How SOC Analysts Cut Alert Review Time from 30 to 2 Minutes
SOC analysts waste about 30 minutes per benign alert gathering context from tools like threat intel, logs, and detonators. Interactive sandboxes slash this to 2 minutes by showing real behavior instantly. ANY.RUN claims 28-minute savings per alert via live execution. Their features page notes: “Watch processes, networks, and interactions unfold in real time for fast verdicts.”
Manual reviews drag on. You check hashes, pivot logs, enrich data, and detonate samples. Each step adds time. Backlogs grow. Real threats wait.
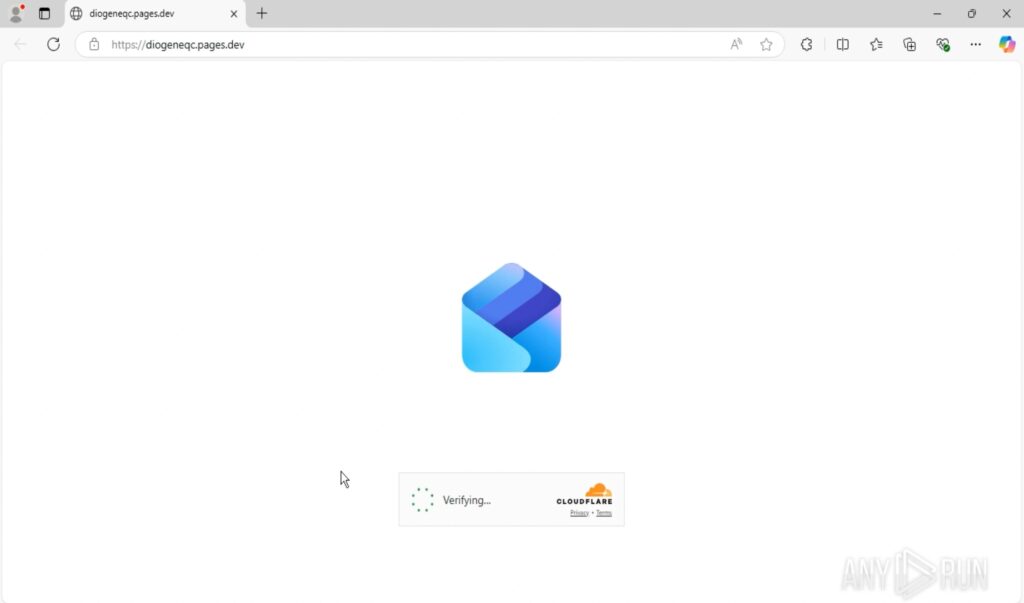
Sandboxes change this. Upload a file or URL. It runs in a safe VM. See spawns, connections, redirects live. Interact as a user would. Benign? Close fast. Malicious? Escalate with proof.
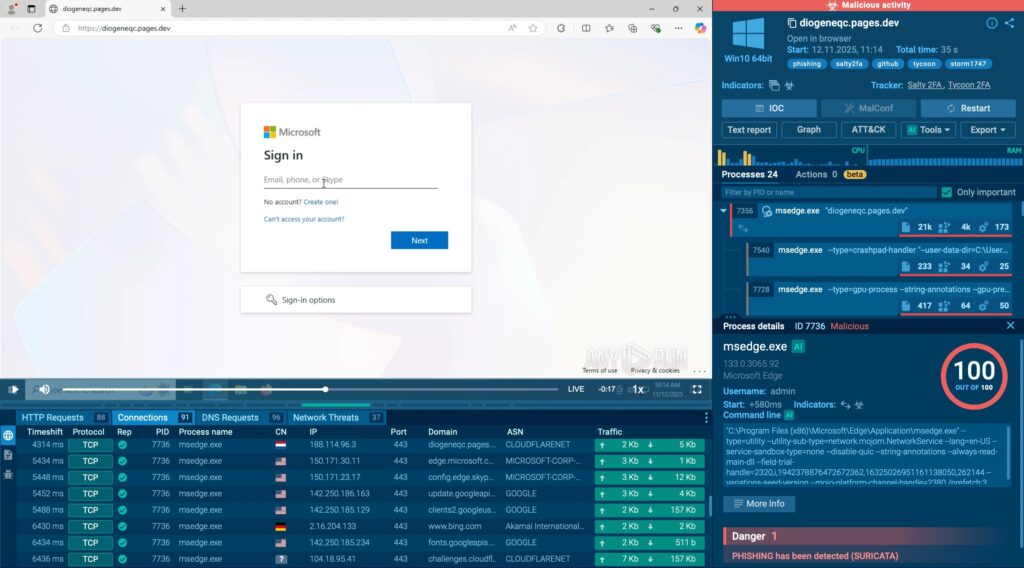
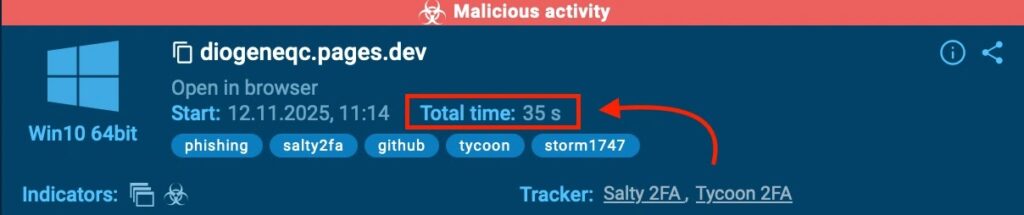
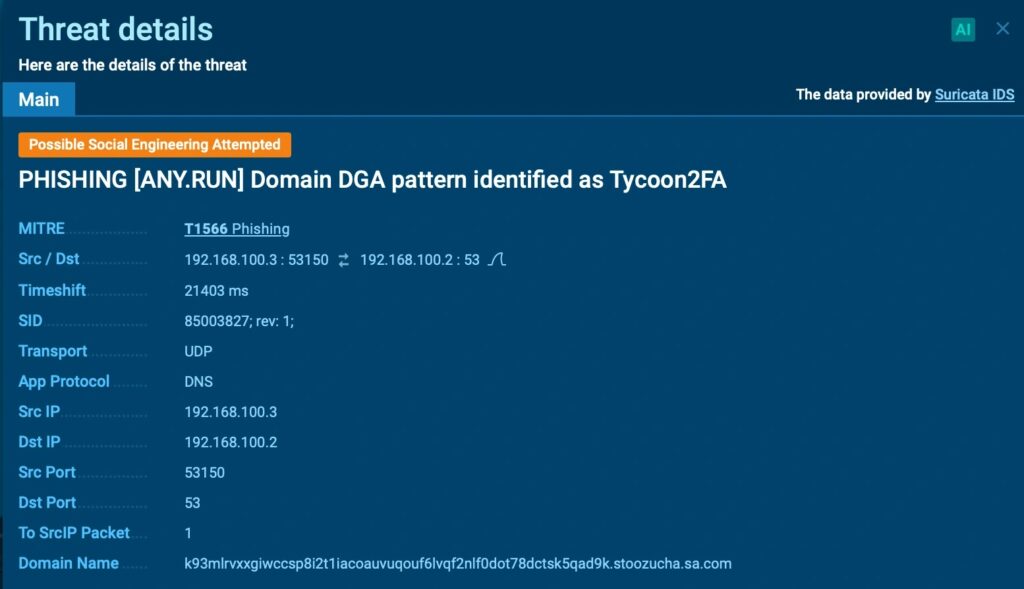
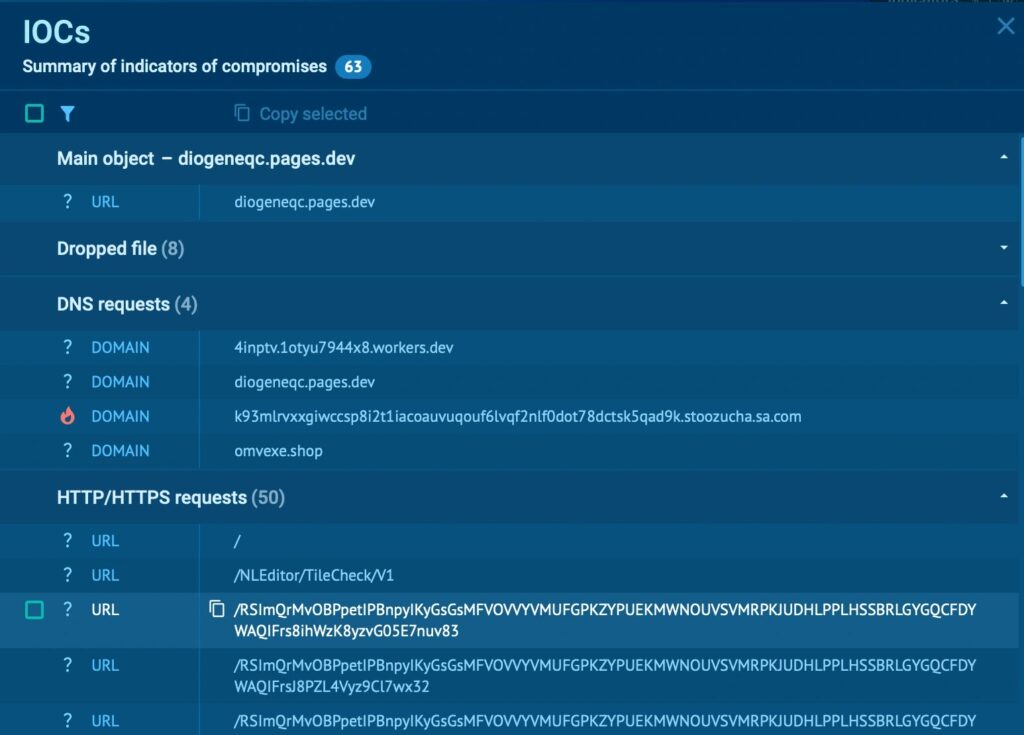
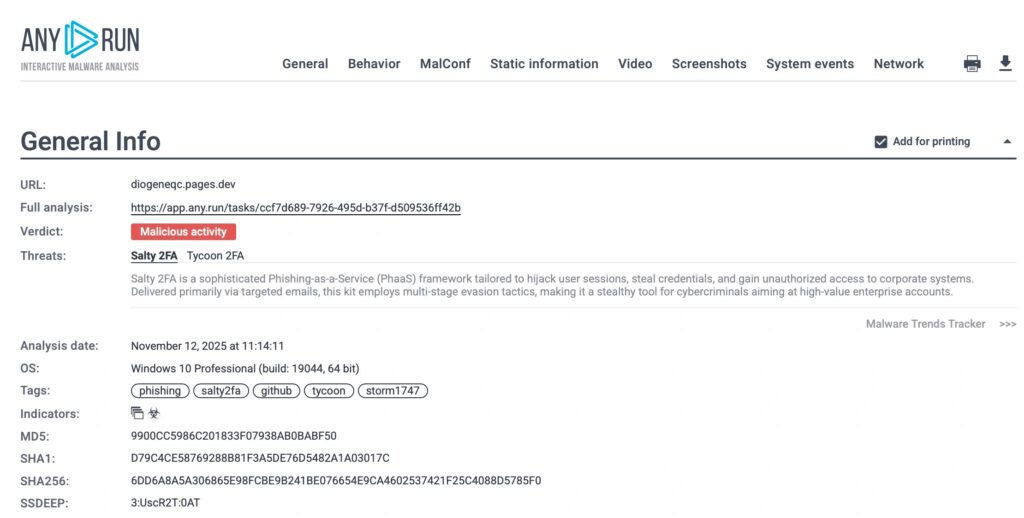
ANY.RUN analyzed a phishkit in 35 seconds. It exposed Salty2FA and Tycoon 2FA chains.
Scale matters. High-volume SOCs save hours daily. Costs drop. Response speeds up.
Time Breakdown: Manual vs. Sandbox
| Step | Manual (Minutes) | Sandbox (Seconds) |
|---|---|---|
| Hash/Rep Check | 5 | 10 |
| Enrichment/Pivots | 10 | 20 |
| Detonation/Logs | 10 | 30 |
| Verdict | 5 | 20 |
| Total | 30 | 80 |
Key Sandbox Benefits
Accelerate triage.
- Real-time process trees and network flows.
- Interactive browsing for phishing.
- Behavior-based verdicts, not just static scans.
- Shareable reports for escalation.
- Integrates with SIEM for automation.
Implementation Steps
Adopt in your SOC.
- Choose interactive platforms like ANY.RUN.
- Train on quick uploads and interactions.
- Set triage rules: Sandbox first for unknowns.
- Integrate APIs for alert feeds.
- Track MTTR metrics pre/post.
FAQ
28 minutes on average, from 30 to 2.
Live processes, connections, redirects, user interactions.
Yes; browse links safely to reveal chains like 2FA stealers.
35-second phishkit takedown:
Free trials at ANY.RUN; integrate with your SIEM.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages