Handala Hack uses RDP, NetBird, and parallel wipers in MOIS-linked destructive intrusions

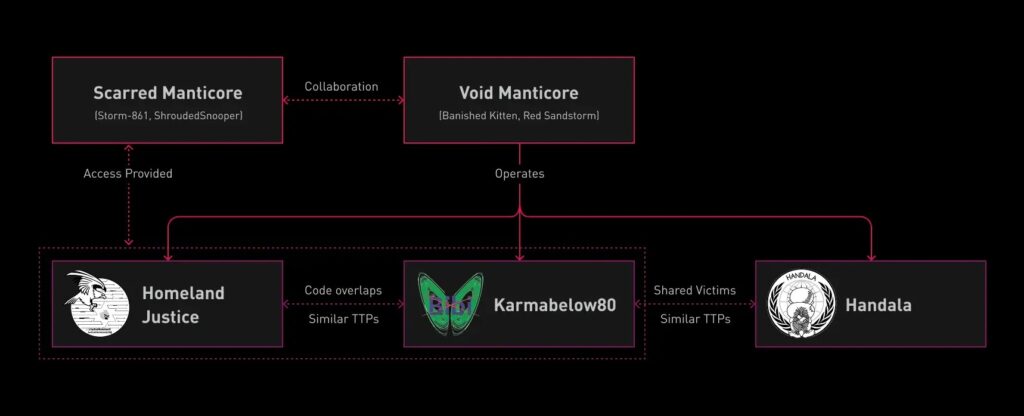
An Iranian threat actor known as Handala Hack has been carrying out destructive intrusions that rely on remote desktop access, NetBird tunneling, and multiple wiping tools launched in parallel to maximize damage. Check Point Research says the group is an online persona operated by Void Manticore, also tracked as Red Sandstorm and Banished Kitten, and links the actor to Iran’s Ministry of Intelligence and Security, or MOIS.
These attacks focus on disruption and destruction rather than quiet intelligence collection alone. Check Point says the group conducts fast, hands-on operations inside victim networks, then deploys several wiping methods at once so recovery becomes much harder. The company says recent activity has targeted organizations in Israel and Albania, while the group has also expanded to U.S. organizations, including medical technology giant Stryker.
The newer campaigns show several tactical changes. Check Point says the actor has started using NetBird, a legitimate peer-to-peer networking tool, to tunnel traffic inside victim environments, and has also deployed an AI-assisted PowerShell script as part of its destructive toolkit. The researchers also said the group showed weaker operational security in some cases, with activity traced directly to Iranian IP addresses instead of commercial VPN services.
How the attacks begin
Check Point says the intrusion often starts with compromised VPN credentials. The actor obtains access through brute-force attempts or supply-chain compromises involving IT service providers, then moves manually through the environment over Remote Desktop Protocol. In at least one victim network, the researchers observed five attacker-controlled machines operating at the same time, which points to an effort to spread damage as quickly as possible.
Once inside, the operators use built-in Windows tooling, credential theft, and lateral movement techniques that Check Point says have stayed fairly consistent from 2024 through 2026. The newer additions, including NetBird, fit into that same playbook by giving the attackers another way to maintain internal access and route traffic around normal controls.
What makes the destructive phase different
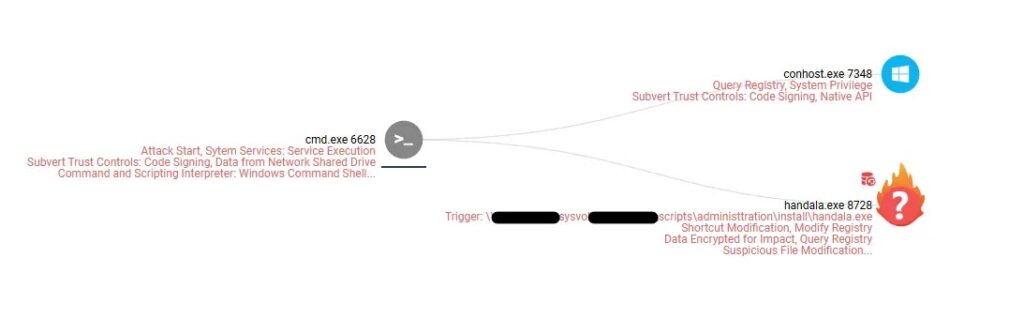
Check Point says Handala’s destructive phase runs several wiping methods in parallel. One of the main tools is a custom Handala Wiper distributed through Group Policy logon scripts by way of a batch file named handala.bat. The report says this wiper overwrites file contents and corrupts the Master Boot Record, which adds deeper system damage beyond ordinary file deletion.
The researchers also describe an AI-assisted PowerShell wiper that deletes files from user directories and floods logical drives with a propaganda image named handala.gif. In parallel, the attackers use VeraCrypt, a legitimate encryption tool, to lock drives and make recovery harder. They also manually delete virtual machines and individual files over RDP, a tactic that Check Point says appears in the group’s own leaked videos.
That layered approach matters because it reduces the chance that defenders can stop the attack by blocking just one payload. If one wiping path fails or gets interrupted, others may still destroy enough data to cripple the victim. That conclusion follows directly from Check Point’s description of multiple simultaneous wiping tracks.
Why NetBird stands out
NetBird is not malware. It is a legitimate networking tool, which gives the attackers a practical way to tunnel traffic through the environment while blending in with allowed software. Check Point lists NetBird as one of the newly observed tactics in these intrusions, which suggests the actor is expanding its use of dual-use tools rather than relying only on custom malware.
That trend fits Check Point’s broader assessment of Iranian cyber activity. In a separate March 2026 report, the company said MOIS-linked actors increasingly mix state-directed operations with tools, infrastructure, and access patterns borrowed from the cybercrime ecosystem.
Key details at a glance
| Item | Detail |
|---|---|
| Threat actor | Handala Hack |
| Broader cluster | Void Manticore |
| Other names | Red Sandstorm, Banished Kitten |
| Assessed sponsor link | Iran’s MOIS |
| Main access methods | Compromised VPN credentials, RDP, supply-chain footholds |
| Newly highlighted tools | NetBird, AI-assisted PowerShell wiper |
| Destructive methods | Custom wiper, MBR corruption, VeraCrypt, manual deletion over RDP |
| Main targeting noted by Check Point | Israel, Albania, and recent expansion to U.S. organizations |
What defenders should do
- Enforce multi-factor authentication on VPN, remote access, and privileged accounts. Check Point explicitly recommends this because compromised remote access remains a core entry point.
- Monitor for logins from unusual countries, strange hours, unfamiliar devices, and abnormal VPN transfer patterns.
- Disable RDP where it is not needed, especially on systems that should never allow broad remote administration.
- Watch closely for NetBird and other tunneling tools in environments where they are not approved.
- Prepare for multi-tool destructive activity, not just one malware family, because Handala’s impact comes from parallel wiping and manual operator actions together. This last point is an inference from Check Point’s case descriptions.
FAQ
Check Point says Handala Hack is an online persona run by Void Manticore, an Iranian threat actor affiliated with MOIS.
Check Point says recent operations added NetBird tunneling and an AI-assisted PowerShell wiper to a long-running destructive playbook.
Because the attackers use hands-on remote access to move through victim environments, trigger deletion tasks, and manually destroy assets such as virtual machines.
Yes. Check Point says the group has targeted organizations in Israel and Albania and has recently expanded to U.S. enterprises such as Stryker.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages