Horabot resurfaces in Mexico with phishing chain that turns infected PCs into email spam hubs

Horabot is back, and researchers say the latest campaign has hit Mexico hard. Kaspersky says the banking trojan uses a fake CAPTCHA page, a multi-stage malware chain, and an email worm that turns each infected machine into a phishing relay. The company found an exposed threat-actor database showing 5,384 victims, with about 93% of them located in Mexico.
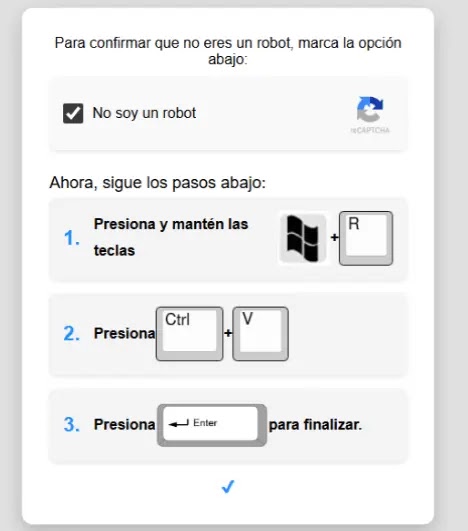
The campaign stands out because it relies on user deception instead of a software exploit. Victims land on a fake CAPTCHA page, open the Windows Run dialog, and paste a malicious mshta command themselves. That action pulls down the first-stage HTA loader and starts the infection chain.
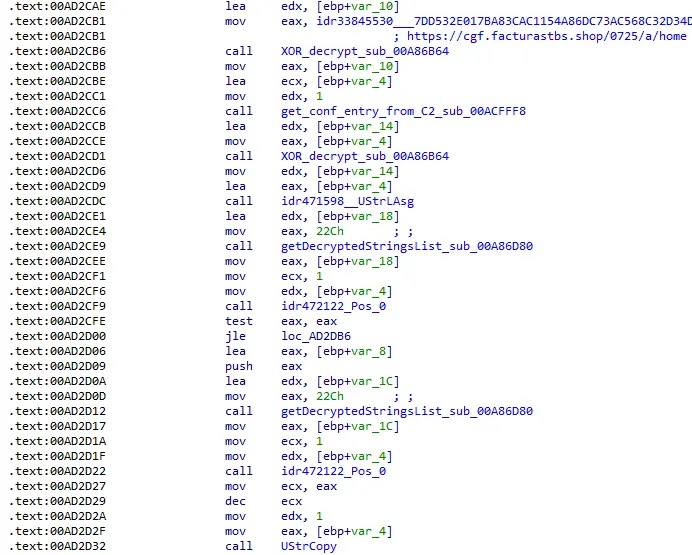
Kaspersky says the malware bundle includes a banking trojan, an email spreader, and several obfuscated stages that use JavaScript, VBScript, PowerShell, AutoIt, and an in-memory DLL payload. The company adds that Horabot remains highly active in 2026 and continues to evolve, including updates to its encryption and protocol logic.
This campaign also fits Horabot’s older pattern. Cisco Talos previously described Horabot as a Brazil-linked threat that targets Spanish-speaking users in the Americas, steals credentials, harvests Outlook contacts, and sends phishing emails from victim mailboxes.
What happened
Kaspersky says its MDR team first spotted the campaign after a suspicious mshta execution alert in a customer environment. Endpoint protection stopped the malicious process before the full chain could complete, but the investigation led analysts to the attacker’s infrastructure and the broader campaign.
From there, researchers traced the operation to a fake CAPTCHA page hosted on attacker-controlled infrastructure. The lure told users to paste a command into the Run box, which fetched and executed an HTA file. That HTA then launched a JavaScript payload, followed by heavily obfuscated VBScript stages.
Kaspersky says one of the later scripts collected system details, downloaded AutoIt components, set persistence through a shortcut in the Startup folder, and used PowerShell to reach additional URLs. It then deployed the next stage, which decrypted and loaded the banking trojan into memory.
Why the Mexico wave matters
The victim log Kaspersky found suggests this was not a small test. The exposed page listed infections dating back to May 2025, and 5,030 of the 5,384 recorded victims were in Mexico. The phishing lures researchers collected were written in Spanish and posed as invoices or confidential business files, which matches the regional focus.
Researchers also found clues that point to Brazilian operators. Kaspersky says comments in the code were written in Brazilian Portuguese, and some of the phrasing looked natural enough to suggest a local author rather than copied text. Cisco Talos had earlier reached a similar conclusion, saying the operator likely came from Brazil.
How the infection chain works
| Stage | What happens | Why it matters |
|---|---|---|
| Initial lure | Fake CAPTCHA page tells the user to run an mshta command | The victim triggers the infection manually |
| First loader | HTA fetches JavaScript from an attacker domain | Helps the attack move past the first step quietly |
| Obfuscated scripts | VBScript and PowerShell gather data, add persistence, and fetch more files | Adds stealth and flexibility |
| AutoIt stage | AutoIt components decrypt and launch the next payload | Prepares the banking trojan in memory |
| Final payload | Horabot banking trojan runs and connects to C2 | Enables credential theft and continued abuse |
| Email worm | Malware sends phishing emails from infected machines | Expands the campaign using trusted inboxes |
The broad sequence above comes from Kaspersky’s March 2026 analysis.
What Horabot does after infection
Kaspersky says the malware chain does more than drop a banking trojan. Using PowerShell, the threat can exfiltrate unique email addresses to command-and-control infrastructure and send phishing emails with malicious PDF attachments from selected infected users. Those messages push new targets into the same infection cycle.
Cisco Talos previously said Horabot can control the victim’s Outlook mailbox, collect contact addresses, and send phishing emails to those contacts. Talos also said the malware can steal credentials, operating system details, keystrokes, and one-time banking codes.
That combination makes Horabot more than a simple banking trojan. It acts as a credential stealer, a phishing platform, and a persistence mechanism for future fraud. Each newly infected system can help the campaign grow.
Key signs defenders should watch for
- Suspicious
mshtaexecution from a user-initiated Run command. - Fake CAPTCHA pages that instruct users to paste commands into Windows.
- Unexpected PowerShell, VBScript, or AutoIt activity chained together.
- Startup-folder shortcut creation linked to newly dropped files.
- Outbound phishing emails sent from internal user inboxes.
What organizations should do now
Security teams should block or tightly control HTA execution from untrusted sources and pay close attention to suspicious mshta launches. Kaspersky says defenders should also deploy the published YARA and Suricata rules from its full report, add the listed indicators to blocklists, and train users to distrust fake CAPTCHA pages and invoice-themed attachments.
Kaspersky also recommends stronger anti-spam tuning, caution with unknown attachments, and updated endpoint protection. The company says businesses should combine tooling with human-led detection and threat intelligence because the threat remains active and continues to change.
FAQ
Horabot is a malware family linked to banking theft, phishing, and mailbox abuse. Researchers say it can steal credentials, spread through email, and target Spanish-speaking users in the Americas.
Kaspersky found an exposed victim database with 5,384 infections, and about 93% of them were in Mexico. The phishing lures were also written in Spanish and tailored to local targets.
Kaspersky’s latest report says the chain starts with a fake CAPTCHA lure that tricks users into running a malicious mshta command themselves. That makes social engineering the main entry point in this campaign.
It combines banking theft with worm-like phishing spread. Once a system is infected, the malware can help send more malicious emails from the victim’s own mailbox, which makes follow-on messages look more trustworthy.
Start with suspicious mshta activity, fake CAPTCHA lures, chained script execution, and unusual mailbox-driven phishing from internal accounts. Those are some of the clearest signals described in the published research.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages