FBI disrupts Russian router hijacking operation that hit thousands of devices

The FBI and the U.S. Justice Department say they have disrupted a Russian cyber operation that hijacked vulnerable small office and home office routers and used them for espionage. The campaign relied on compromised routers to reroute internet traffic through attacker-controlled DNS servers, helping Russian military intelligence steal passwords, authentication tokens, emails, and other sensitive data.
The takedown, announced on April 7, 2026, targeted infrastructure tied to GRU Military Unit 26165, the Russian state hacking unit widely known as APT28, Fancy Bear, Sofacy, Forest Blizzard, and Sednit. U.S. officials said the operation neutralized the American portion of the network and affected routers in more than 23 states.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
According to the Justice Department, the attackers had been exploiting known router vulnerabilities since at least 2024, stealing credentials for thousands of TP-Link routers worldwide. After gaining access, they changed DNS settings so selected victims could be redirected to fake services that looked legitimate, including Microsoft Outlook Web Access.
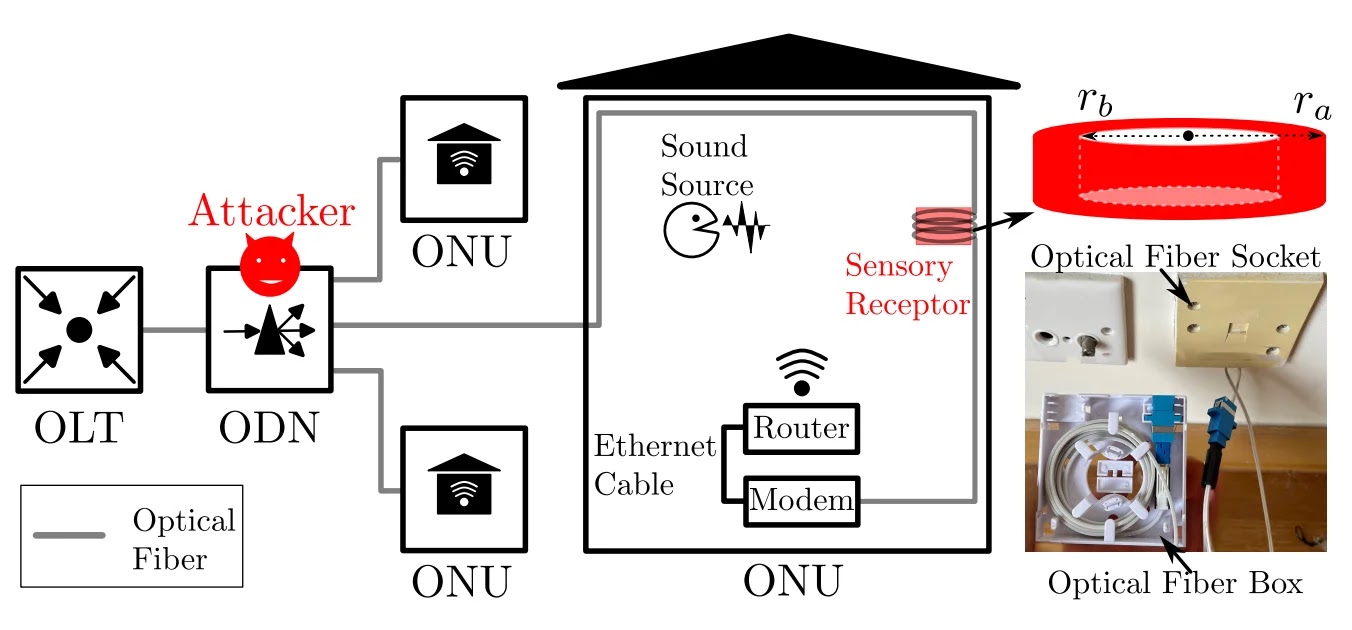
How the attack worked
Officials said the initial router compromises were broad and opportunistic. After that first wave, the attackers filtered traffic to identify people and organizations worth spying on, especially in military, government, and critical infrastructure sectors.
For those selected targets, the malicious DNS servers returned fake records for real domains. That let the hackers stage adversary-in-the-middle attacks, intercept traffic, and harvest credentials and other sensitive information from devices connected to the infected networks.
The UK’s National Cyber Security Centre described the same campaign as a DNS hijacking operation that enabled theft of passwords and authentication tokens. Its alert also said the attackers used compromised edge devices as a covert path into higher-value networks.
What the hackers were after
| Targeted asset | What attackers could steal | Why it mattered |
|---|---|---|
| Web logins | Passwords and session data | Account takeover |
| Email services | Emails and authentication tokens | Espionage and persistence |
| Government and military traffic | Sensitive communications | Intelligence collection |
| Critical infrastructure networks | Credentials and browsing data | Follow-on intrusion risk |
What the FBI did
The Justice Department said the FBI obtained court authorization and sent a series of commands to compromised routers in the United States. Those commands collected evidence, removed the malicious DNS settings, restored legitimate ISP resolvers, and blocked the attackers from using the original access path.
Federal officials said the government tested the operation on affected TP-Link hardware and firmware before deployment. According to the DOJ, the process did not damage normal router functionality and did not collect the legitimate users’ content information.
The FBI is now working with internet service providers to notify affected users. People who think their router was compromised can contact their local FBI field office or file a report through the Internet Crime Complaint Center.
What router owners should do now
The main advice from U.S. and allied agencies is straightforward. Replace end-of-life routers, update firmware, verify DNS settings, and make sure remote management is not exposed to the public internet.
The IC3 public advisory says Russian GRU actors used vulnerable routers worldwide to intercept data that users normally expect SSL or TLS to protect. That warning makes this more than a router issue. Any laptop, phone, or tablet that inherited the rogue DNS settings from an infected router could also sit at risk.
The broader lesson is simple. Old or poorly secured routers can turn into stealth infrastructure for state-backed attacks, even when the real targets sit somewhere else on the network.
Remediation checklist
- Replace any router that has reached end of life or no longer gets security updates
- Install the latest firmware available from the manufacturer
- Check the router’s DNS settings and confirm they point to legitimate resolvers
- Review firewall and remote management settings so outsiders cannot reach the admin interface
- Report suspected compromise to IC3 or the FBI
FAQ
It was the FBI-led, court-authorized disruption of a GRU-controlled router network used for DNS hijacking and espionage. The DOJ announced it on April 7, 2026.
U.S. officials attributed it to Russia’s GRU Military Unit 26165, also tracked as APT28, Fancy Bear, Sofacy, Forest Blizzard, and Sednit.
The DOJ said the campaign involved thousands of compromised TP-Link routers worldwide. UK and other reporting around the joint warnings also pointed to vulnerable edge routers used in small office and home office environments.
Passwords, authentication tokens, emails, and other sensitive information moving through the compromised network.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages