Hackers abuse GitHub and GitLab to host malware and credential phishing campaigns

Attackers are increasingly abusing GitHub and GitLab as trusted delivery channels for malware and credential phishing. New research from Cofense says this tactic has grown steadily since 2021, with 2025 alone accounting for 45% of all observed campaign volume during the period studied.
The appeal is obvious. GitHub and GitLab are widely used inside enterprises, so security tools often trust their domains by default. That gives phishing emails and malware links a better chance of slipping past filters, especially when the links point to public repositories, raw file delivery paths, or pages that look like normal developer content.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Cofense says threat actors are no longer using these platforms for only one goal at a time. Many campaigns now combine malware delivery with credential theft, which raises the odds of compromise from a single click. Your sample article tracks closely with those findings.
Why GitHub and GitLab work so well for attackers
GitHub and GitLab sit at the center of modern software development. Blocking them outright can disrupt normal business operations, so many organizations allow traffic to these domains while applying lighter scrutiny than they would to unknown file-hosting sites. Cofense says threat actors have learned to take advantage of that trust.
By placing malicious files in repositories or setting up fake login pages tied to trusted developer infrastructure, attackers can make phishing messages look more legitimate. According to Cofense, this helps such emails evade secure email gateways that rely too heavily on domain reputation.
The numbers show where most of the abuse happens. Cofense says 95% of the campaigns it studied abused GitHub, while 5% used GitLab. It also found that 58% focused on credential theft and 42% delivered malware.
Malware and phishing now arrive together
One of the more concerning patterns in the Cofense research involves dual-purpose campaigns. In one case, tracked as ATR 383659, victims opened what appeared to be a PDF reader and ended up installing Muck Stealer, while a fake DocuSign page also opened to harvest credentials.
That combination makes these attacks more effective. Even if the malware path fails, the phishing page may still capture logins. If the user ignores the credential prompt, the downloaded malware may still run. Attackers no longer need a single point of success.
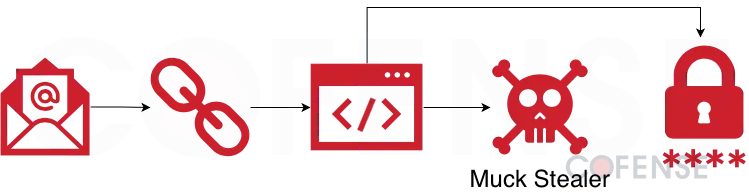
Cofense also says the malicious content often hides behind normal-looking development workflows. That makes it easier for users to trust a link when it comes from GitHub or GitLab, especially if the message references a document, reader, update, or shared file.
How attackers deliver the payloads
When attackers abuse GitHub, they can host malware directly in repositories or attach malicious files to comments on legitimate projects. Cofense notes that downloads may then redirect through GitHub’s raw content infrastructure, which can let malicious files arrive in the background with little visible friction for the user.
Cofense says Remcos RAT leads the malware families delivered through Git-based platforms in its dataset at 21% of volume. It is followed by Byakugan at 9%, AsyncRAT at 7%, and DcRAT in fourth place. Those payloads show that the tactic is not limited to one malware family or one actor.
Attackers also use password-protected ZIP and 7z archives to reduce the chance of automated inspection. Because the password sits in the phishing email rather than inside the archive, scanners may not be able to inspect the payload before delivery.
GitHub and GitLab abuse at a glance
| Metric | Finding |
|---|---|
| Share of campaigns abusing GitHub | 95% |
| Share abusing GitLab | 5% |
| Credential theft campaigns | 58% |
| Malware delivery campaigns | 42% |
| Share of total observed volume seen in 2025 | 45% |
| Top malware family on Git platforms | Remcos RAT (21%) |
Source: Cofense Intelligence.
GitLab campaigns can adapt to the victim
Cofense also documented a GitLab-based campaign tracked as ATR 404322 that used browser user-agent detection to tailor the attack. If the victim used a Windows device, the campaign delivered GoTo RAT. If not, it redirected the target to a credential phishing page instead.
That kind of filtering helps attackers waste fewer payloads and improve conversion. It also makes detection harder because different users may see different stages of the same campaign depending on their system and browser.
This reflects a wider phishing trend in which trusted infrastructure, adaptive delivery, and mixed objectives all work together. Cofense’s broader 2026 reporting says threat actors increasingly use trusted services and AI-assisted variation to evade traditional perimeter defenses.
What organizations should do now
Security teams should treat unexpected GitHub or GitLab links in email with the same caution they would apply to links from unknown domains. Trusting the platform alone is no longer enough when attackers can host malicious files or phishing pages on legitimate infrastructure.
Organizations should also enforce multi-factor authentication across business accounts so a stolen password does not immediately lead to account takeover. That will not stop malware delivery, but it does reduce the damage from credential phishing. This is a standard defensive inference that matches the campaign types Cofense describes.
Behavior-based email analysis also matters. Cofense argues that security teams need controls that look beyond domain reputation and inspect the behavior, file type, redirection chain, and user interaction flow behind a message.
Defensive priorities
- Treat unexpected GitHub and GitLab links in email as potentially hostile.
- Block or inspect password-protected archives arriving through email workflows.
- Enforce MFA on business accounts to reduce the impact of stolen credentials.
- Use behavior-based email analysis instead of trusting well-known domains.
- Run phishing simulations that include trusted-platform lures.
- Watch for redirections to raw content delivery paths and fake login pages.
These recommendations follow directly from Cofense’s campaign analysis and the delivery methods it documented.
FAQ
Because enterprises trust them and rely on them every day, which makes links hosted there less likely to be blocked or viewed as suspicious.
Cofense says 95% of the campaigns it studied abused GitHub, compared with 5% for GitLab.
Most aim to steal credentials or deliver malware, and some combine both in the same attack chain.
Cofense highlighted Remcos RAT, Byakugan, AsyncRAT, DcRAT, Muck Stealer, and GoTo RAT in different campaign examples and trend data.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages