How elite SOCs cut escalation rates by giving Tier 1 better threat intelligence
Security teams cut unnecessary escalations when Tier 1 analysts get faster access to context, not just more alerts. The goal is simple: help frontline analysts decide with confidence whether an alert is benign, suspicious, or ready for deeper investigation. NIST says organizations should use up-to-date cyber threat intelligence in log analysis tools to improve detection accuracy, which supports this shift toward better first-line decisions.
This matters because a modern SOC does not fail only when it misses an attack. It also loses efficiency when Tier 1 sends too many weak or incomplete cases to Tier 2. Microsoft’s Sentinel guidance shows how threat intelligence, enrichment, analytics rules, and automation all sit inside the investigation workflow that security teams use to triage incidents and choose the right response.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The strongest SOCs reduce escalation volume by tightening the first decision point. They give Tier 1 better enrichment on IPs, domains, URLs, hashes, process trees, and campaign context, then back that up with repeatable triage rules. Google’s SecOps documentation describes the same pattern: alerts become easier to handle when analysts can enrich indicators, pull prevalence data, inspect process relationships, and gather evidence before deciding whether a case needs a deeper handoff.
Why Tier 1 escalates too often
Tier 1 analysts usually escalate because they lack time, context, or confidence. They might see a suspicious IP or domain in an alert, but the alert alone rarely explains whether the indicator belongs to a live malware campaign, a known false positive pattern, or a low-risk artifact that only looks suspicious.
That gap creates friction everywhere. Tier 2 spends time rechecking cases that never needed deeper analysis. Threat hunters lose time to reactive case cleanup. Managers then see slower investigations, heavier backlogs, and weaker response consistency. The 2025 SANS SOC Survey highlights alert triage, detection, and incident response as core SOC functions, which underscores how much pressure lands on the first layer of analysis.
Elite teams close that gap by moving context closer to the analyst. They enrich alerts with threat intelligence at the moment of review, use structured playbooks to suppress noisy incidents, and route only the cases that carry clear risk or unresolved ambiguity. Microsoft’s automation guidance explicitly includes suppressing noisy incidents, assigning triage tasks, and escalating incidents only after defined handling steps.
What better threat intelligence changes in practice
Good threat intelligence gives Tier 1 more than a reputation score. It adds usable evidence: when an indicator was first or last seen, what malware family it connects to, what tactics it maps to, how common it is, and whether related activity appears elsewhere in the environment. Google SecOps says its investigation flow uses indicator enrichment, prevalence data, case metadata, and process-tree analysis to build context before deeper action.
Microsoft makes a similar point in Sentinel. Its threat intelligence features enrich indicators with data such as geolocation and WhoIs, while built-in analytics can generate higher-fidelity alerts and incidents for security teams to triage. In practical terms, this helps Tier 1 spend less time guessing and more time closing or prioritizing alerts based on evidence.
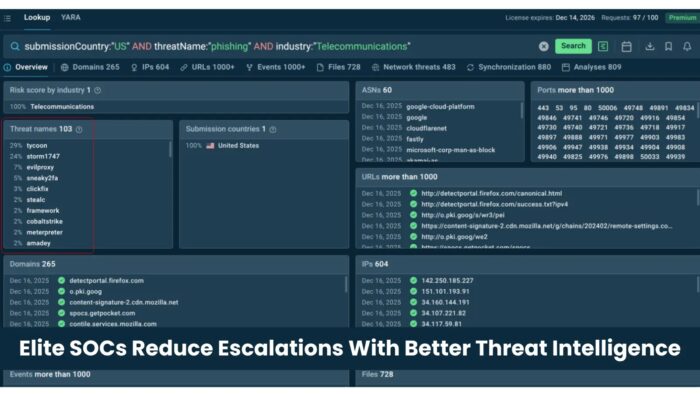
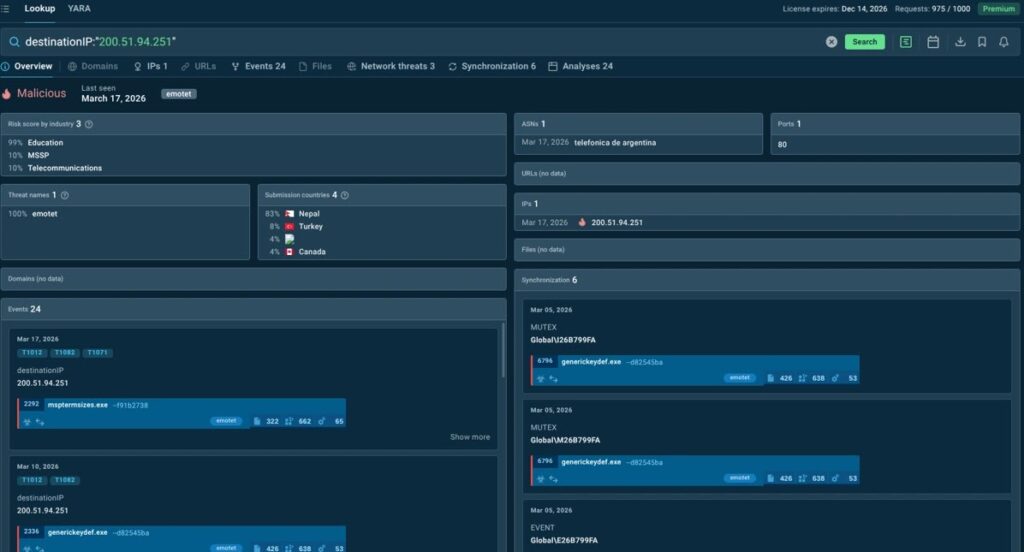
Vendors that specialize in operational threat intelligence push the same workflow closer to the analyst. ANY.RUN says its Threat Intelligence Lookup is built to speed up alert triage, incident response, and threat hunting by letting teams search indicators across millions of sandbox research sessions and review contextual data tied to threats, TTPs, and IOCs. Used well, tools like this can help Tier 1 resolve more routine alerts without sending uncertainty upstream.
What high-performing SOCs usually do differently
| Practice | What Tier 1 gets | Effect on escalations |
|---|---|---|
| IOC enrichment at first touch | Context on IPs, domains, URLs, hashes, and related behavior | Fewer “just in case” handoffs |
| Standard triage playbooks | Clear close, contain, monitor, or escalate criteria | More consistent decisions |
| Noise suppression rules | Fewer repeat false positives | Less wasted analyst time |
| Incident automation | Ownership, tags, and status changes happen faster | Cleaner routing to Tier 2 |
| Feedback loop from Tier 2 | Analysts learn what deserved escalation | Better judgment over time |
| Integrated threat intel feeds | Current intelligence inside SIEM/SOAR workflows | Faster, evidence-based triage |
How to lower escalation rates without weakening security
- Put threat intelligence directly inside the Tier 1 workflow.
- Enrich every suspicious indicator before an analyst decides to escalate.
- Build playbooks that define what Tier 1 can close on its own.
- Suppress recurring false positives instead of reviewing them forever.
- Feed Tier 2 findings back into Tier 1 handling rules every week.
- Track escalation reasons, not just escalation counts.
- Measure how many escalations return as benign or low value.
- Give Tier 1 tools that explain why an indicator matters.
FAQ
No, not when the reduction comes from better context and better playbooks. Risk rises when teams suppress alerts blindly. It falls when Tier 1 closes low-value noise based on evidence and pushes forward only the alerts that need deeper analysis. NIST and Microsoft both point toward this model by emphasizing current threat intelligence, structured triage, and automated handling.
The most useful intelligence answers immediate triage questions. Analysts need to know whether an IP, domain, hash, or URL has known malicious associations, what campaign or malware family it links to, how prevalent it is, and what related behavior surrounds it. Google SecOps and Microsoft Sentinel both highlight contextual enrichment as part of practical incident triage.
Not fully. Automation can gather context, suppress noise, assign owners, and trigger defined workflows. Analysts still need to interpret edge cases, judge business impact, and decide when ambiguity justifies escalation. Microsoft’s automation guidance centers on assisting analysts, not removing them from the loop.
No. MSSPs and smaller in-house teams can benefit just as much because they often face the same problem with fewer people. Better enrichment and cleaner routing help small teams protect investigation time and avoid burning senior staff on low-value reviews. SANS identifies alert triage and incident response as core SOC functions across environments, not just the largest ones.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages