GTFire Phishing Campaign Abuses Google Firebase and Translate for Credential Theft

GTFire phishing scheme uses Google Translate and Firebase to steal login credentials worldwide. Attackers hide behind trusted Google domains to bypass email filters and security gateways. Victims enter details on fake brand pages, then get redirected to real sites unaware of the theft.
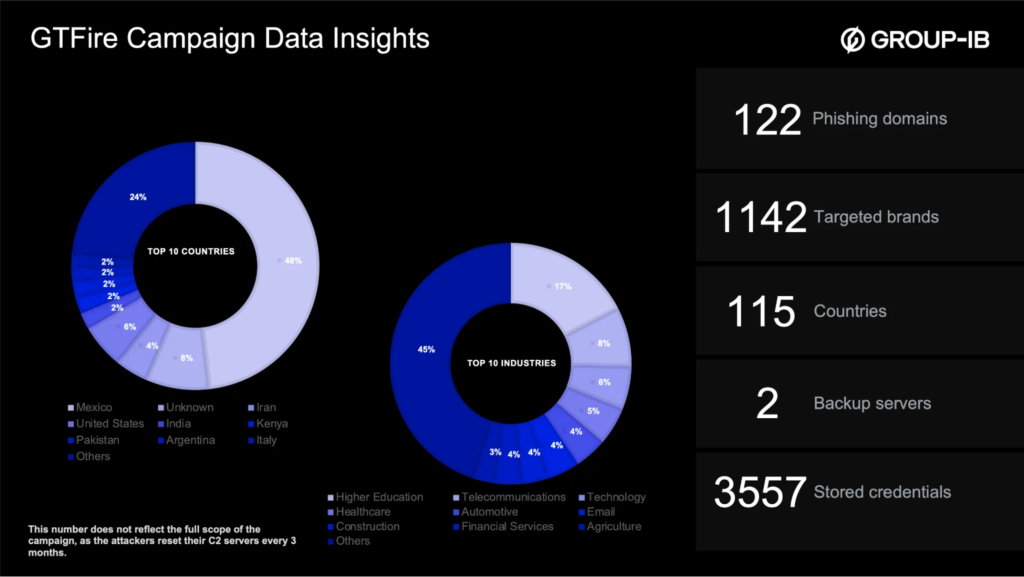
Group-IB uncovered this operation targeting over 1,000 organizations across 100+ countries. Servers exposed thousands of stolen credentials from 200+ industries. Mexico tops the list with 385 victims in manufacturing, education, and government sectors. The US follows with 101 cases.
Phishers reuse templates for brands with small tweaks. Pages collect credentials in steps. Data sorts by date, language, and service on central servers. Over 120 domains use random names for quick swaps.
Links start with translate.goog URLs. These relay through Google’s proxy to Firebase *.web.app phishing sites. Legit Google domains dodge blocks. Pages mimic brands perfectly with dynamic logos.
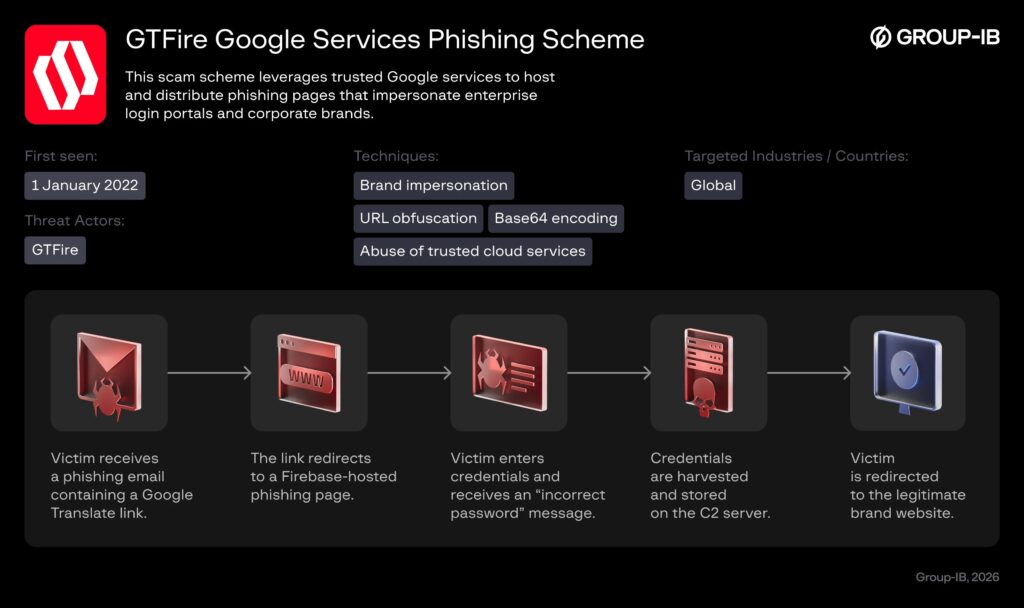
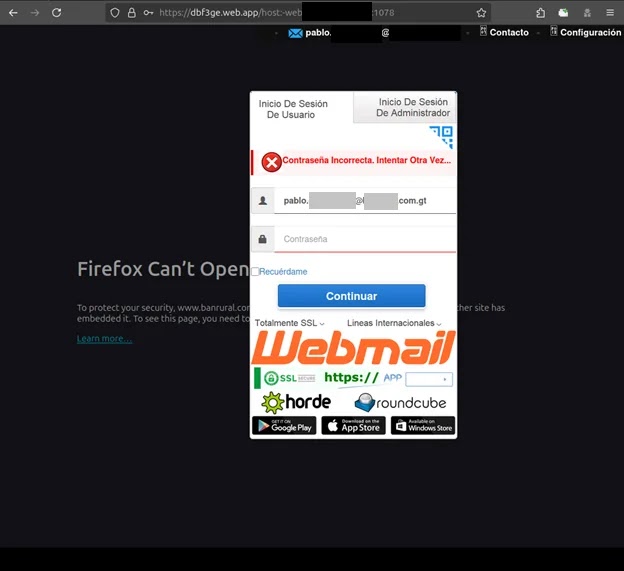
Victims type credentials. Pages show fake “wrong password” errors to grab second tries too. Data hits C2 servers via GET requests with Base64 passwords plus country and browser info. LiteSpeed servers run All-in-1.php scripts.
Victim Distribution
| Country | Victims | Top Sectors |
|---|---|---|
| Mexico | 385 | Manufacturing, Education, Government |
| USA | 101 | Various |
| Spain | 67 | Various |
| India | 54 | Various |
| Argentina | 50 | Various |
Redirects to real sites delay detection. Traditional filters miss Google-hosted phishing. Rapid subdomain rotation beats blocklists.
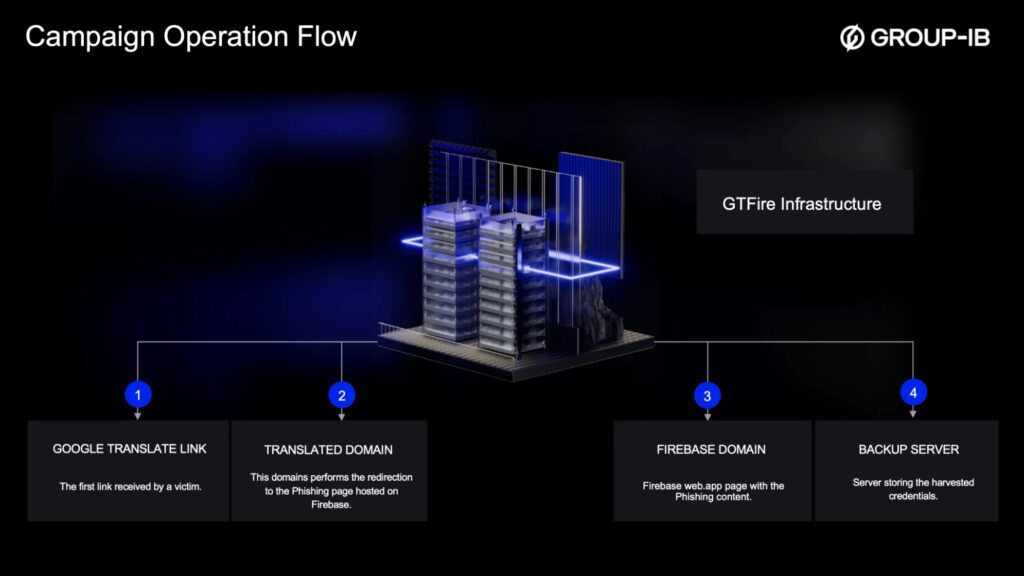
Attack Flow
- Phishing email with translate.goog link.
- Routes to Firebase *.web.app fake login.
- Victim submits credentials twice via error loop.
- Data to C2: jnhwzs.fyi, gnpnia.lat.
- Silent redirect to legit brand site.
Deploy phishing-resistant MFA everywhere. Train staff on translate.goog + Firebase patterns. Monitor cloud platforms for brand fakes. Share IOCs with CERT teams.
FAQ
Google Translate (translate.goog) and Firebase (*.web.app subdomains).
Mexico 385, US 101, Spain 67, India 54, Argentina 50.
Fake “wrong password” to capture two credential sets.
jnhwzs.fyi, gnpnia.lat; All-in-1.php scripts.
MFA, train on Google URL patterns, monitor Firebase abuse.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages