Hackers Scan SonicWall Firewalls from 4,000+ IPs for SSL VPN Exploits

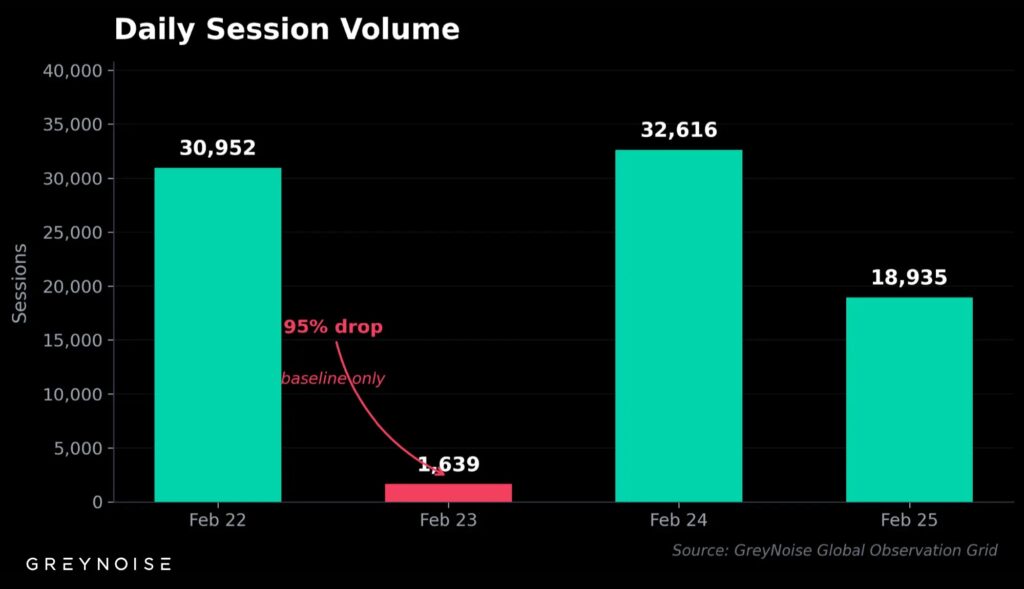
Hackers launched a massive scan against SonicWall firewalls using over 4,000 unique IP addresses. The campaign hit 84,142 sessions from February 22-25, 2026. Attackers mapped devices with active SSL VPN before planned exploits.
SonicWall SSL VPN remains a top ransomware entry point. The REST API endpoint checking VPN status took 92% of scans. This builds target lists fast. Over 430,000 SonicWall devices face the public internet.
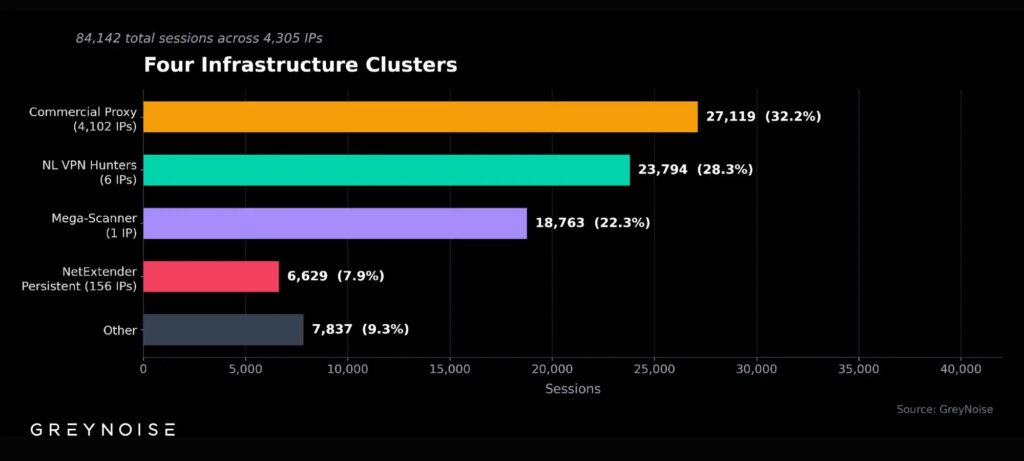
GreyNoise tracked three infrastructure clusters. They used commercial rotating proxies for cover. This mirrors a December 2025 scan wave against SonicWall and Palo Alto gear. Activity escalates now.
More than 25,000 SSL VPNs run unpatched critical flaws. Another 20,000 use unsupported firmware. Akira ransomware hit 250+ orgs via SonicWall since 2023, pulling $244 million. Fog groups encrypt networks in hours.
Campaign Details
| Metric | Value |
|---|---|
| Sessions | 84,142 |
| Unique IPs | 4,305 across 20 ASNs |
| Duration | Feb 22-25, 2026 |
| Main Target | SonicOS REST API / SSL VPN check |
| Proxy Sessions | 27,119 (32%) via 4,102 rotating IPs |
| Fingerprint | HTTP/1.0 + Chrome 119 UA |
Proxies averaged 6.6 requests per IP. This dodges rate limits and blocklists. The service sat unmanaged since December 2025. Amsterdam IPs scanned Cisco ASA too.
Five of seven key CVEs sit in CISA’s Known Exploited list. Four link to ransomware directly.
Key Risks
- Akira exploits for initial access.
- Fog full encryption in <4 hours.
- 25,000+ unpatched SSL VPNs exposed.
- 20,000 on end-of-life firmware.
Patch CVE-2024-53704 now (CVSS 9.8). Enable MFA on VPN. Lock management to trusted IPs. Reset old passwords. Watch for HTTP/1.0 + Chrome UA scans. Scrap EOL SRA gear.
FAQ
SSL VPN offers ransomware entry; 430k devices exposed online.
4,305 unique across 20 networks in 4 days.
Commercial service with 4,102 rotating Canadian IPs.
CVE-2024-53704 (CISA KEV, CVSS 9.8); EOL: CVE-2021-20028.
Akira (250+ victims, $244M); Fog rapid encryption.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages