Hackers abuse GitHub and Jira notifications to send phishing emails from trusted platforms

Attackers are abusing built-in email features in GitHub and Jira to send phishing messages through real SaaS infrastructure. Cisco Talos says this tactic lets malicious emails travel from legitimate platform servers, which makes them much harder for email filters and users to distrust.
The campaign matters because the emails pass normal authentication checks. Talos says messages sent this way can satisfy SPF, DKIM, and DMARC, which means many gateways see them as valid traffic instead of obvious phishing.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Talos calls this technique “Platform-as-a-Proxy,” or PaaP. The idea is simple: attackers do not need to spoof a brand or compromise an email server when they can abuse a trusted platform to generate the message for them.
Why GitHub and Jira work so well for this tactic
GitHub already supports notification emails tied to repository activity, and its documentation shows that notification emails come from GitHub-controlled addresses and headers. That trusted delivery model helps attackers hide malicious content inside a message that looks routine to developers and IT staff.
Talos says attackers used GitHub commit notifications as the lure. In the observed activity, they placed short social engineering hooks in commit summaries and then added longer scam text in the extended description, which later appeared inside the email notification body.
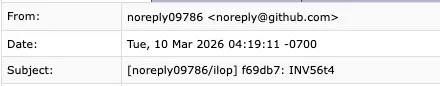
The researchers said the spike became especially visible on February 17, 2026, when about 2.89% of emails they saw coming from GitHub infrastructure likely tied back to abuse activity. Over a five-day period, Talos also found that roughly 1.20% of traffic from “[email protected]” carried an “invoice” lure in the subject line.
How the Jira version works
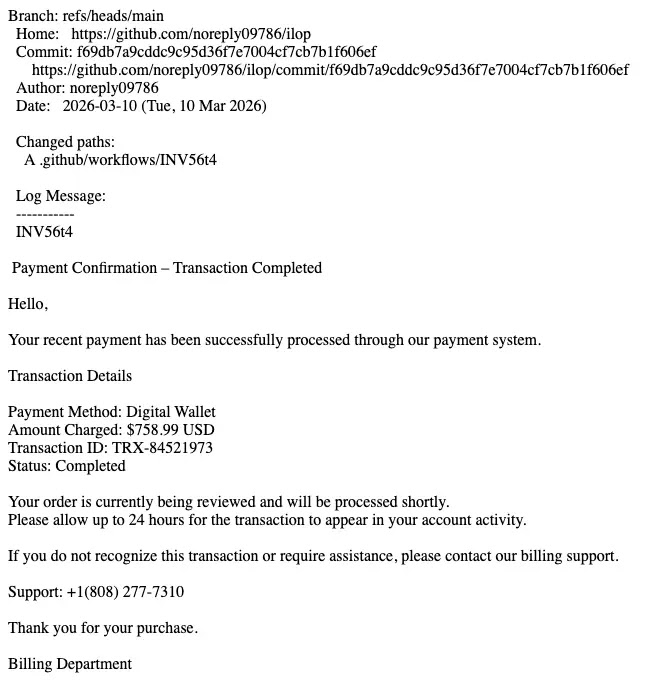
Jira gives attackers a different route. Atlassian documentation shows that Jira Service Management lets admins add customers by email, which triggers an invitation email from Atlassian’s system. Talos says attackers abused that workflow by stuffing phishing text into project-related fields and then inviting targets.
That matters because the final email still carries Atlassian branding and arrives as an expected system message. To the recipient, it can look like a normal help desk or service notification, not a phishing attempt built by an attacker.
Talos says most of these campaigns aim to steal credentials first. Once an attacker gets valid logins, that access can lead to account takeover, internal fraud, or deeper intrusion into corporate systems.
What security teams should watch for
| Platform | Abuse method | Why it slips through | Likely goal |
|---|---|---|---|
| GitHub | Malicious content embedded in commit notification workflows | Email comes from trusted GitHub infrastructure and authenticated domains | Credential theft, scam calls, fake billing lures |
| Jira | Malicious text embedded in service project or invite workflows | Email arrives as a legitimate Atlassian-branded invitation | Credential theft, social engineering, account access |
Security teams should not treat every SaaS notification as harmless just because the sender domain looks real. A GitHub or Jira email that pushes urgent payment demands, account warnings, or phone-based support instructions deserves extra scrutiny because that content does not match the normal purpose of those tools.
Talos recommends feeding GitHub and Atlassian activity logs into SIEM or SOAR platforms so defenders can catch unusual project creation, mass invitations, or other strange actions before the phishing email lands. It also advises users to open the service directly in a browser instead of clicking links inside surprise notifications.
For companies, the larger lesson is clear. Modern phishing no longer depends only on fake domains or broken authentication. Attackers now borrow the trust of real business platforms and turn normal automation into a delivery channel.
Quick signs this may be a SaaS notification phishing lure
- The email comes from a real platform, but the message pushes an invoice, refund, payment problem, or urgent account issue.
- The content asks you to call a number instead of using the official portal.
- The message creates panic and tries to rush you into action.
- The notification appears unrelated to your actual GitHub or Jira activity.
- The safest next step is to open GitHub or Jira directly and verify the event there.
FAQ
They are real platform-generated emails in the cases Talos described. The abuse happens when attackers use legitimate product features to inject phishing content into those messages.
Because the messages can pass normal sender authentication checks and come from trusted infrastructure. Traditional filtering often focuses on spoofing, bad domains, or authentication failure.
Do not click first. Open GitHub or Jira directly, check whether the event exists, and report the message to your security team if the content looks unusual or unrelated to your work.
Monitor GitHub and Atlassian activity logs, flag financial lures in developer-tool notifications, and train staff not to trust automated SaaS email blindly.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages