What Is Double VPN? [Beginner-Friendly]
Have you ever used a VPN and felt it’s still not safe to go on the internet? If you have, you’re not alone.
Some users consider basic VPN connections insufficient. Although they encrypt your traffic and mask your real IP address, they’re not completely failproof.
But that’s what advanced features are for — like a double or multi-hop VPN. Let’s take a deeper look into what makes it so special!
What is a double VPN?
Double VPN (or multi-hop) allows you to route your traffic through two remote servers in different locations. Conversely, a normal connection works with one server.
Depending on your service provider, you may be able to tailor your multi-hop route or select from a pre-configured list.
Either way, your IP address changes twice. As your traffic goes from the first to the second remote hardware, it passes through a secure tunnel encapsulated by another level of encryption.
Want to know the best part?
Hacking this type of connection is nearly impossible. It would require guessing two fake IPs and peeling away a double layer of military-grade encryption.
It’s also perfect for dodging censorship in restrictive countries.
How does double VPN work?
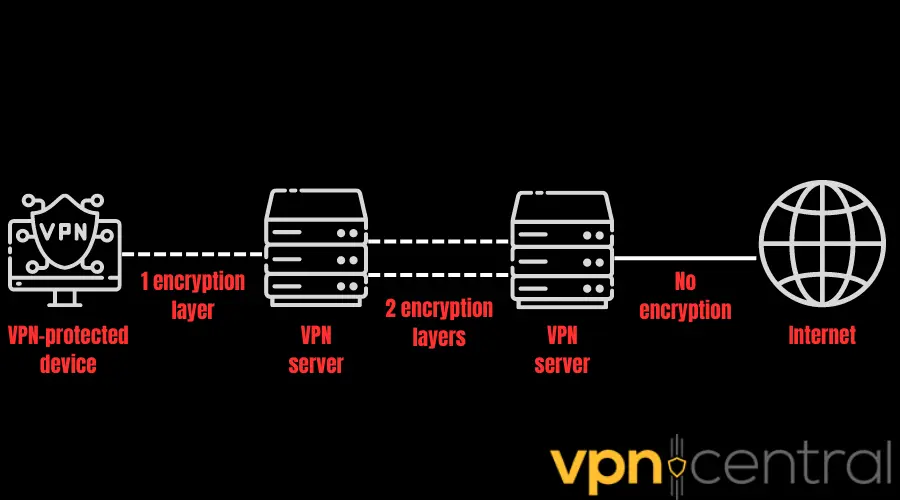
Multi-hop generally works like a normal VPN connection. The only difference is your traffic has to go through two remote servers before reaching the internet.
Here’s how it goes:
- Your VPN software establishes an encrypted tunnel for your traffic.
- Your data reaches the first server, replacing your IP with its own and creating another layer of encryption.
- The second remote server converts your double-encrypted data into plain text and ties its own IP to it.
- The target website responds to the second server’s IP, remaining clueless about your actual location.
- The process repeats itself in reverse as your traffic travels back to your device.
Here’s an illustration of a double VPN connection:
In theory, you can involve three or more servers with VPN chaining. However, your connection speed will plummet with each additional hop.
Double VPN vs normal VPN connection
If you compare how traffic flows through double and normal VPN connections, you’ll see one glaring difference: the number of remote servers. The former involves multiple pieces of hardware, whereas the latter only has one.
Normally, when you connect to a VPN, your traffic passes through a remote server first. It hides your real IP address and replaces it with its own. This way, the site or service you visit remains clueless about your device, especially its physical location.
Not only that, but your VPN software encrypts your data. Unless the snooper is capable enough to decode the best-kept military secrets, it won’t be able to decipher what you’re doing online even if it intercepts your traffic.
When you use double VPN, the protection you get increases twofold. It multiplies the level of IP masking and encryption your traffic goes through, concealing your identity and activity more effectively.
But here’s the flip side:
Double VPN can raise latency. That’s because of the greater distance your data has to travel when hopping on two servers housed in different locations.
Plus, encrypted traffic moves slower than plain text. So, you can imagine how bandwidth-heavy it is to send data through two layers of military-grade encryption.
To summarize the difference between normal and double VPN connections, have a look at this roundup:
| Masked IP | Encryption layer | Speed loss | Server locations | |
| Normal VPN connection | 1 | 1 | Tolerable, minimal, or potentially none | Abundant |
| Double VPN connection | 2 or more | 2 or more | Noticeable or potentially severe | Generally limited |
Should you use a double VPN?
You should use a double VPN only when you really have to prioritize your privacy and security.
For example, it’s a great tool for avoiding censorship in highly restrictive environments. You can never be too careful as an investigative journalist, an activist, or a whistleblower.
Additionally, many governments control the flow of information and news available to their citizens. You can rely on a double VPN to hide your tracks when accessing prohibited or blocked sites.
Multi-hop also comes in handy when you want to access content on platforms with sophisticated security systems. They can easily identify normal VPN connections.
Still, there are situations where a double VPN is definitely overkill.
It’s not suited for casual web browsing. Even on public Wi-Fi networks, a normal VPN will be more than enough.
Moreover, double VPN and high-bandwidth activities don’t mix. When gaming, streaming, and torrenting, using this feature can be counterproductive. It drives down internet connection speeds too much.
How to use a double VPN?
Here’s how to use a double VPN with Surfshark as an example:
1. Go to Surfshark’s site to subscribe and set up an account.
2. Install its Android VPN app.
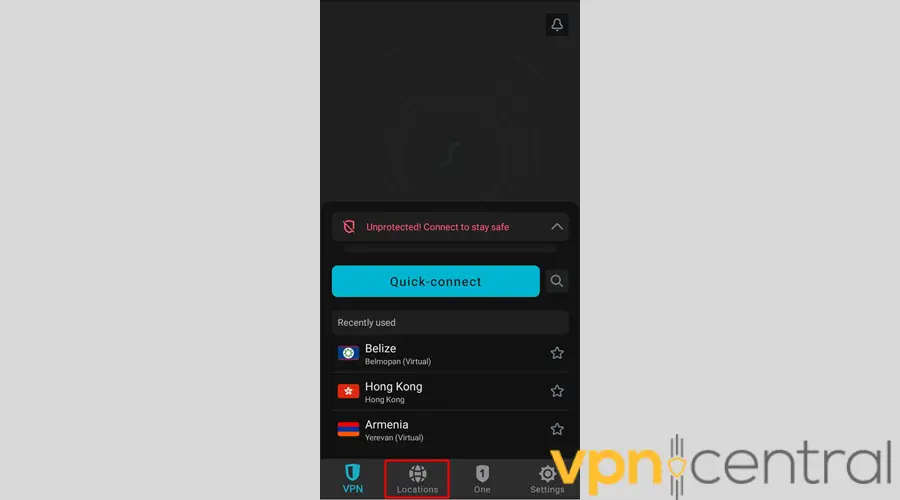
3. Launch your VPN software.
4. Proceed to Locations.
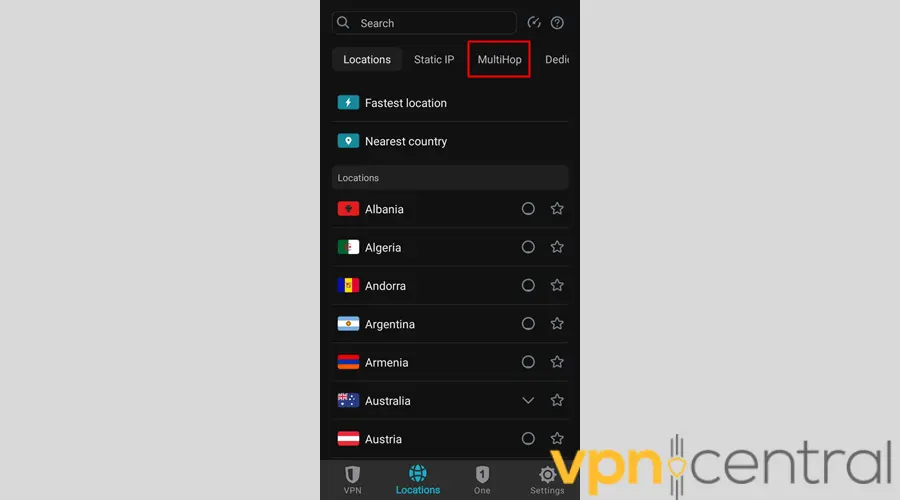
5. Go to MultiHop.
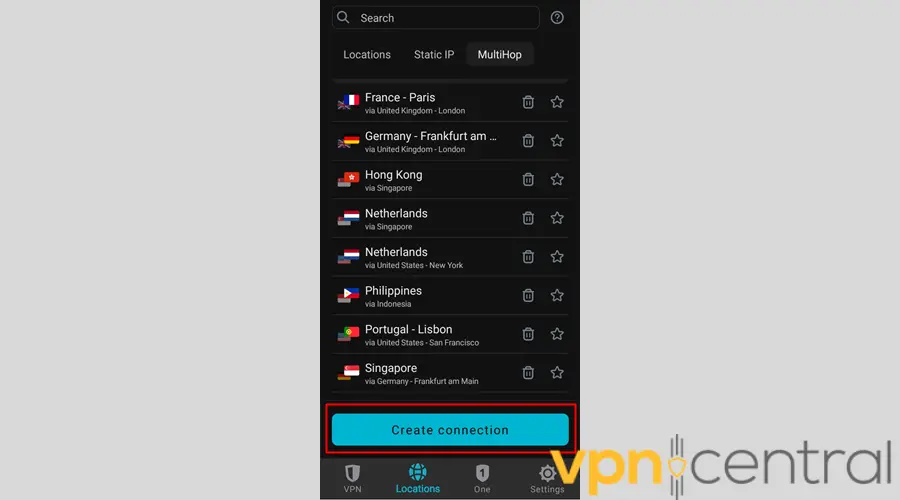
6. If you prefer creating your double VPN route from scratch, select Create connection.
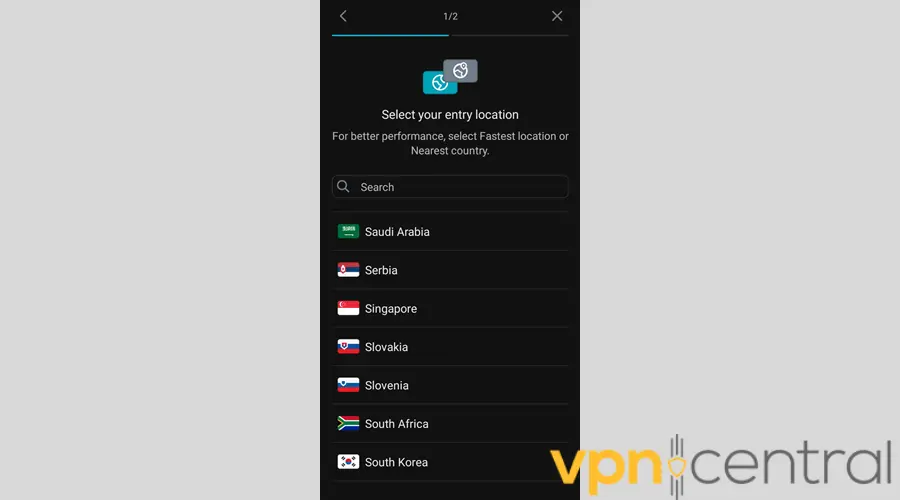
7. Pick a city or a country as your entry location.
8. Choose your exit location.
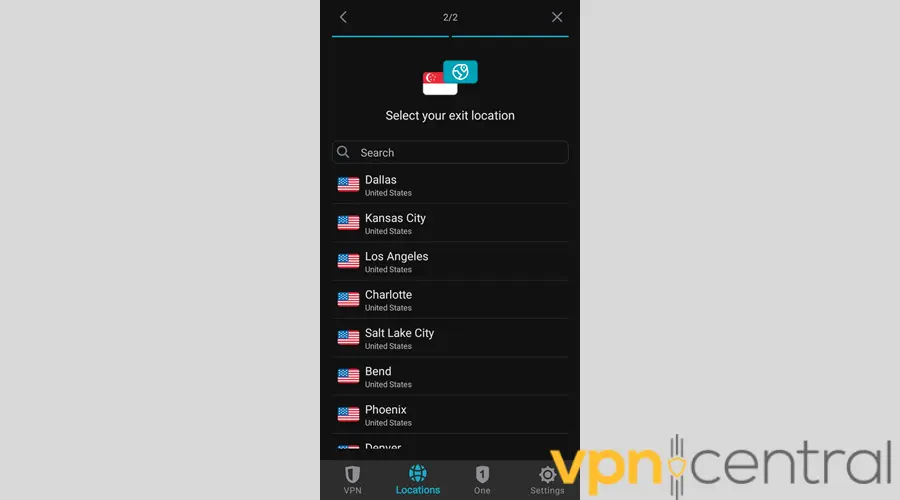
9. Tap Connect and you’re done!
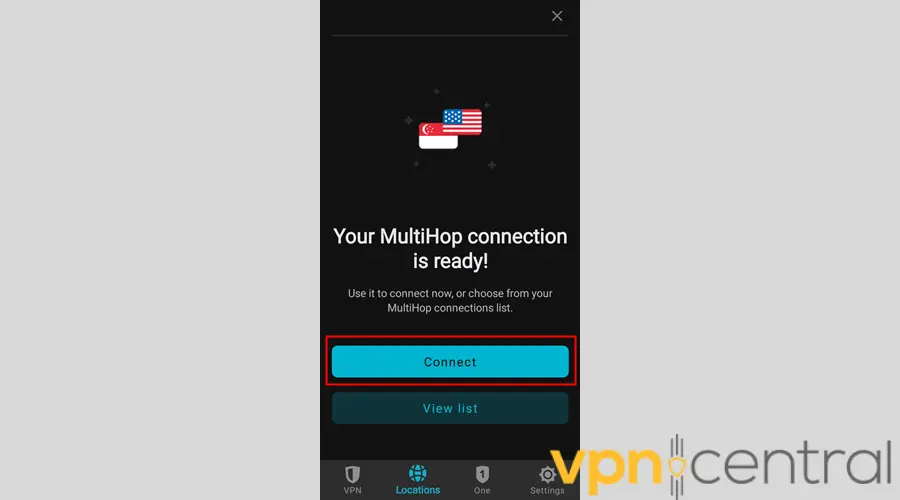
The steps for Windows, Linux, iPhone, and Mac can vary, but they’re generally similar.
Double VPN benefits
The two undisputed benefits of double VPN are increased privacy and enhanced security.
Let’s expand on both of them:
Increased privacy
Hiding your activity behind a pair of geographically distant VPN servers is among the surest routes to online anonymity. Remember: only the first server communicates directly with your device. So, the one after it knows nothing about you.
If a malicious party wants to find your real IP, it’ll have to compromise all of the servers in your double VPN connection. On top of that, the snoop will have to pray that your VPN vendor logs data and doesn’t auto-delete it after every server reboot.
Enhanced security
To say that cracking two layers of encryption is difficult is a massive understatement. Most VPNs use AES-256 encryption, which is what militaries and government institutions utilize to safeguard classified data.
If you seriously want to protect yourself from hackers, double VPN is the way to go.
When to use Double VPN
Double VPN makes sense when you need extra protection from cyberattacks and when you have to get around intense government censorship.
Among the biggest beneficiaries of this feature are journalists researching sensitive topics. If you need to hide the identity of your valuable sources like whistleblowers and informants, you shouldn’t skimp on IP masking and encryption.
The other user groups that would benefit the most from double VPN are political activists wanting to expose corrupt leaders.
Practicing freedom of speech where it’s a crime to offend the authorities can be dangerous for you and your loved ones. So if you want to speak the truth without putting anyone at risk, using a double VPN won’t be overkill.
When not to use Double VPN
Double VPN doesn’t make sense in high-bandwidth activities such as gaming, streaming, and P2P networking.
Don’t get it twisted: you may be able to play games, stream geo-restricted shows, and share files over a P2P network using this feature. But you can do the same by masking your IP and encrypting your traffic once. In fact, major VPN vendors can provide you with specialized servers for each activity.
Losing a considerable percentage of your base internet speed is a given when you use double VPN. So, it would be unwise to subject yourself to such an inconvenience without getting any added benefits.
Is double VPN Safe?
Yes, a double VPN is safe. In fact, it’s so safe that it’s the perfect solution for journalists, activists, whistleblowers, and informants who risk their lives doing what they believe is right.
Here’s what makes it so secure:
In this type of connection, your traffic is protected by two VPN servers instead of one. Your data gets scrambled once as it leaves your device and then again as it goes out of the first remote server. That’s two levels of encryption for you.
As a result, your traffic travels through a tunnel within a tunnel. If the outer layer falls apart, the inner one will continue to render your data unintelligible to observers.
Of course, encrypted data is only as secure as the strength of the protocol used to scramble it.
The good news is that the best double VPN vendors use 256-bit encryption, which is as secure as you can get.
However, this is just the tip of the iceberg.
In VPN use, true privacy and security stem from:
- Non–Fourteen Eyes headquarters – A service provider that operates in a country that doesn’t commit mass surveillance is privacy-friendly. The best cases in point are the British Virgin Islands, Panama, and Switzerland.
- Verified no data logging – Credible providers commission third-party system audits to verify that their no-logs policies hold water. Without that, a VPN company advertising “no data logging” may just be paying lip service.
- RAM-only storage – Servers that run on RAM automatically erase their memory the moment they get unplugged. As a result, the authorities can’t confiscate them without deleting their contents.
In conclusion, security is this feature’s calling card. But its safety ultimately depends on its provider.
Is double VPN good for gaming?
No, double VPN isn’t good for gaming.
Make no mistake about it, you could play games through a double VPN configuration just fine. Doing so can ease your security concerns.
But will you have a smooth gaming experience? Most likely, not.
Pros of using double VPN for gaming
The pros of using double VPN for gaming are increased privacy and security.
Forget about the nefarious players you might be playing with. Your own government, with all of its resources, may not be able to link your gaming traffic back to your device.
Remember: double VPN servers are usually located in different regions. So, tracing your traffic means checking the logs of both pieces of hardware in jurisdictions that may or may not be friendly toward your country or territory.
And that’s assuming that your provider keeps activity and connection records, which most reputable VPNs don’t.
From a security standpoint, double VPN can truly help boost your defenses against many cyber attacks and phishing attempts.
Using a secure tunneling protocol like WireGuard, OpenVPN, or IKEv2, you can encrypt your gaming data the way military organizations and banking institutions obscure confidential information.
What are the downsides?
The downsides of using double VPN for gaming are significant speed loss and limited server options.
Double VPN raises latency no matter how you slice it. Even worse, you typically don’t have the luxury to choose where to route your data.
At best, most service providers that offer double VPN only give you a fixed list of server location pairs. If none of them are close to where you are physically, you can do little to reduce lag.
Granted, many VPNs these days have been adopting 10Gbps connectivity, which promises faster speeds. But only a few have fully upgraded their networks.
Just like any VPN hardware, double VPN–configured servers have finite resources. So, they’re prone to server overloads too.
Summary
In a nutshell:
Multi-hop VPN hides your traffic behind two separate servers. As a result, it cloaks your real IP twice for greater privacy. Although it has many benefits, it’s not ideal for bandwidth-heavy activities.
So, what is double VPN really used for?
It’s a neat solution for resisting advanced surveillance and state-sponsored censorship. So if you’re a casual internet user, you most likely won’t appreciate it. But if you take risks as an activist, you’ll find it a reliable tool.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages