Hackers hijack hotel booking workflows to send fake payment requests to real guests
A growing fraud campaign is targeting hotel guests by abusing trusted reservation workflows instead of relying on generic phishing alone. Researchers at Gen call it the “Reservation Hijack Scam,” and say attackers use real booking details plus legitimate-looking hotel communication channels to pressure travelers into making fake payments.
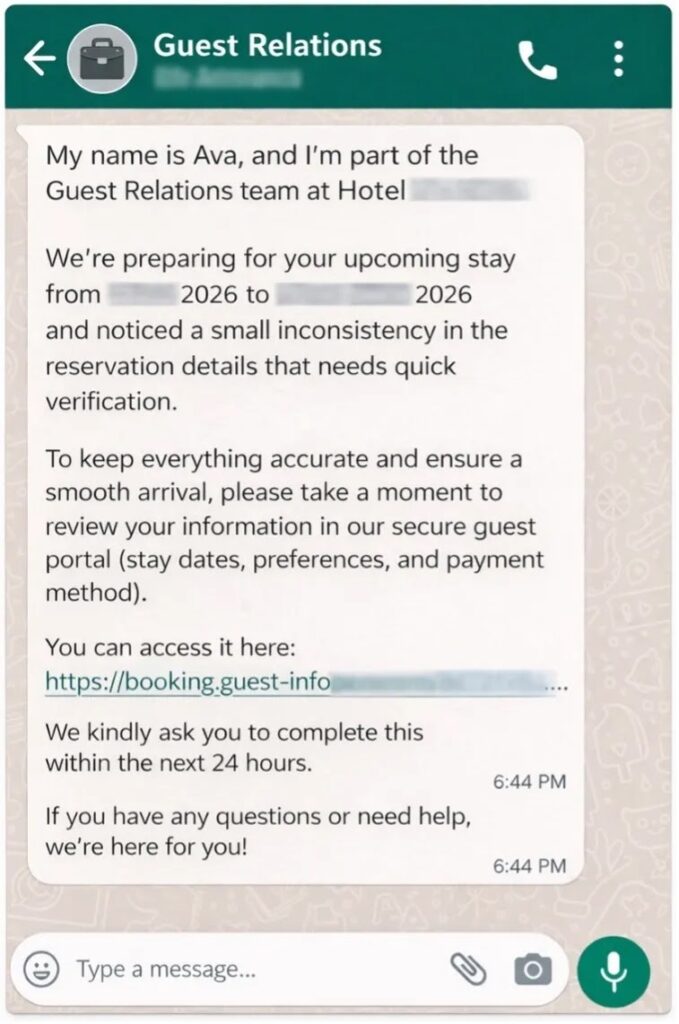
The scam often starts with a message that looks routine. Victims receive a WhatsApp message, SMS, email, or even a message inside a booking thread that appears to come from hotel staff and asks them to verify or complete payment before arrival. Gen says the messages often include the real property name, trip dates, and payment context, which makes them feel credible.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This is what makes the campaign more dangerous than a basic phishing email. The attackers do not always need polished language or advanced malware at the guest side. They only need enough stolen reservation data and enough access to trusted workflows to make a fake payment request look like normal customer service.
How the scam works
Gen says the campaign operates through two main paths. In one, attackers impersonate hotel staff or booking support and send guests to fake payment pages through WhatsApp, email, SMS, or booking-platform messages. In the other, they first compromise hotel-side systems, then use legitimate access to message guests directly from trusted channels.
That second path creates the biggest risk. According to Gen, attackers phish hotel employees and partners to steal account credentials for hospitality software, then log into real environments and access reservation data such as guest names, contact details, stay dates, and payment information. Once inside, they can send fraudulent payment requests through real hotel or booking-linked workflows.
The sample you shared captures the core mechanics accurately, including the use of stolen reservation details, compromised hotel software accounts, malicious PDFs, and typo-squatted payment domains. It also correctly reflects Gen’s point that this is a workflow hijack built on trust and context rather than a simple generic travel scam.
Why guests keep falling for it
When a payment request arrives inside a real booking thread, or references a confirmed stay with the correct dates and hotel name, many travelers assume it is legitimate. Gen says the scam abuses the fact that guests already expect some kind of pre-arrival communication from hotels, especially around payment verification, late check-in, or booking confirmation.
Booking.com’s own traveler safety guidance matches that risk. The company says travelers should not send a payment that falls outside the platform’s stated policy, and warns that no legitimate transaction or reservation change should take place outside the official booking flow.
For hotel partners, Booking.com also says its messaging protections exist specifically to stop cybercriminals from impersonating properties and sending fraudulent payment links to guests. That public warning matters because it confirms the attack does not only target end users. It also targets the communication layer between hotels and guests.
How hotel-side compromise escalates the fraud
Gen says attackers do more than steal passwords. In some cases, they trick hotel staff or partners into running a malicious command disguised as a security update, which installs remote access malware and gives the attacker a more durable foothold inside the hotel’s environment.
That detail matters because it turns an account compromise into an operational breach. Instead of one stolen login, the attacker can gain ongoing access to reservation data, internal workflows, and guest communication tools. That gives them time to send professionally styled payment requests, often with deadlines of 24 to 48 hours, to push guests into paying fast.
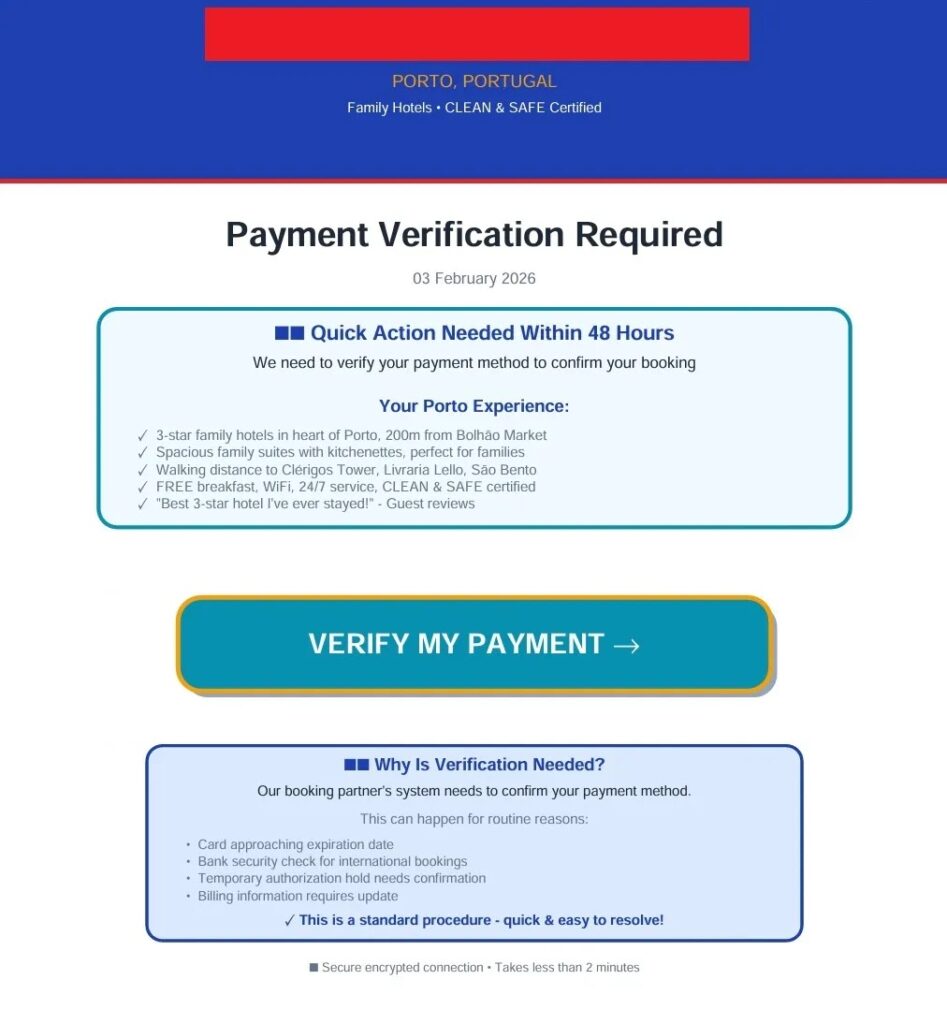
The sample article also correctly notes that some PDFs and payment requests were hosted on already compromised legitimate infrastructure before sending victims to typo-squatted domains. That extra layer of trust can make the scam harder to spot, because the attack chain may begin on a real partner-linked resource before the victim reaches a fake payment page.
Main signs of the reservation hijack scam
| Red flag | Why it matters |
|---|---|
| Urgent request to “verify” or “complete” payment | Pressure reduces the chance the guest will verify independently |
| Message references a real booking | Stolen reservation data makes the scam look legitimate |
| Link leads outside the hotel or booking platform | Payment often shifts to typo-squatted or unrelated domains |
| Message arrives through WhatsApp or SMS | Attackers use channels guests may trust for quick travel updates |
| PDF invoice with a short deadline | Fraudsters add urgency and branding to look official |
| Payment request conflicts with the booking policy | Booking.com says legitimate transactions should stay within official flows |
The countries with the highest observed activity in Gen’s research included the UK, France, Germany, the US, Brazil, and Australia. That does not mean other regions are safe. It means the scam already has broad international reach and can easily move wherever attackers find exposed hotel accounts and active reservation data.
What travelers should do right now
- Do not tap a payment link sent through WhatsApp, SMS, email, or a booking thread unless you independently verify it first.
- Open the hotel’s official website or the original booking platform yourself instead of using the message link.
- Call the property using the number listed on the official site or app if anything about the message feels unusual.
- If you already entered card details, contact your bank immediately, freeze or replace the card, and enable transaction alerts.
- Watch for follow-on scams after the first contact, especially refund scams or “failed payment” messages. This inference follows Gen’s description of attackers using real context and repeated trust cues to keep victims engaged.
What hotels and partners should do
- Enforce phishing-resistant MFA for staff accounts that access reservation or guest-messaging systems. Cloudbeds says its platform uses MFA as a core protection layer, and Booking.com tells partners to report suspected account attacks immediately.
- Train staff to recognize fake support emails, urgent login alerts, and update prompts. Cloudbeds says it is tracking an ongoing phishing campaign affecting hospitality providers across the industry.
- Limit who can export reservation data or send payment-related guest messages. That recommendation follows directly from Gen’s finding that attackers abuse reservation visibility and trusted messaging workflows.
- Review messaging-security settings and account access logs for unusual activity. Booking.com says messaging protections exist to reduce impersonation and fake payment-link abuse.
- Treat guest communication systems as security-critical infrastructure, not just service tools. That conclusion follows from Gen’s findings about how attackers turned routine hospitality workflows into fraud channels.
FAQ
It is a fraud scheme in which attackers use stolen booking details and trusted hotel or booking workflows to send fake payment requests to real guests. Gen documented the campaign on March 25, 2026.
Researchers say they often steal hotel or partner credentials through phishing, then log into real hospitality software and access future reservation data. In some cases, they also trick staff into running malicious commands that install remote access malware.
Yes. Gen says attackers may use legitimate hotel or booking-linked communication channels after compromising the hotel side of the workflow, which makes the fraud much harder to detect.
Do not use the link in the message. Open the booking platform or hotel website yourself, then verify the request through official channels. Booking.com says legitimate transactions should not happen outside official payment policies and workflows.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages