Google API Keys Expose Private Gemini Data and Bills After Silent Privilege Escalation

Legacy Google API keys in public web code now access sensitive Gemini AI endpoints without warning. These keys, meant for Maps or Firebase, gain power when admins enable Gemini on the same project. Attackers grab private files, cached data, and rack up bills.
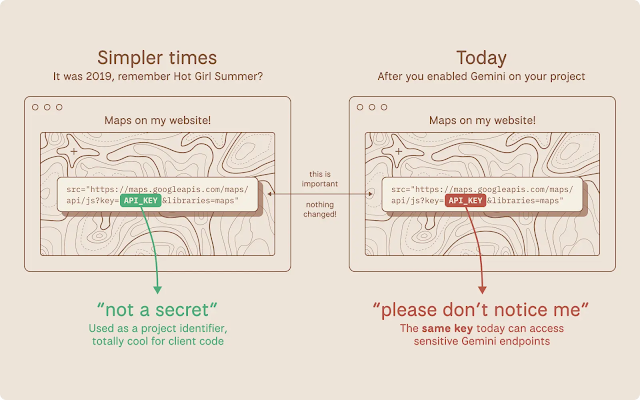
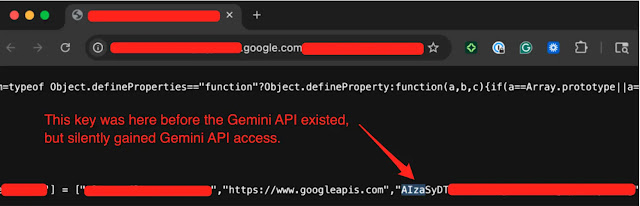
Google once told developers to embed AIza… keys openly in JavaScript. Firebase docs called them non-secrets for billing. Maps guides said paste them publicly. That advice dates back years. No alerts come when Gemini activates. Old keys inherit access instantly.
Truffle calls it privilege escalation via CWE-1188 and CWE-269. Defaults set keys to unrestricted. They hit every enabled API, including Gemini’s /files/ and /cachedContents/. No notifications flag the change.
Attackers need no hacks. They scrape a site for the key. Query https://generativelanguage.googleapis.com/v1beta/files?key=$API_KEY. A 200 OK unlocks:
- Uploaded datasets and docs.
- Stored AI context.
- Quota burns costing thousands daily.
Truffle scanned November 2025 Common Crawl data. They found 2,863 live vulnerable keys. Hits included banks, security firms, recruiters, and Google sites. One key from a Google page since 2023 worked on Gemini.
Exposed Gemini Endpoints
| Endpoint | Risks Accessed |
|---|---|
| /v1beta/files | Private uploads, datasets, documents |
| /cachedContents | Stored AI context and history |
| Model inference | Billable queries, quota exhaustion |
Google plans scoped defaults for AI keys, auto-blocks on leaks, and alerts. Fixes roll out per their security update. Root issues persist as of February 27.
Immediate Remediation Steps
- Audit GCP projects: Check APIs & Services for Generative Language API.
- Review keys: Flag unrestricted or Gemini-enabled ones.
- Hunt exposures: Scan JS, repos, pipelines for AIza… strings.
- Rotate now: Hit old public keys first.
- Scan code: Use TruffleHog with
trufflehog filesystem /path --only-verified.
Block public keys in AI projects. Monitor bills for spikes.
Google API key leaks, Gemini privilege escalation, and AI credential risks affect Maps, Firebase users. Secure them before attackers drain quotas in 2026.
FAQ
Enabling Gemini on a project auto-grants access to all keys.
Steal files/caches, burn quotas for bills, disrupt services.
Truffle found 2,863 in public web scans from 2025 data.
Scoped keys and alerts incoming.
List in GCP console. Rotate unrestricted ones. Scan with TruffleHog.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages