Iran-linked cyber operations expand alongside electronic warfare as conflict spreads

Iran-linked cyber activity has intensified alongside the wider regional war, with espionage, disruptive attacks, GPS interference, and influence operations now unfolding at the same time. The clearest takeaway is that this is no longer just a conventional military conflict with cyber incidents on the side. Cyber operations and electronic warfare have become part of the main battlespace.
The wider conflict began on February 28, 2026, when joint U.S. and Israeli strikes hit Iran. Since then, the war has spread across the region, with missile and drone attacks, strikes on Gulf targets, and mounting pressure on shipping, energy, and critical infrastructure. Reuters and other major outlets have reported that the confrontation has already moved well beyond Iran and Israel, affecting Gulf states and international business operations.
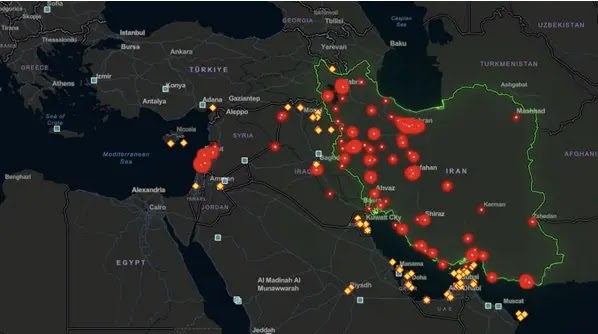
On the cyber side, several security firms and news outlets now describe a blended threat picture. It includes hacktivist attacks, suspected state-linked operations, disruption campaigns against private companies, and espionage activity targeting governments and infrastructure. Palo Alto Networks Unit 42 warned in early March that Iran-related cyber risk had sharply escalated, while Reuters, AP, and The Guardian documented the Handala-linked cyberattack on Stryker as one of the clearest public examples so far.
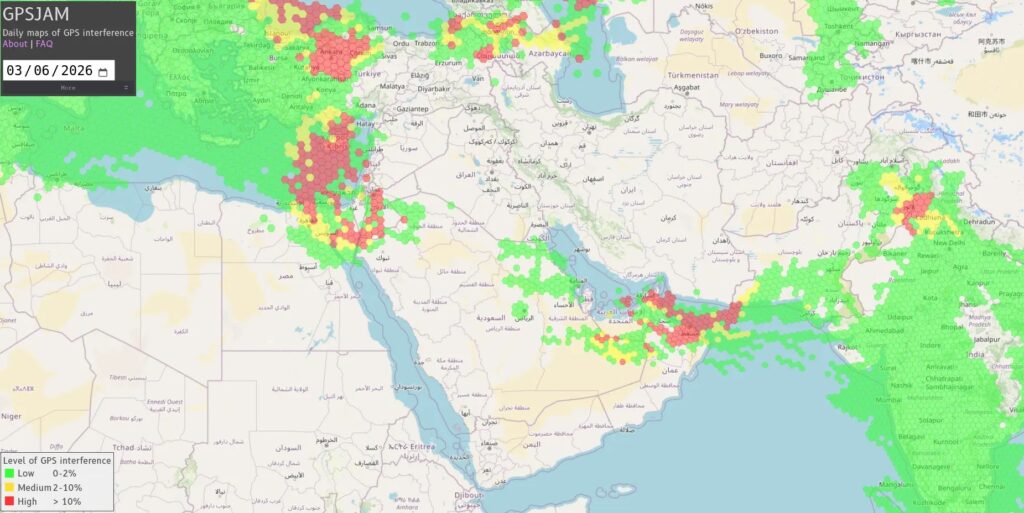
What makes this phase different is the overlap between cyberattacks and electronic warfare. In the Gulf, ship operators and intelligence providers have reported a sharp jump in GPS and AIS interference since the war began. Windward said more than 1,650 vessels experienced interference on March 7, up 55% from the prior week, while Lloyd’s List Intelligence reported 1,735 interference events affecting 655 vessels in the first week of the war.
That interference matters because it affects more than navigation. Modern logistics, fleet management, maritime safety, and some industrial processes depend on accurate positioning data. When spoofing and jamming surge during a live conflict, the line between military pressure and civilian disruption becomes much thinner. Resecurity highlighted that risk in its latest analysis, though some of its more detailed attribution claims remain difficult to verify independently from public evidence.
What has been verified so far
Several core parts of the story are well supported by public reporting.
| Verified development | What we know |
|---|---|
| Wider war began on February 28 | Reuters reported the war began with joint U.S.-Israeli strikes on Iran |
| Major cyber spillover risk | Unit 42 warned of sharply elevated cyber risk tied to Iran |
| Stryker attack | Reuters, AP, and Stryker confirmed a major cyber disruption starting March 11 |
| GPS disruption in Gulf waters | Windward and Lloyd’s List reported major interference affecting hundreds of vessels |
| Regional infrastructure impact | Reuters reported AWS facilities in the UAE and Bahrain suffered strike-related damage |
Where the cyber escalation is showing up
One of the most visible incidents involved Stryker. On March 11, the company said it suffered a cyberattack that disrupted its Microsoft environment globally. Reuters later reported that Stryker said the incident had been contained, although order processing, manufacturing, and shipping were affected. Handala, an Iran-linked group, claimed responsibility and framed the attack as retaliation tied to the war.
This attack stands out because it shows how fast the conflict reached a large civilian company outside the immediate war zone. AP reported that Stryker saw global network disruption, while Reuters said the incident affected operations across its business. That shift raises concern that private companies, especially in healthcare, logistics, shipping, energy, telecom, and cloud services, could increasingly become symbolic or practical targets.
At the same time, defensive alerts have started spreading beyond the Middle East. Reuters reported today that Greek firms began scanning systems after a high-priority advisory from the country’s National Cybersecurity Authority, which warned of elevated cyber risk linked to the Iran war. That shows governments and companies now expect spillover attempts well outside the immediate conflict zone.
Proofpoint also reported that the conflict has already started appearing in phishing lures. In one case, a suspected Pakistan-aligned actor sent emails themed around Gulf security alerts and Iranian retaliation to government-linked targets. That detail matters because it shows the war is already being used as cover material for espionage and social engineering, even outside direct Iranian operations.
Electronic warfare has become a parallel front
The GPS and AIS interference in and around the Persian Gulf may prove just as important as the better-known website attacks and data breaches. Windward reported at least 30 jamming clusters across Saudi Arabia, Kuwait, the UAE, Qatar, Oman, and Iran, while Lloyd’s List said daily vessel disruptions nearly doubled after the war began.
This kind of interference creates operational confusion at scale. Ships can appear to be in impossible locations, routes become harder to trust, and maritime operators must rely on alternative navigation and validation methods. In a conflict centered on Gulf energy flows and the Strait of Hormuz, that gives electronic warfare direct economic and security value.
Reuters also reported that Amazon Web Services said drone strikes damaged facilities in the UAE and Bahrain in early March. That incident shows how physical strikes and digital dependency now collide. A regional cloud facility can become part of the conflict picture just as easily as a port, airfield, or logistics hub.
What remains less certain
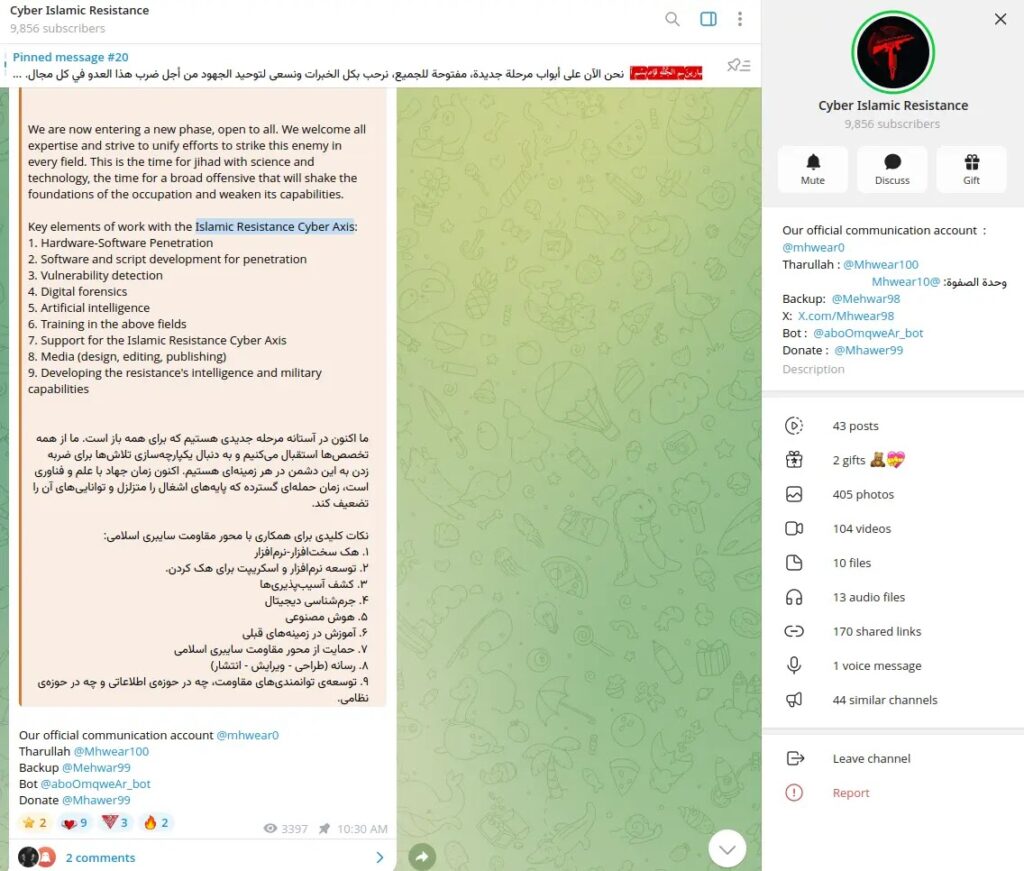
Some of the sample’s most specific claims come from Resecurity’s new report, including references to an “Islamic Resilience Cyber Axis,” an “Electronic Operations Room,” named proxy groups, and detailed targeting narratives. Resecurity did publish those claims, but I could not independently confirm all of them through Reuters, AP, or other primary public reporting before writing this piece. Those details may prove accurate, but they need more public corroboration.
The same caution applies to some highly granular operational claims in the sample, such as exact attribution chains for every group, specific hit lists, and the full scope of drone damage to private infrastructure. A few of those points line up with broader reporting trends, but the full details remain unevenly verified in public sources.
What organizations should do now
- Review internet-facing systems for unusual scanning, login abuse, and web shell activity.
- Harden MFA, especially for admin, VPN, cloud, and email accounts.
- Watch for phishing that references Gulf security alerts, retaliation, shipping disruption, or diplomatic fallout.
- Validate GPS and AIS anomalies with secondary systems where possible.
- Prepare business continuity plans for cloud, shipping, and logistics disruption.
- Segment critical OT and ICS environments from standard corporate networks.
- Monitor for destructive behavior, not just data theft, because retaliation-driven attacks may prioritize disruption.
These steps follow directly from the public reporting on elevated cyber risk, GPS interference, and recent disruptive incidents such as the Stryker attack.
Why this matters beyond the Middle East
This conflict shows how quickly modern war can mix physical force, cyber disruption, electronic warfare, and public messaging into one campaign. A shipping company may face spoofed navigation, a hospital supplier may lose core systems, a government office may get themed phishing, and a cloud provider may deal with both regional outages and physical damage at the same time.
That convergence does not just raise the technical risk. It also raises the pressure on public trust, crisis response, and business continuity. The main lesson from the first weeks of this war is clear: cyber risk no longer sits behind the front line. In many sectors, it is part of the front line.
FAQ
Yes. Reuters, AP, Unit 42, and other public sources have confirmed a rise in cyber risk, including the Stryker attack and broader warnings tied to the conflict.
Yes. Windward and Lloyd’s List Intelligence both reported sharp increases in GPS and AIS disruption affecting hundreds of vessels after the war began.
A Handala-linked attack hit Stryker on March 11. Stryker confirmed the disruption, and Reuters reported the Iran-linked claim of responsibility.
No. Some group names and coordination claims come primarily from Resecurity’s report and still need broader independent confirmation in public reporting.
Shipping, energy, healthcare, telecom, government, logistics, and cloud-linked operations look especially exposed based on the incidents and warnings published so far.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages