Hackers Abuse .arpa TLD and IPv6 Tunnels to Bypass Phishing Defenses
Phishing campaigns now exploit .arpa top-level domain and IPv6 tunnels to evade detection. Infoblox Threat Intel uncovered attackers creating A records in infrastructure-only .arpa namespace instead of expected PTR records. Security tools trust these reverse DNS domains automatically. Malicious content hosts on IPv6 tunnel services with clean reputations.
Traditional blocklists fail completely. .arpa lacks WHOIS registration data. Attackers generate domain generation algorithm subdomains under ip6.arpa. CNAME hijacking of abandoned government and university subdomains adds trusted reputations. Mobile residential IPs receive highest priority targeting.
Emails use hyperlinked images promising prizes or warning subscription issues. Traffic Distribution Systems fingerprint victims before payload delivery. Dr. Renée Burton of Infoblox calls it weaponized internet core plumbing.
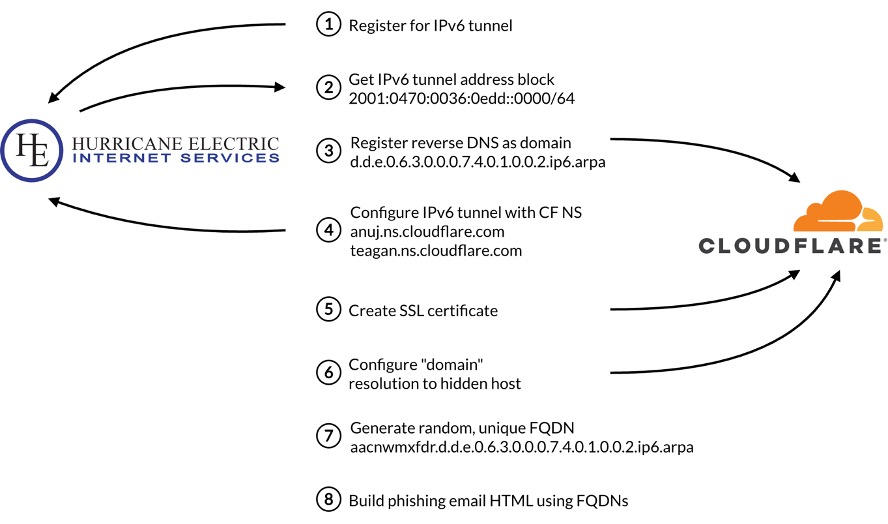
Attack Infrastructure
.arpa abuse patterns follow strict format.
| Domain Pattern | Type | Purpose |
|---|---|---|
| <random>.5.2.1.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa | IPv6 reverse DNS | Phishing hosting |
| actinismoleil.sbs | Standard TLD | Phishing landing |
| cablecomparison.shop | Standard TLD | Phishing landing |
| dulcetoj.com | TDS controller | Traffic distribution |
Delivery Chain
Sophisticated redirection targets high-value victims.
- Malspam Entry: Branded emails with prize/subscription lures
- Image Click: Hyperlinked graphics trigger TDS
- Fingerprinting: Mobile + residential IP prioritization
- .arpa Redirect: ip6.arpa domains host phishing pages
- CNAME Hijack: Trusted gov/edu subdomains mask traffic
Evasion Techniques
Multiple layers defeat defenses:
- Reputation Bypass: .arpa inherently trusted as infrastructure
- No WHOIS Data: Registration tracking impossible
- IPv6 Tunnels: Clean provider reputations
- DGA Subdomains: Random 10-character prefixes
- CNAME Hijacking: Abandoned trusted domains
Target Selection
TDS prioritizes:
- Mobile devices (highest conversion)
- Residential IP addresses
- European corporate networks
- High-value financial targets

Detection Challenges
Standard controls ineffective:
| Control Type | Why It Fails |
|---|---|
| Domain Blocklists | .arpa lacks reputation data |
| URL Filtering | Infrastructure TLD appears legitimate |
| WHOIS Analysis | No public registration records |
| IP Reputation | IPv6 tunnel providers clean |
Defense Recommendations
Network Layer:
- Block all .arpa A record resolutions
- Monitor ip6.arpa DNS queries
- Filter IPv6 tunnel egress traffic
- Deploy CNAME chain analysis
Email Gateway:
- Strip hyperlinked images from malspam
- Block trycloudflare.com subdomains
- Flag prize/subscription lures
Endpoint:
- Enable IPv6 traffic inspection
- Deploy DNS sinkholing for .arpa
IOC Summary
Primary Indicators:
*.ip6.arpa (A records, not PTR)
actinismoleil[.]sbs
cablecomparison[.]shop
dulcetoj[.]com (TDS)
FAQ
Infrastructure TLD trusted by all security tools.
Free tunnel services grant admin DNS access.
Mobile devices on residential IPs.
No. .arpa lacks reputation data.
Prize offers and subscription warnings.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages