Google Disrupts Chinese Hackers Targeting 53 Telecom and Government Entities

Google Threat Intelligence disrupted a Chinese state-linked hacking group called UNC2814. The group breached 53 telecom providers and government bodies across 42 countries. This cyber espionage ran for nearly a decade until coordinated action on February 18, 2026.
Mandiant and Google Cloud uncovered the operation. They severed the hackers’ access and shared threat details. Victims span Africa, Asia, Europe, and the Americas. The campaign focused on sensitive communication networks.
The GRIDTIDE Backdoor
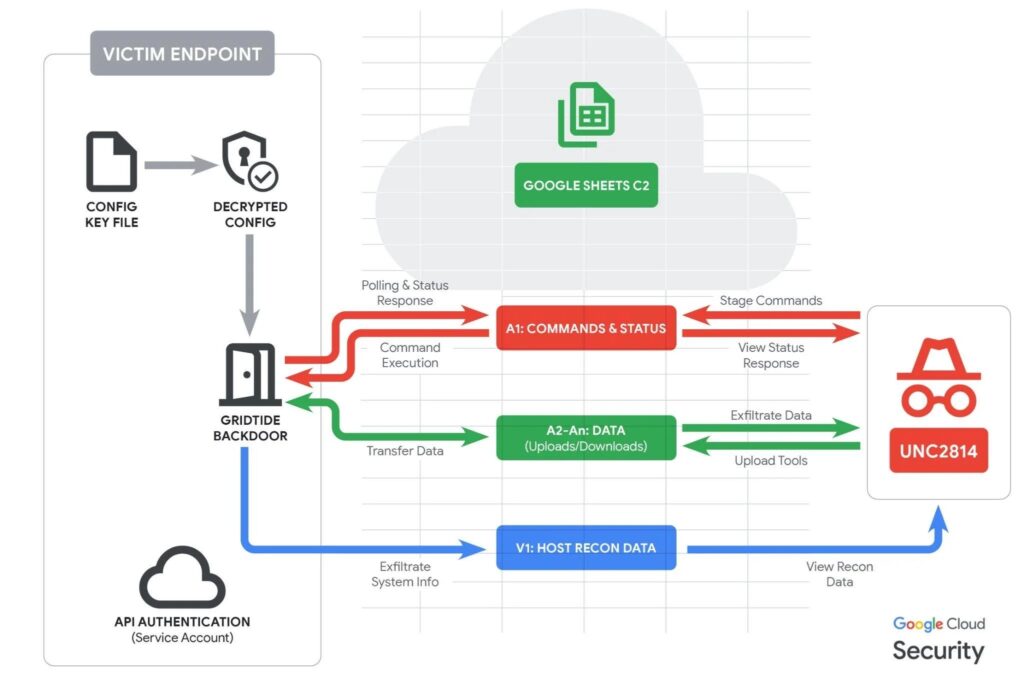
UNC2814 used a new backdoor named GRIDTIDE. It hides commands in Google Sheets cells, blending with normal cloud traffic. This method evades typical network defenses.
Analysts spotted it on a customer’s CentOS server. A binary called xapt mimicked a system tool and ran root commands. The malware registers as a systemd service to persist.
It uses AES-128 encryption for Google Drive configs. Commands flow through cell A1. Results go back in Base64 encoding. A SoftEther VPN adds a backup channel since 2018.
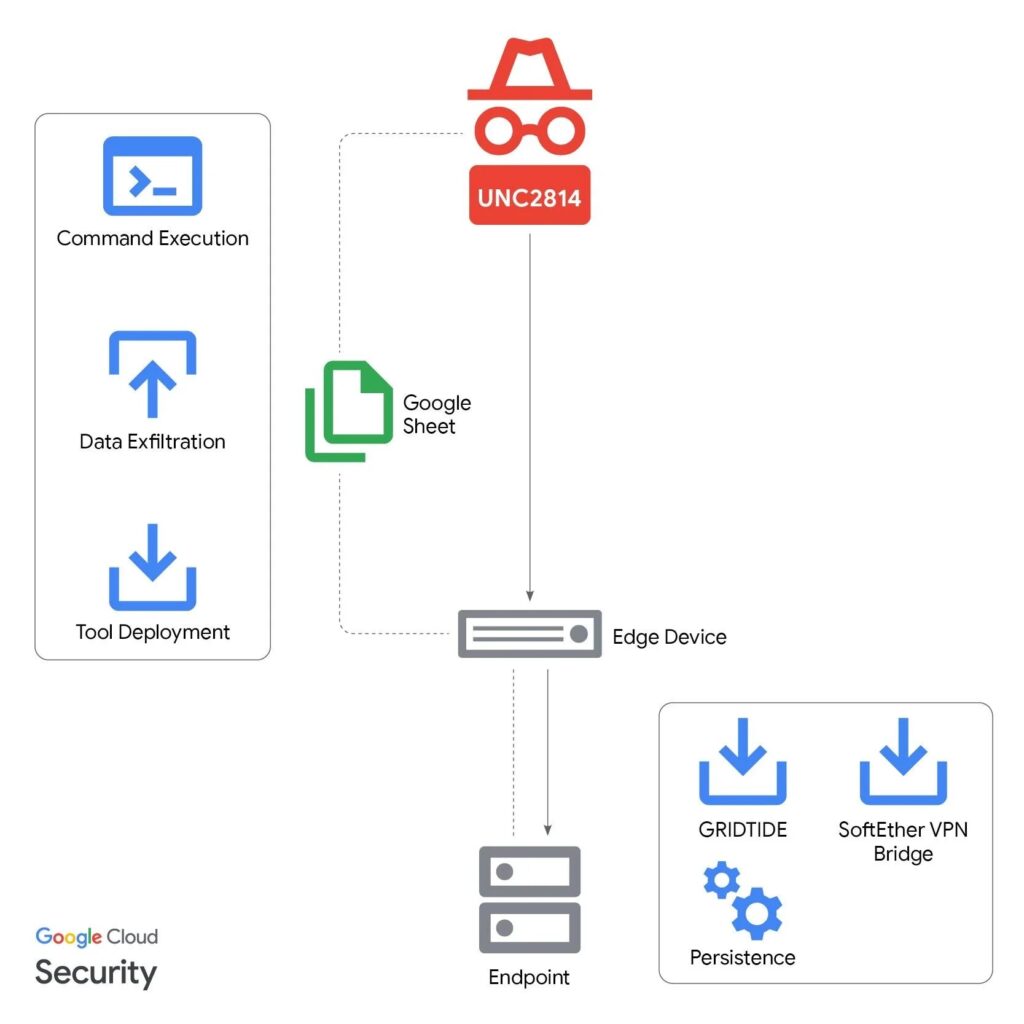
Attack Techniques
Hackers entered via internet-facing web servers and edge devices. They used built-in system tools for lateral movement. No new malware dropped to avoid alerts.
Targets held personal data like names, phone numbers, and voter records. This matches Chinese intelligence goals. The group shows no link to Salt Typhoon.
Google Cloud Blog states: “We disrupted GRIDTIDE, a global espionage campaign by UNC2814.”
Victim Scope and Impact
| Category | Count | Regions Affected |
|---|---|---|
| Confirmed Victims | 53 | 42 countries (4 continents) |
| Suspected Infections | 20+ | Africa, Asia, Americas |
| Primary Targets | Telecom, Government | Communication infrastructure |
Detection Indicators
Monitor these signs of compromise.
- Outbound HTTPS to Google Sheets API with batchClear or batchUpdate.
- Systemd services in /etc/systemd/system/xapt.service.
- Binaries in /var/tmp/xapt running nohup.
- Non-browser processes using valueRenderOption=FORMULA.
- SoftEther VPN Bridge on Linux servers.
Response Steps
- Apply GTIG YARA rules for GRIDTIDE detection.
- Scan logs for listed IOCs from Google.
- Check web servers and edge devices for breaches.
- Block unusual Google Sheets API calls.
- Hunt for living-off-the-land binaries.
Mandiant noted suspicious xapt behavior first. Google tracked UNC2814 since 2017.
FAQ
Chinese-linked espionage group behind GRIDTIDE campaign targeting telecoms.
Backdoor uses Google Sheets for C2, AES-encrypted, with Base64 commands.
53 confirmed across 42 countries, plus 20+ suspected.
February 18, 2026, via GTIG and Mandiant action.
PII like names, phones, IDs, voter records.
Monitor Sheets API calls, xapt binaries, SoftEther VPN.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages