Firefox 148 Introduces Sanitizer API for XSS Protection

Firefox 148 brings the new Sanitizer API, the first browser implementation to help developers block cross-site scripting (XSS) attacks easily. This standard tool cleans dangerous HTML before it reaches web pages. Developers can now replace risky methods with safe ones in just a few lines of code.
XSS ranks high among web threats. Attackers inject scripts through comments or forms. These scripts steal sessions or data. The API stops this at the source. It fits into current workflows unlike older fixes.
Mozilla developed it after years of standards work. Content Security Policy helped before but required full site overhauls. Many skipped it. Sanitizer API works line-by-line for quick wins.
How Sanitizer API Works
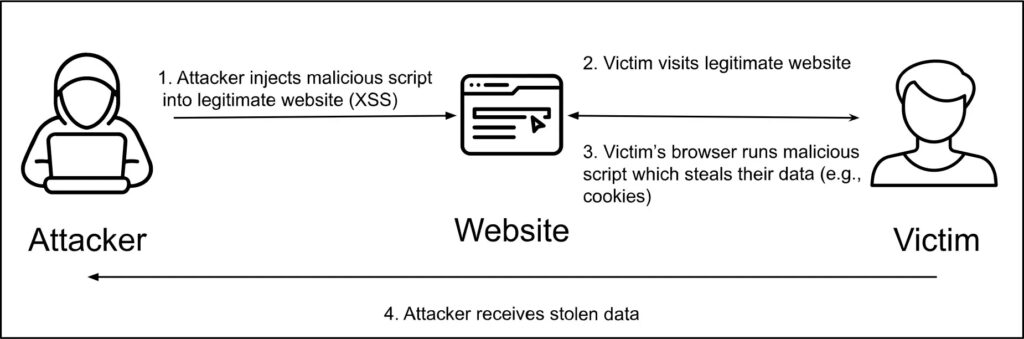
The setHTML() method forms its core. It filters user content on insertion. Harmful tags disappear. Safe text remains.
Bad input like <h1>Click</h1><img src=x onerror=alert('XSS')> becomes <h1>Click</h1>. Scripts and risky elements go.
Customize rules for needs. Blogs allow images. Forums block forms. Test in Mozilla’s playground tool.
| Feature | Old innerHTML Risk | New setHTML Benefit |
|---|---|---|
| Script Execution | Runs malicious JS directly | Blocks all scripts by default |
| Element Filtering | No built-in checks | Removes or escapes bad elements |
| Customization | Manual parsing needed | Config object for rules |
| Browser Support | Universal but unsafe | Firefox 148 first, others soon |
Mozilla confirms: “setHTML provides stronger XSS protection with minimal code changes.” Details at Mozilla Hacks Blog.
Pairing with Other Defenses
Combine with Trusted Types from Firefox 148. It blocks unsafe strings early. CSP limits loaded resources next.
Layered setup covers all angles. Sites run faster too. No extra parsing slows pages.
Developers save review hours. Users avoid fake alerts or theft.
Key Steps to Implement
Add protection this way:
- Create sanitizer:
const sanitizer = new Sanitizer(); - Insert safe HTML:
element.setHTML(dirtyHTML, sanitizerConfig); - Test configs online.
- Add CSP headers.
- Find old innerHTML calls.
User-content sites win big. Think forums and apps. Deploy in phases.
FAQ
Web standard cleans HTML to stop XSS by default.
setHTML removes scripts. innerHTML executes them.
148 and newer. Update today.
Yes. Define allowed elements in config.
Yes. Both create full defense.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages