IPVanish VPN for macOS flaw could let local attackers run code as root

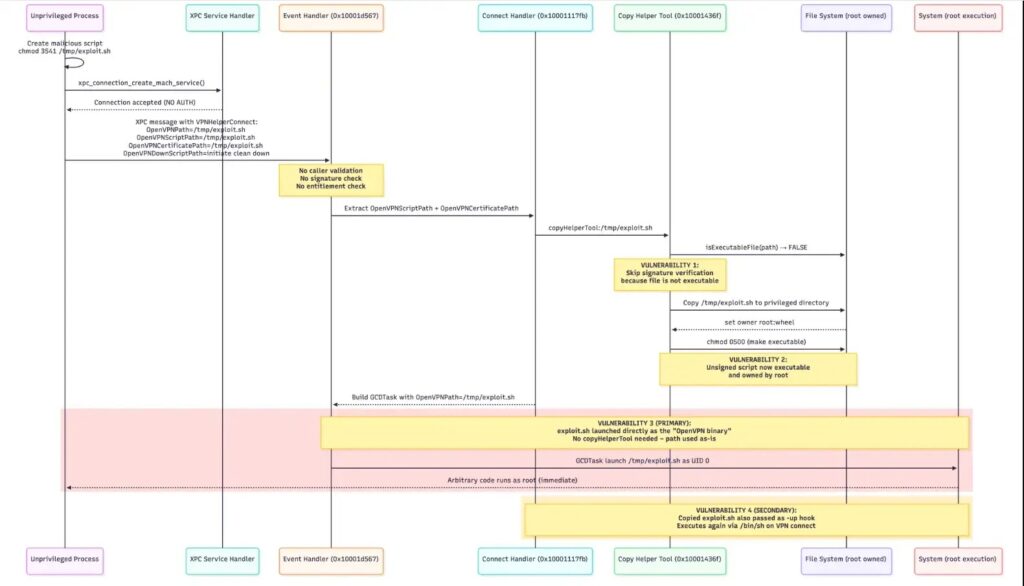
Security researchers have published a new report that claims a local privilege escalation weakness in IPVanish’s macOS app can let an unprivileged user run arbitrary code as root. The write-up says the bug sits in a privileged helper tool named com.ipvanish.osx.vpnhelper, which accepts XPC connections without properly authenticating the caller.
This attack requires local access. An attacker needs the ability to run code on the Mac as a regular user. The report does not describe a remote, over-the-internet exploit path.
The researcher labels the issue CVE-PENDING and assigns it a CVSS 8.8 (High) score in the proof-of-concept output. CVE assignment can take time, so teams should track the vendor response and any eventual CVE record.
What researchers say broke inside the IPVanish macOS design
SecureLayer7 says IPVanish splits its macOS client into a normal user-space app and a root-privileged helper. The helper listens for XPC requests and performs privileged actions. According to the report, the helper does not verify the connecting client’s identity before processing commands.
The report also claims the helper accepts parameters that influence what it launches as root. In the described chain, an attacker provides a path that points to attacker-controlled content and reaches root execution.
This pattern shows up in macOS software more often than it should. Apple provides APIs that let developers require peers to match a specific Team ID or entitlement. If a privileged service does not enforce those checks, any local process may try to talk to it.
Quick facts
| Item | Details |
|---|---|
| Product | IPVanish VPN for macOS |
| Reported component | com.ipvanish.osx.vpnhelper privileged helper |
| Reported issue | Unauthenticated XPC client can trigger privileged actions |
| Attack type | Local privilege escalation |
| User interaction | None reported in the PoC flow |
| CVE status | CVE-PENDING, per researcher report |
Why this matters
A VPN client often runs on laptops that hold corporate credentials, browser sessions, and sensitive files. If a local attacker gains root via a helper tool, they can potentially disable security controls, extract data, or plant persistence. The report’s PoC demonstrates root-owned artifact creation as proof of escalation.
This also matters because the technique targets a common macOS pattern. Many apps ship privileged helpers for networking or device configuration, and XPC authorization mistakes can turn those helpers into escalation paths. Apple’s XPC docs describe XPC services as helper tools for interprocess communication, and Apple provides specific APIs for peer identity and entitlement requirements.
Reported indicators of compromise
These IOCs come from the SecureLayer7 proof-of-concept and show the example paths used during exploitation. Treat them as hunting clues, not confirmation of real-world attacks.
| IOC type | Indicator | Why it matters |
|---|---|---|
| File path | /tmp/ipvanish_exploit.sh | Example attacker payload path in the PoC |
| File path | /Library/Application Support/com.ipvanish.osx.vpnhelper/ | Example privileged destination directory cited in the flow |
| XPC service | com.ipvanish.osx.vpnhelper | Reported vulnerable privileged helper |
What affected users should do now
- Treat this as a local risk. Focus on who can run code locally on the Mac, including shared-user setups and dev workstations.
- Limit local user access. Remove unused accounts and avoid granting local login to untrusted users.
- Watch for suspicious helper interactions. Review macOS logs around privileged helper activity and unexpected process launches that occur near IPVanish usage.
- Reduce exposure while you wait for a vendor fix. If you do not need IPVanish on macOS right now, uninstall it from high-risk machines and remove the helper.
- Keep macOS and security tooling updated. Updates will not fix an app-level bug, but they can reduce follow-on impact.
SecureLayer7 also recommends adding strong caller authentication inside the helper and enforcing signature validation and strict path allowlisting. Those steps target the root cause described in the report.
A historical note worth knowing
This report resembles an older IPVanish macOS escalation issue tracked as CVE-2018-10192, where an insecure XPC service in com.ipvanish.osx.vpnhelper could allow root code execution by manipulating parameters such as OpenVPNPath. That older issue appears in NVD and in a VerSprite advisory for IPVanish for macOS 3.0.11.
That does not prove the 2026 report describes the same bug. It does show the same class of failure, and it raises the stakes for users who assume the helper architecture is safe by default.
FAQ
SecureLayer7 reports a local privilege escalation flaw where an unauthenticated XPC client can send crafted messages to a root-privileged helper tool and trigger root execution.
The report describes a local attack. The attacker needs the ability to run code on the Mac as a normal user.
The report labels it CVE-PENDING. CVE assignment can change quickly after disclosure.
Apple provides XPC APIs that enforce peer Team ID and entitlement requirements. Developers can use them to ensure only the intended signed app can talk to a privileged helper.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages