trying to identify potential victims who installed infected games between May 2024 and January 2026.
The case matters because the affected games were not just buggy or deceptive. The FBI’s victim notice and follow-up reporting indicate investigators are focused on stolen cryptocurrency, hijacked accounts, and other losses linked to malware hidden inside games distributed through Steam.
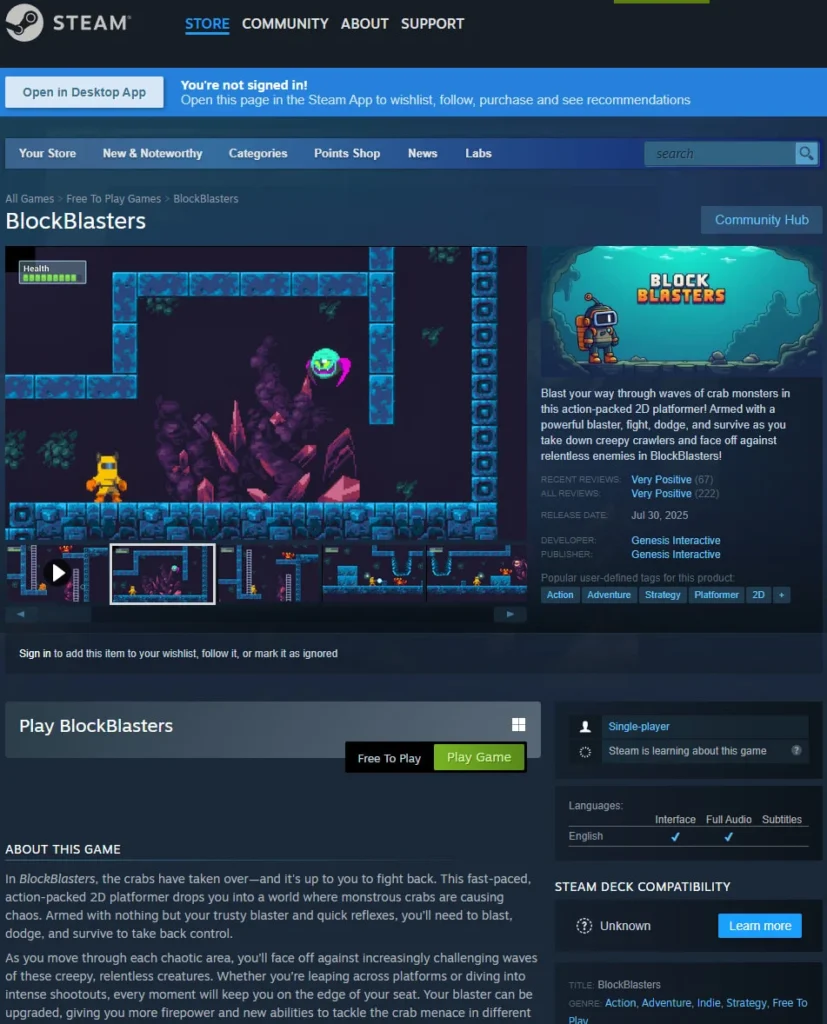
The FBI notice names these games in connection with the investigation: BlockBlasters, Chemia, Dashverse or DashFPS, Lampy, Lunara, PirateFi, and Tokenova. Anyone who believes they or their minor dependent installed one of them and suffered harm can submit information through the FBI’s victim intake process.
What the FBI is investigating
According to the FBI’s Seattle Division, the bureau believes a threat actor primarily targeted users during the period from May 2024 to January 2026. The FBI is collecting reports from people who may have installed one of the listed Steam games and later experienced theft, account compromise, or related suspicious activity.
The victim form shows what investigators care about most. It asks about cryptocurrency transactions, stolen funds, compromised online accounts, and screenshots of communications with people who promoted the games. That suggests the bureau is trying to map both the victims and the distribution chain behind the malware campaign. This is an inference based on the questions shown in the FBI form.
The Steam games named by the FBI
| Game named in the FBI notice | Status |
|---|---|
| BlockBlasters | Under FBI victim outreach |
| Chemia | Under FBI victim outreach |
| Dashverse / DashFPS | Under FBI victim outreach |
| Lampy | Under FBI victim outreach |
| Lunara | Under FBI victim outreach |
| PirateFi | Under FBI victim outreach |
| Tokenova | Under FBI victim outreach |
Source: FBI victim information page and follow-up reporting.
Why this case stands out
Steam usually carries a reputation as a safer distribution platform than random download sites, which is why this investigation will likely get attention well beyond the usual security audience. In at least some of the cases tied to recent reporting, the games appeared legitimate enough to attract downloads before the malware activity became public.
One of the best known cases involved BlockBlasters, a game later linked by security researchers and media reports to crypto theft affecting hundreds of accounts. Another involved PirateFi, which Valve removed from Steam after warning users that malicious files may have run on their PCs.
What affected users should do now
- Check whether you installed any of the games named in the FBI notice.
- Review crypto wallets, exchange accounts, email accounts, Steam credentials, and browser-stored passwords for suspicious activity. This is practical guidance based on the types of harm described in the FBI victim form and past reporting on the malware.
- Change passwords on important accounts, especially if you reused them.
- Run a reputable antivirus or antimalware scan.
- Consider a full operating system reinstall if you launched one of the known malicious games, especially in cases like PirateFi where users were warned that malicious files may have executed.
- Submit a report to the FBI if you think you were affected.
What this means for Steam users
This investigation suggests the real risk was not limited to one game. The FBI’s wording points to a broader campaign that stretched across many months and multiple titles. That pattern raises difficult questions about how long malicious content can stay live on large game platforms before users or researchers catch it. This is an inference based on the timeline and number of games in the FBI notice.
It also shows why gamers should treat lesser-known free titles with more caution, especially when those games are pushed through unusual promotion channels or tied to crypto-related offers. That does not mean every small Steam game is risky, but it does mean platform trust alone is not enough protection. This is an inference drawn from the attack pattern described in the investigation and reported cases.
FAQ
No public FBI notice says Steam itself was breached. The bureau says it is seeking victims who installed Steam games embedded with malware.
The notice lists BlockBlasters, Chemia, Dashverse or DashFPS, Lampy, Lunara, PirateFi, and Tokenova.
The victim form points to crypto theft, stolen funds, and compromised accounts.
They should secure accounts and devices, then submit information through the FBI’s official victim reporting process.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages