How to scale early threat detection in your SOC without extra staff
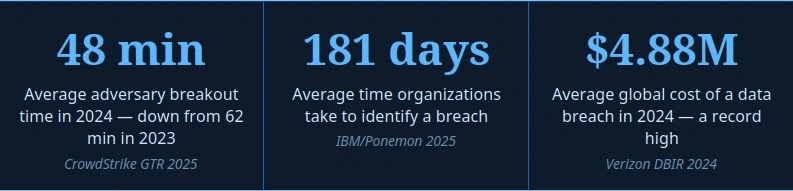
You can improve early threat detection without adding headcount, but only if you reduce analyst drag and push better data into the tools you already own. The fastest attackers now move laterally in 27 seconds in CrowdStrike’s latest reporting, while the average eCrime breakout time fell to 29 minutes in 2025. That leaves very little room for slow triage, stale indicators, or manual enrichment.
That is why the real question is not whether your SOC needs more alerts. It is whether your team can spot the right signal early enough to act. IBM’s 2025 Cost of a Data Breach report says the global average breach cost was $4.4 million, and it also says organizations with extensive use of AI in security saw average savings of $1.9 million compared with those that did not.
Hiring still matters, but it does not solve the speed problem on its own. CyberSeek, supported by NIST’s NICE program, says U.S. employers posted 514,359 cybersecurity job listings over the past 12 months. ISC2 separately says the global cybersecurity workforce gap reached 4.8 million in 2024. In plain terms, demand remains too high for most SOC leaders to expect hiring alone to close coverage gaps.
What actually scales detection
The most practical way to scale early detection is to make each analyst faster, not busier. That usually means three things working together: fresher threat intelligence, better enrichment inside SIEM and EDR workflows, and more automation around routine triage. IBM explicitly says AI-powered security tools and services can reduce alert volume, spot gaps, detect breaches early, and enable faster, more precise responses.
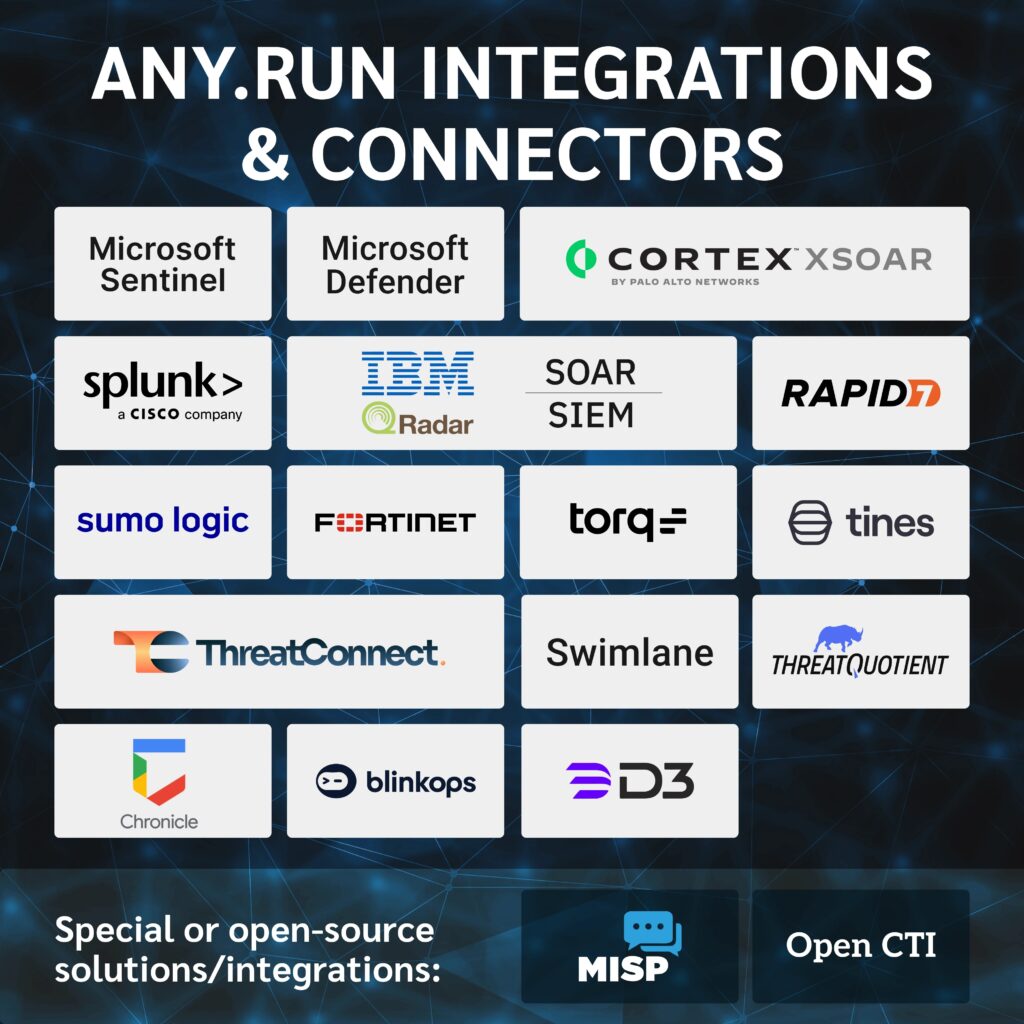
Threat intelligence only helps when it arrives fast enough and with enough context to support a decision. ANY.RUN says its Threat Intelligence Feeds provide real-time malicious IPs, domains, and URLs enriched with sandbox analyses, and that the data comes from millions of malware and phishing investigations contributed by a community of more than 600,000 analysts and 15,000 organizations. The company also says its feeds support STIX/TAXII for easier ingestion into existing tools.
That matters because stale blocklists do not match modern attack tempo. If your SOC imports indicators once a day, or only after a vendor publishes a report, you may still detect threats, but you will not catch enough of them early. The strongest detection programs now treat fresh threat data as an operational input, not a weekly research task. CrowdStrike’s latest report makes the urgency clear by showing both faster breakout times and a continued shift toward malware-free activity that blends into legitimate tooling.
Where most SOC teams lose time
- Too many low-context alerts force analysts to investigate from scratch.
- Threat data arrives late, so detections map to yesterday’s infrastructure, not today’s campaign activity.
- Teams enrich alerts manually across multiple consoles, which increases dwell time during triage. This is an inference based on IBM’s guidance on AI and automation plus ANY.RUN’s emphasis on linked sandbox context.
- Hiring pressure stays high, so senior analysts spend too much time supervising basic work instead of handling high-risk investigations.

What a scalable approach looks like
| SOC problem | What changes without extra staff |
|---|---|
| Too many alerts | Filter and enrich alerts with fresher indicators before they reach analysts |
| Weak prioritization | Add campaign context, malware behavior, and IOC confidence to triage |
| Slow investigation | Link detections to sandbox reports, network activity, and TTP context |
| Manual enrichment | Use STIX/TAXII or API-based ingestion into SIEM, EDR, and SOAR |
| Limited analyst capacity | Automate routine lookups so analysts spend more time on decisions |
This model does not replace analysts. It removes repetitive work that slows them down. Microsoft’s Sentinel documentation also supports this direction by documenting direct ingestion of threat indicators from TAXII servers into Microsoft Sentinel.
How ANY.RUN fits into that model
ANY.RUN’s value proposition is straightforward. The company says its TI Feeds deliver fresh, high-confidence IOCs, link those IOCs to sandbox analysis, and support integrations with common SOC workflows. Its product page also claims 99% unique, high-confidence IOCs are added after validation, while the TAXII documentation says the feeds include network-based IOCs in STIX format delivered via TAXII 2.1, including IP addresses, domain names, and URLs.
That context layer is important. An IOC on its own tells you something touched a suspicious domain or IP. A linked sandbox report tells you what happened next, which processes ran, which network infrastructure was contacted, and which MITRE ATT&CK behaviors appeared during execution. ANY.RUN says its feeds provide that one-click path from indicator to behavior.
Still, teams should keep one point in mind. Vendor-fed intelligence helps most when the SOC already has decent telemetry and a clear response path. If your environment lacks endpoint visibility, identity telemetry, or basic playbooks, fresh IOCs will improve coverage, but they will not fix broken operations by themselves. That is an evidence-based conclusion drawn from IBM’s emphasis on integrated security controls and CrowdStrike’s findings on fast breakout.
Practical steps to improve early detection this quarter
- Review how often your SIEM, EDR, and SOAR platforms ingest new indicators. If the answer is daily or ad hoc, tighten that window.
- Prioritize intelligence sources that include behavioral context, not just raw IOC lists.
- Push enrichment earlier in the workflow so the alert arrives with campaign tags, confidence, and report links attached. This recommendation follows directly from ANY.RUN’s linked analysis model.
- Use automation for lookups, suppression, and first-pass correlation, then reserve humans for validation and containment. IBM says AI-powered security tools can reduce alert volume and enable faster responses.
- Measure success with fewer metrics, not more. Track MTTD, MTTR, percentage of alerts auto-enriched, and analyst time spent per true positive. IBM and CrowdStrike both support a focus on faster identification and containment.
Bottom line
You do not scale early threat detection by asking analysts to read faster. You scale it by making each alert smarter when it reaches them. Fresh threat intelligence, automated enrichment, and direct integration into SIEM, EDR, and SOAR pipelines can raise detection quality without forcing a hiring sprint that most teams cannot win anyway.
If you are evaluating ANY.RUN specifically, the strongest case for it is not just real-time IOCs. It is the combination of real-time IOCs plus sandbox context plus standards-based delivery. That combination gives smaller SOC teams a better shot at acting before attackers pivot.
FAQ
Yes, if it reduces manual triage and improves the quality and freshness of the data flowing into existing tools. IBM says AI-powered security tools can reduce alert volume and detect breaches earlier, while CrowdStrike’s latest data shows attackers are moving too fast for manual-heavy workflows.
Because adversary infrastructure and behavior change quickly, and breakout times keep shrinking. CrowdStrike says the average eCrime breakout time dropped to 29 minutes in 2025, with the fastest case at 27 seconds.
ANY.RUN says the feeds provide real-time malicious IPs, domains, and URLs enriched with sandbox analyses, plus STIX/TAXII support for integration into security stacks.
No. They help most when they plug into a SOC that already has sound telemetry, detection rules, and response processes. They improve signal quality, but they do not replace basic security operations discipline. This conclusion follows from the official sources cited above.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages