Infostealers Drive Brute-Force Attacks on Corporate SSO Gateways

Infostealers now fuel large-scale brute-force attacks on corporate SSO gateways using stolen employee credentials. Threat actors skip software exploits and log in directly with harvested passwords from infected devices. This campaign targets F5 BIG-IP interfaces and similar edge systems.
Defused Cyber first spotted the activity on February 23, 2026. Their honeypots logged POST requests from IP 219.75.254.166, tied to Japan’s OPTAGE Inc. The attacker tested real corporate email-password pairs at high volume. Precision stood out, as many combos linked to big firms and agencies.
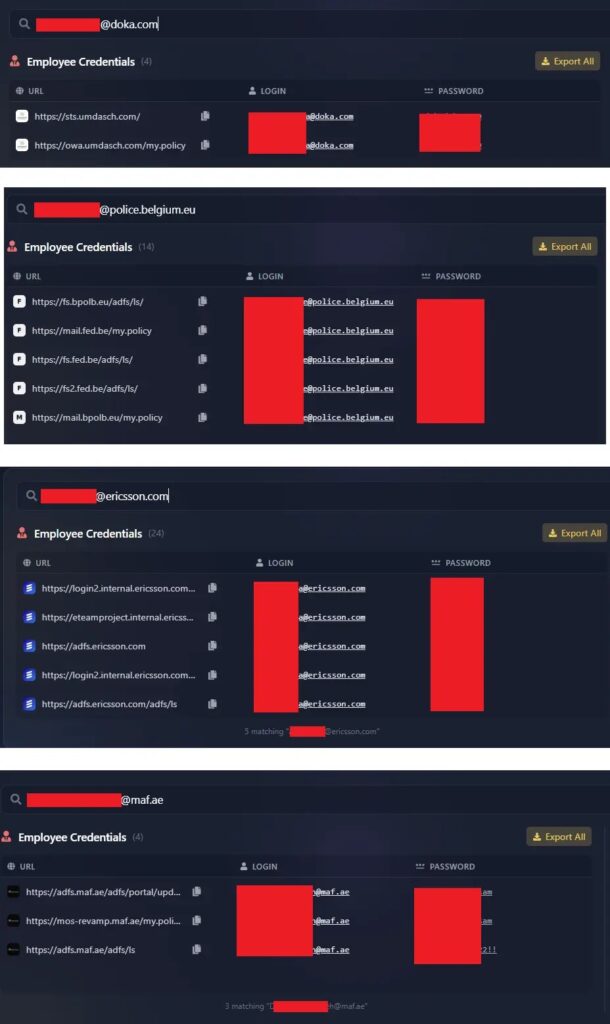
Infostealers.com analysts matched 77% of 70 captured credentials to infostealer logs in Hudson Rock’s database. These came from employee browsers, not F5 breaches. Attackers reuse them against ADFS, STS, and OWA portals. This marks infostealers’ shift to network breaches.
Targeted Organizations
Victims span multinationals and public sectors. Rolls-Royce, Johnson & Johnson, Ericsson, Deloitte, and Cellebrite employees appeared in attack payloads. Law enforcement hit too, including Belgian Police and Queensland Police. Turkish government staff and retail giants also surfaced.
Attackers bet on weak MFA. A single valid login grants footholds. They cast wide nets knowing success rates stay low but profitable.
Attack Infrastructure
The source IP traced to a hijacked Fortinet FortiGate-60E firewall. Open ports 541/tcp and 10443/tcp ran a self-signed SSL cert. Attackers route through compromised edges to hit other edges. This blends stolen IDs with network takeovers for stealth.
Log-to-Lead Pipeline
Infostealers create a “Log-to-Lead” flow. Malware grabs browser credentials like SSO masters from infected machines. Logs aggregate by corporate value and sell to access brokers on dark web markets.
Brokers stuff them into SSO targets until hits occur. “Functional equivalence” powers this. ADFS passwords often double as VPN or gateway keys. Attackers enter via front doors with employee keys.
| Stage | Action | Output |
|---|---|---|
| Infection | Steals browser creds | Raw logs with domains |
| Aggregation | Filters high-value firms | Bundled credential sets |
| Sale | Dark web marketplaces | Packages to brokers |
| Stuffing | Brute-force SSO edges | Network access |
Defense Measures
Enforce phishing-resistant MFA on all SSO and edge devices. Monitor dark web feeds for exposed employee creds. Ban password reuse in policies.
- Deploy endpoint tools to block infostealers early.
- Train staff against browser password saves.
- Audit F5 BIG-IP and ADFS for shared logins.
Defused Cyber tweeted the alert on X. Infostealers.com detailed the pipeline (infostealers.com/article/how-infostealers-industrialize-the-brute-forcing-of-corporate-sso-gateways).
FAQ
Defused Cyber honeypots caught brute-force POSTs to F5 devices on February 23, 2026.
Rolls-Royce, Deloitte, Ericsson, police forces in Belgium and Queensland, plus Turkish ministries.
They harvest browser creds, sell high-value sets, then brokers stuff SSO gateways.
219.75.254.166 from a compromised Japanese FortiGate firewall.
Use phishing-resistant MFA, dark web monitoring, and endpoint detection.
Defused Cyber on X
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages