Iranian APT activity rises as Middle East conflict widens, putting critical infrastructure on alert

Critical infrastructure operators should treat the current Iran-related cyber risk as elevated. New research from Nozomi Networks says it is already seeing a systematic increase in activity tied to Iran-linked threat actors, with manufacturing and transportation the most targeted sectors so far. At the same time, Nozomi stresses that the data is still early and not enough has been collected yet to draw definitive conclusions.
That caution matters. The sample article overstates a few points. The strongest public evidence right now supports this narrower conclusion: Iran-linked cyber risk is rising during a fast-moving regional war, but much of the visible activity still appears to be early-stage intrusion work, reconnaissance, opportunistic probing, and hacktivist noise rather than confirmed large-scale destructive attacks on critical infrastructure.
The geopolitical backdrop is real and severe. Reuters reported on March 3, 2026 that Israel’s U.N. envoy said the United States and Israel had launched strikes on Iran and now claimed control over most Iranian airspace, while the conflict had already spread beyond Iran and Israel. Nozomi’s March 2 threat brief places its cyber warning in that same wartime context.
What Nozomi says it is seeing
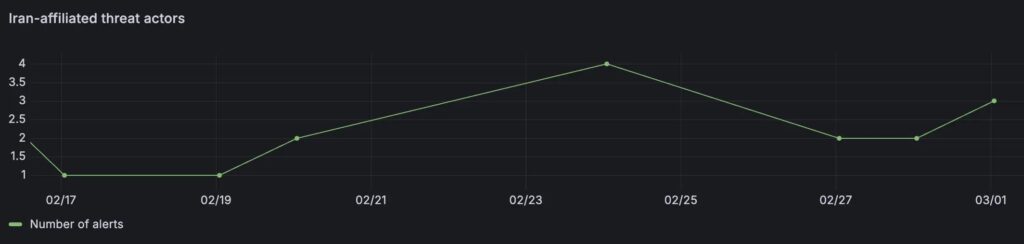
Nozomi says it has tracked an increase in alerts associated with MuddyWater, OilRig, APT33, and UNC1549 over the past two weeks. It says manufacturing and transportation are the most targeted sectors in its telemetry at the moment.
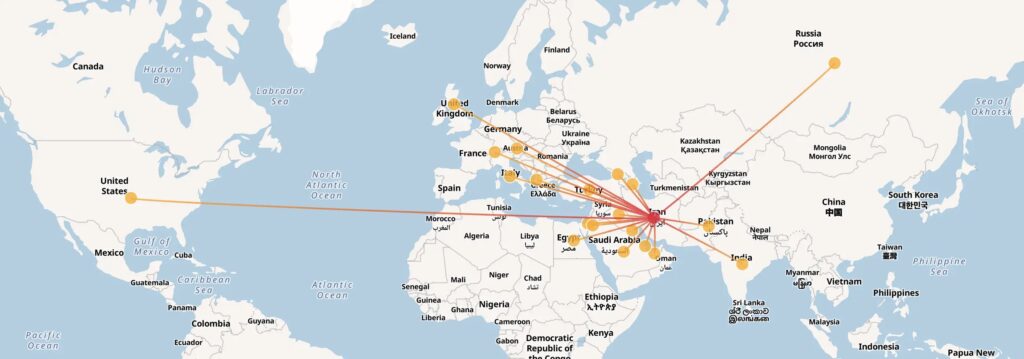
The report does not say these groups have already moved into widespread destructive operations. Instead, Nozomi says the current pattern points to attackers still being in an exploratory and positioning phase. It highlights default credential abuse, valid account usage, brute force, and scanning as the top signals in the region.
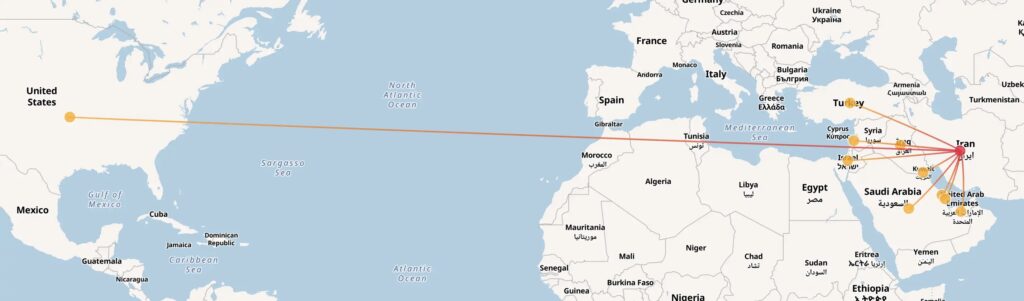
That lines up with outside reporting. Palo Alto Networks Unit 42 says activity tied to Iran is likely to intensify and tells defenders to harden internet-facing assets, improve phishing resilience, and prepare for both real attacks and exaggerated breach claims. Computer Weekly also reported on March 4 that hacktivist activity is currently louder than classic state APT activity, giving defenders a short but valuable window to tighten controls.

Who the main threat groups are
| Threat group | What Nozomi says |
|---|---|
| MuddyWater | State-aligned espionage actor tied to MOIS, known for phishing, credential abuse, and use of legitimate admin tools |
| OilRig | Long-running Iranian espionage group that targets government, finance, telecom, defense, and energy |
| APT33 | Group linked to Iran’s strategic objectives, with history in aerospace, aviation, energy, manufacturing, and government |
| UNC1549 | Actor overlapping with CURIUM / Tortoise Shell / Crimson Sandstorm, active against defense, aerospace, telecom, and regional government |
Why critical infrastructure teams should care now
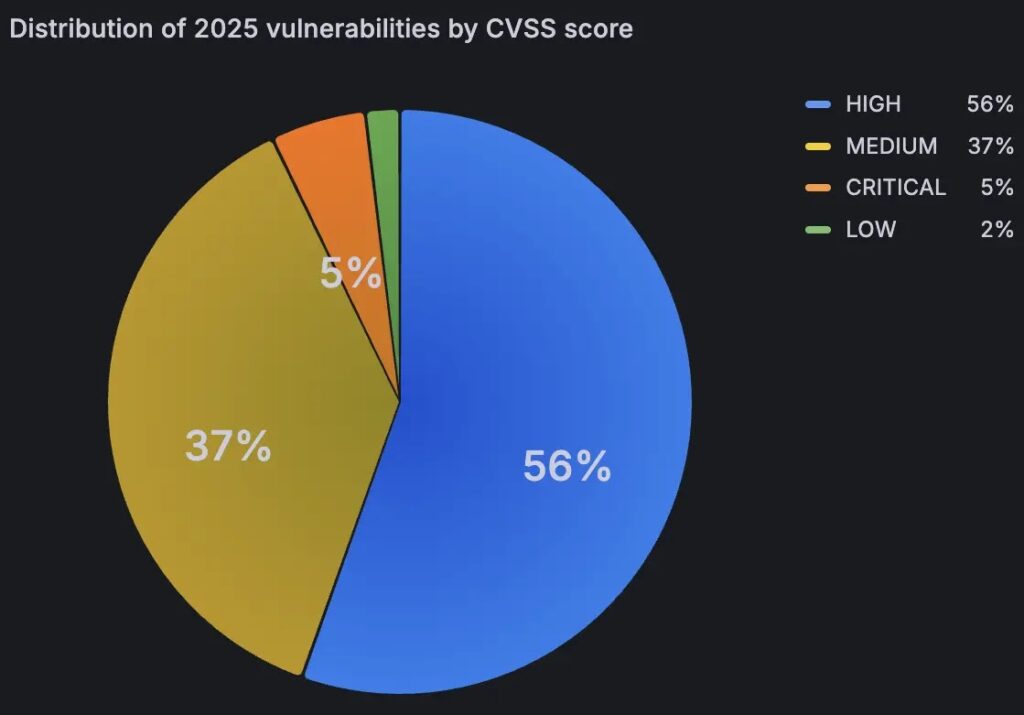
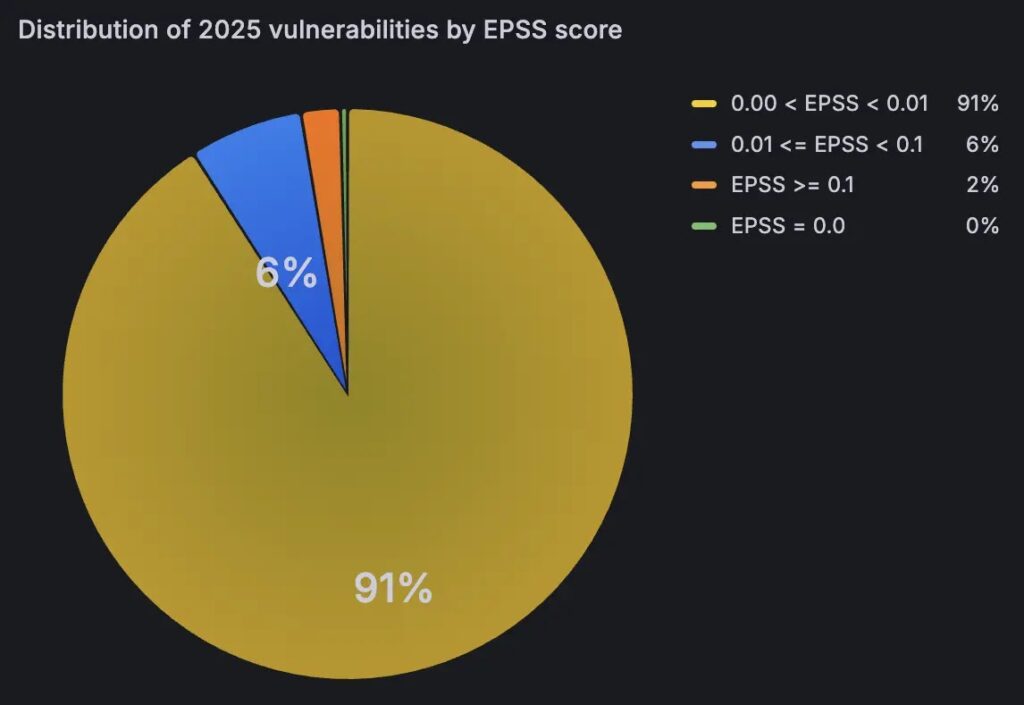
Nozomi says organizations in the Middle East face a weaker exposure profile than the global average in at least one important area. In its telemetry, 61% of vulnerabilities discovered in 2025 carried high or critical CVSS scores, versus a 48% global average. It also says about 8% had an EPSS score above 1%, versus a 4% global average.
That does not prove compromise. It does show a wider attack surface at the exact moment when Iran-linked actors and aligned hacktivists have more motive to probe exposed systems. If defenders wait until activity turns overtly destructive, they may lose the best chance to stop it.
What defenders should do right now
- Change default credentials immediately, especially on OT, IoT, VPN, edge, and remote-access systems. Nozomi says default credential abuse is one of the top patterns it is seeing.
- Tighten identity controls and monitor valid-account use. The current activity pattern suggests attackers want quiet access before they escalate.
- Patch internet-facing assets fast. Unit 42 specifically calls out websites, VPN gateways, and cloud assets as priority surfaces.
- Segment IT and OT networks and verify the segmentation actually works. Nozomi warns that air-gapping alone is not enough.
- Raise alert sensitivity for scanning, brute force, and authenticated reconnaissance. That is where the current signal sits.
- Prepare for phishing tied to war themes, disruption claims, and data leaks. Unit 42 and Computer Weekly both note that hacktivist and state-linked operators may mix real attacks with exaggeration and psychological pressure.
- Review business continuity and incident response plans now, not after a disruptive event. Unit 42 explicitly recommends this.
What this likely means over the next few days
The visible pattern suggests many Iranian-linked actors still aim to map networks, keep access, and identify high-value targets before they move to bigger effects. Nozomi says this stage often comes before privilege escalation, data exfiltration, and operational disruption. Computer Weekly’s reporting points in the same direction, noting that the quiet period for top-tier espionage actors may not last long.
So the real takeaway is not that critical infrastructure is already under mass cyberattack everywhere. It is that defenders appear to be in a short pre-disruption window, and that window may close quickly if the regional war continues to expand.
FAQ
Yes, public reporting says the risk is elevated and Nozomi says it sees increased Iran-linked activity. But Nozomi also says it is still too early to draw firm conclusions about the full scale of the campaign.
Nozomi says manufacturing and transportation are the most targeted sectors in its current telemetry.
Public evidence does not yet show broad destructive operations from the APT groups named in the sample. Nozomi says the current TTP pattern looks more like reconnaissance and early positioning.
Default credential abuse, valid-account use, brute force, scanning, unusual authentication patterns, and probing of exposed edge systems are the clearest signals highlighted by Nozomi and Unit 42.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages