FBI says Iran-linked Handala hackers used Telegram as malware C2 in attacks on dissidents and journalists

The FBI has warned that Iran-linked hackers used Telegram as command-and-control infrastructure in malware attacks targeting Iranian dissidents, journalists critical of Tehran, and other opposition groups worldwide. In a FLASH alert published on March 20, the bureau said the activity ties back to cyber actors working on behalf of Iran’s Ministry of Intelligence and Security, or MOIS.
According to the FBI, the malware campaign dates back to at least the fall of 2023 and focused on Windows devices. The bureau said the attacks led to intelligence collection, data leaks, and reputational harm, and warned that the same tooling could be used against any person of interest to Iran.
The alert matters because it shows how a mainstream messaging platform can blend into normal traffic while quietly serving as a control channel for spyware-style malware. In this case, the FBI said stage-two malware used Telegram bots for bidirectional communication with compromised devices, allowing attackers to exfiltrate screenshots and files from victims’ systems.
What the FBI says happened
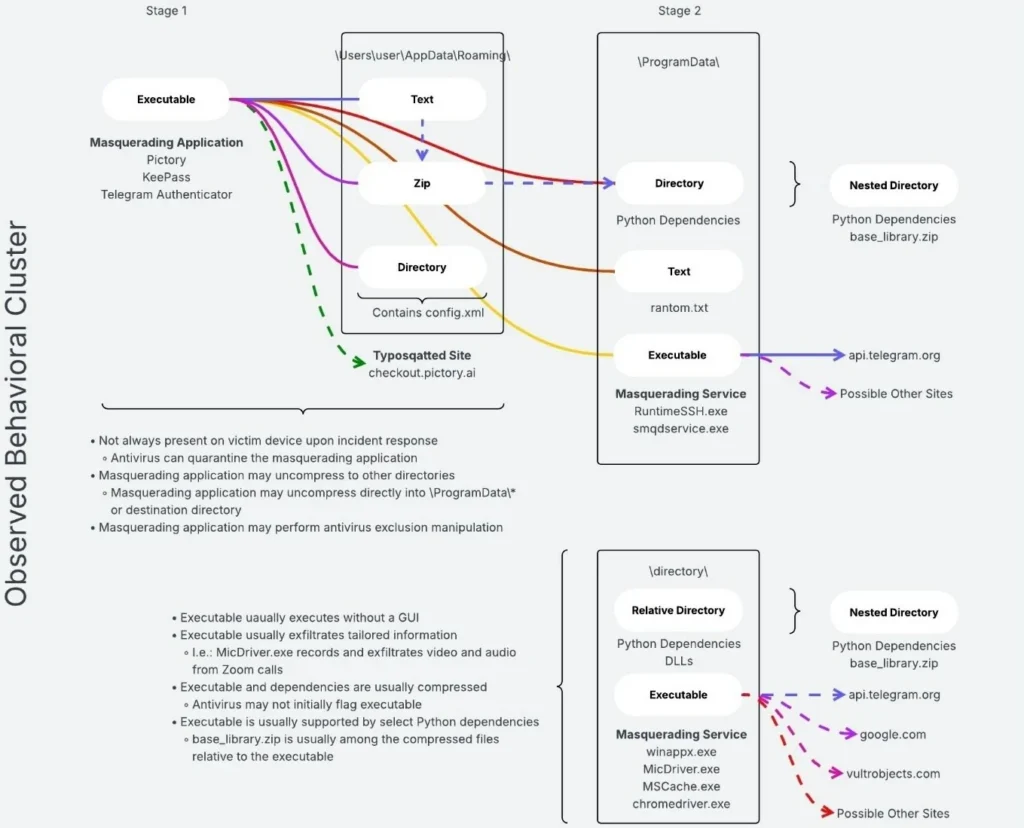
The FBI said the attackers relied on social engineering to deliver the malware. In multiple cases, they contacted victims through messaging apps, posed as known contacts or platform support staff, and then convinced targets to open malicious files. The bureau said the first-stage malware often matched the victim’s habits and interests, which suggests the attackers conducted reconnaissance before making contact.
Once opened, the initial file launched a persistent implant on the Windows machine. The FBI said some samples masqueraded as well-known apps or services, including Telegram, KeePass, WhatsApp, and Pictory. The second stage then connected the infected device to Telegram-based infrastructure that enabled remote access and data theft.
The bureau also described follow-on malware with added surveillance functions. In one example, malware in a file named MicDriver.zip included logic to record screen and audio while a Zoom session was active. Other malware families tied to the campaign could capture caches, compress files with passwords, delete data, and stage stolen material for transfer.
How Handala fits into the campaign
The FBI linked this activity to Handala Hack and said the group is tied to MOIS. In the alert, the bureau said Handala claimed responsibility in July 2025 for a hack-and-leak campaign targeting people who voiced views that conflicted with the Iranian government’s rhetoric. The FBI further said some of the material Handala posted online likely came from the same ongoing malware campaign aimed at dissidents.
A separate Justice Department announcement on March 19 adds more context. DOJ said U.S. authorities seized four domains used by MOIS as part of cyber-enabled psychological operations and transnational repression efforts: Justicehomeland[.]org, Handala-Hack[.]to, Karmabelow80[.]org, and Handala-Redwanted[.]to. The department said those sites were used to claim credit for hacks, publish stolen data, and threaten dissidents, journalists, and other targets.
DOJ also said Handala-Hack[.]to claimed credit for a March 2026 destructive malware attack against a U.S.-based multinational medical technologies firm. The release stated that investigators tied the seized domains together through shared leak sites, Iranian IP ranges, and a common operational playbook.
Why Telegram showed up here
The FBI did not accuse Telegram itself of aiding the operation. Instead, the alert describes Telegram as infrastructure the attackers abused to manage malware on victim machines. That distinction matters, because threat actors often use legitimate services to hide malicious traffic among routine network activity.
Telegram pushed back on any suggestion that the platform offers a special advantage for attackers. In a statement reported by BleepingComputer, a company spokesperson said bad actors can use any available channel to control malware, including other messengers, email, or direct web connections, and added that moderators routinely remove accounts found to be involved with malware.
At a glance
| Item | Key detail |
|---|---|
| Threat actor | Iran MOIS cyber actors, according to the FBI |
| Linked groups | Handala Hack and Homeland Justice |
| Target profile | Iranian dissidents, anti-regime journalists, and opposition groups |
| First known timeframe | At least fall 2023 |
| Platform abused | Telegram as command-and-control |
| Main victim systems | Windows devices |
| Data targeted | Screenshots, files, audio, screen recordings, caches |
| Recent U.S. action | Seizure of four domains on March 19, 2026 |
Malware examples named by the FBI
- Telegram_Authenticator.exe
- WhatssApp.exe
- KeePass.exe
- Pictory_premium_ver9.0.4.exe
- MicDriver.exe / MicDriver.dll
- Winappx.exe
- MsCache.exe
- RuntimeSSH.exe
- smqdservice.exe
What organizations should do now
- Be cautious with unexpected messages, even from known contacts.
- Do not open transferred files unless you verify the sender and the reason.
- Keep Windows and installed software fully updated.
- Download apps only from official vendor sites or trusted stores.
- Run antivirus or anti-malware tools and keep them enabled.
- Use strong, unique passwords and turn on multi-factor authentication.
- Report suspicious activity to the FBI or IC3 if compromise is suspected.
FAQ
The FBI warned that Iran-linked cyber actors used Telegram bots as malware command-and-control infrastructure in attacks on dissidents, journalists, and opposition groups.
No. The alert says attackers abused Telegram as a communication channel for malware control and data exfiltration.
The bureau attributed the campaign to actors working on behalf of Iran’s Ministry of Intelligence and Security and linked the activity to Handala Hack and Homeland Justice.
The FBI said the malware could exfiltrate screenshots, files, screen recordings, audio, and cached data from infected Windows systems.
On March 19, 2026, the Justice Department announced the seizure of four domains tied to the operation.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages