Hackers Weaponize Windows File Explorer WebDAV for RAT Delivery

Cybercriminals bypass browser defenses by abusing Windows File Explorer’s legacy WebDAV support. Attackers deliver RATs through file:// links, .url shortcuts, and LNK files that connect directly to remote servers. Cofense Intelligence reports 87% of campaigns deploy XWorm, AsyncRAT, and DcRAT against European corporate networks. No browser warnings appear during connections.
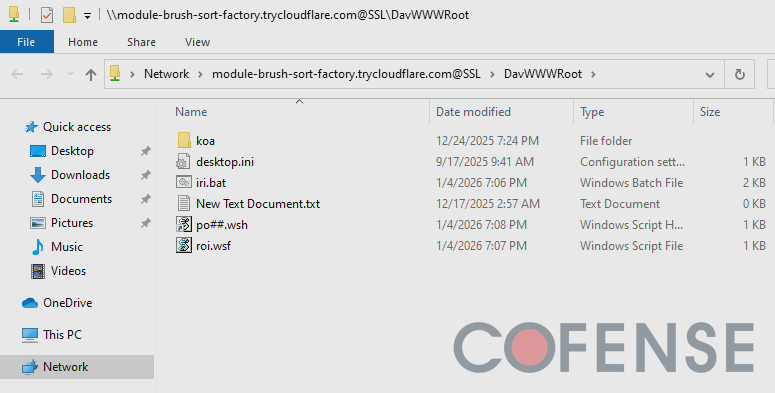
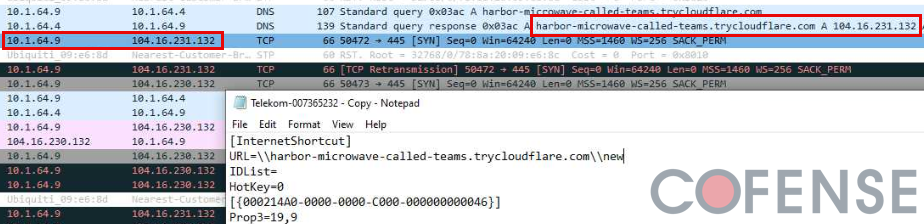
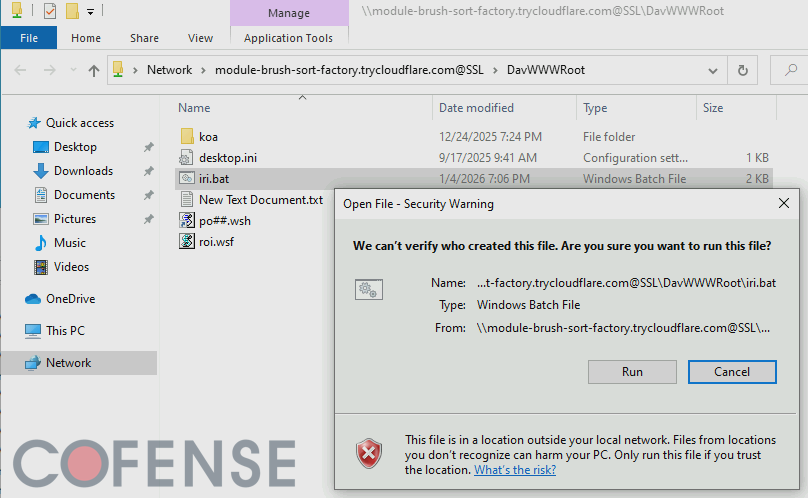
WebDAV protocol support lingers in Explorer despite Microsoft’s 2023 deprecation announcement. Remote servers appear as local folders. Users ignore standard “Open file from network?” prompts accustomed to legitimate shares. DNS beaconing occurs when directories containing malicious .url files open.
German-language phishing dominates at 50% of campaigns disguised as invoices. Cloudflare Tunnel trycloudflare[.]com hosts ephemeral WebDAV servers. Legitimate CDN traffic masks malicious activity until servers vanish.
Attack Delivery Methods
Three vectors exploit File Explorer directly.
| Method | Technique | Evasion Benefit |
|---|---|---|
| file:// URI | Direct WebDAV folder access | No browser security prompts |
| .url Shortcuts | UNC paths over HTTP/HTTPS | DNS beacon on directory open |
| LNK Shortcuts | Hidden CMD/PowerShell download | Silent payload execution |
DavWWWRoot keyword targets WebDAV root directory consistently.
Malware Distribution
RATs dominate payload selection.
- XWorm RAT: 42% of analyzed campaigns
- AsyncRAT: 31% deployment rate
- DcRAT: 14% observed instances
- Multiple RATs: 87% of Active Threat Reports
European targets receive German (50%) and English (30%) phishing lures.
Infrastructure Characteristics
Cloudflare Tunnel domains rotate rapidly:
| Malicious Domain | ATR ID |
|---|---|
| tiny-fixtures-glossary-advantage.trycloudflare.com | 374884 |
| nasdaq-aged-sf-cheers.trycloudflare.com | 377161 |
| lose-croatia-acdbentity-lt.trycloudflare.com | 377161 |
| discounted-pressed-lc-vcr.trycloudflare.com | 376309 |
Servers live hours before decommission. Legitimate Cloudflare IPs evade reputation blocks.
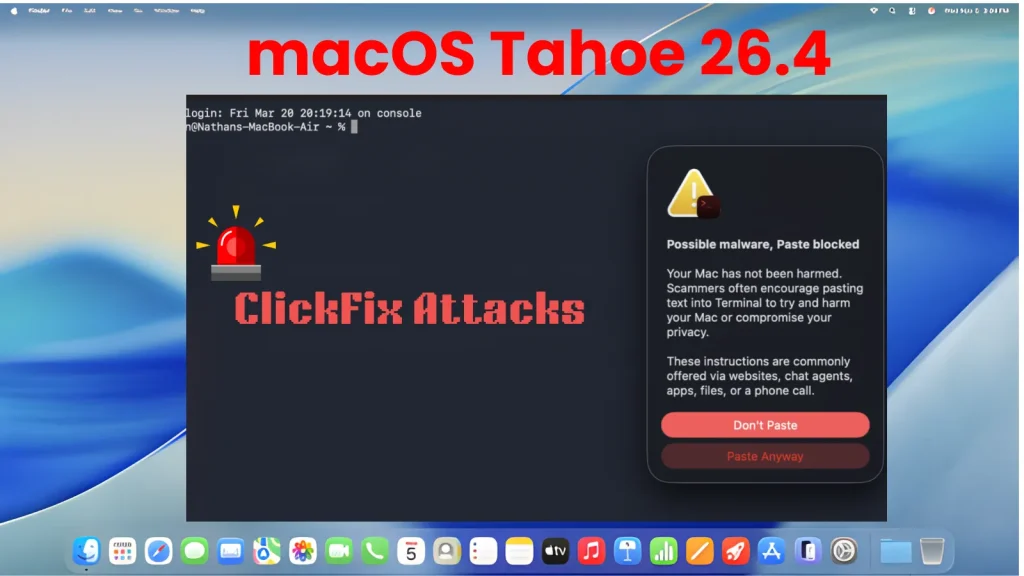
Detection Challenges
Traditional controls fail:
- Browser download scanners bypassed
- No HTTP referer headers sent
- File Explorer lacks URL reputation
- Users dismiss network file warnings
- Ephemeral domains evade blocklists
DNS queries trigger on .url directory access even without clicks.
Security Recommendations
Immediate Actions:
- Block trycloudflare[.]com subdomains
- Monitor File Explorer network connections
- Disable WebDAV client via registry
- Train users to check Explorer address bar
- Deploy network beacons to listed ATR domains
Registry Hardening:
EDR Hunting:process_name:explorer.exe AND destination_port:80 OR 443
file_extension:.url AND path:DavWWWRoot
User Awareness
Educate employees:
- Verify File Explorer address bar shows legitimate domains
- Treat network file warnings as high-risk
- Report invoice phishing immediately
- Never open unexpected .url or .lnk files
FAQ
File Explorer connects directly, skipping browser warnings.
XWorm RAT (42%), AsyncRAT (31%), DcRAT (14%).
DavWWWRoot targets WebDAV server root.
Standard network file prompt appears but gets ignored.
Cloudflare Tunnel trycloudflare[.]com with rotating subdomains.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages