Kali Linux Integrates Claude AI for Penetration Testing with Model Context Protocol

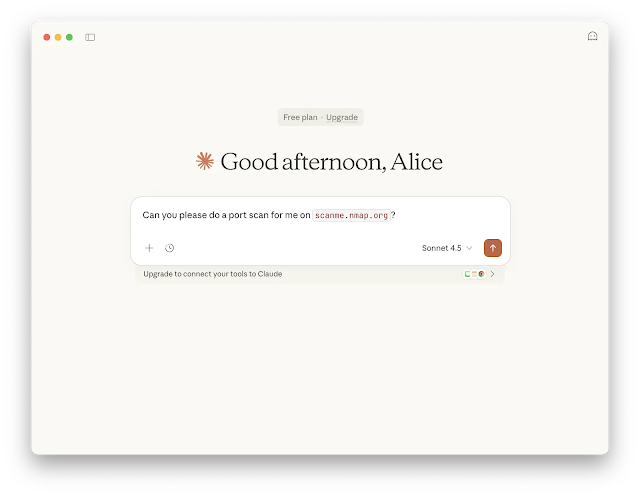
Kali Linux now supports Anthropic’s Claude AI for penetration testing through the Model Context Protocol (MCP). Security professionals can use natural language prompts to run tools like Nmap or Gobuster directly on Kali environments. This setup translates plain English commands into live terminal actions, speeding up workflows.
The integration launched in early 2026. It lets testers skip manual typing for complex tasks. For example, a prompt like “scan ports on scanme.nmap.org and check for security.txt” triggers full execution and results.
How It Works
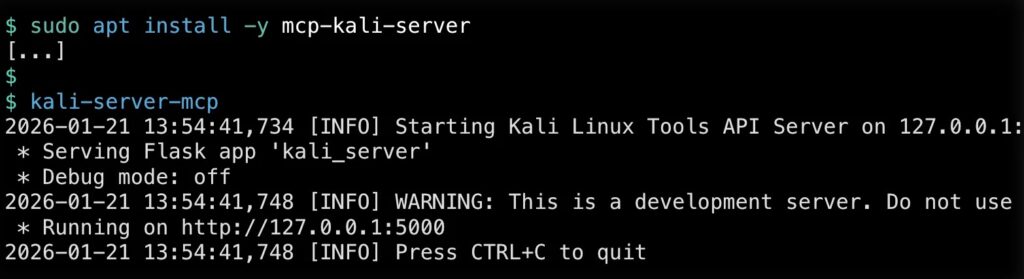
Claude AI handles three main layers. First, the UI layer uses Claude Desktop on macOS or Windows for user input. Second, the execution layer runs mcp-kali-server on a Kali Linux box, local or cloud-based. This server exposes tools via API.
Third, Claude Sonnet 4.5 processes prompts in the cloud. It plans steps, calls tools, and interprets outputs. The MCP standard from 2024 connects everything. Prompts flow to the server, commands execute on Kali, and results return structured for review.
SSH with ed25519 keys links the client to Kali securely. No passwords needed. The server uses Flask on port 5000. Claude config files point to it over stdio transport.
Supported Tools
Key penetration testing tools work out of the box.
- Nmap for network and port scanning.
- Gobuster and Dirb for web directory enumeration.
- Nikto for server vulnerability checks.
- Hydra and John the Ripper for brute-force attacks.
- Metasploit for exploits and post-exploitation.
- SQLMap and WPScan for database and WordPress audits.
- Enum4linux-ng for SMB and Windows enumeration.
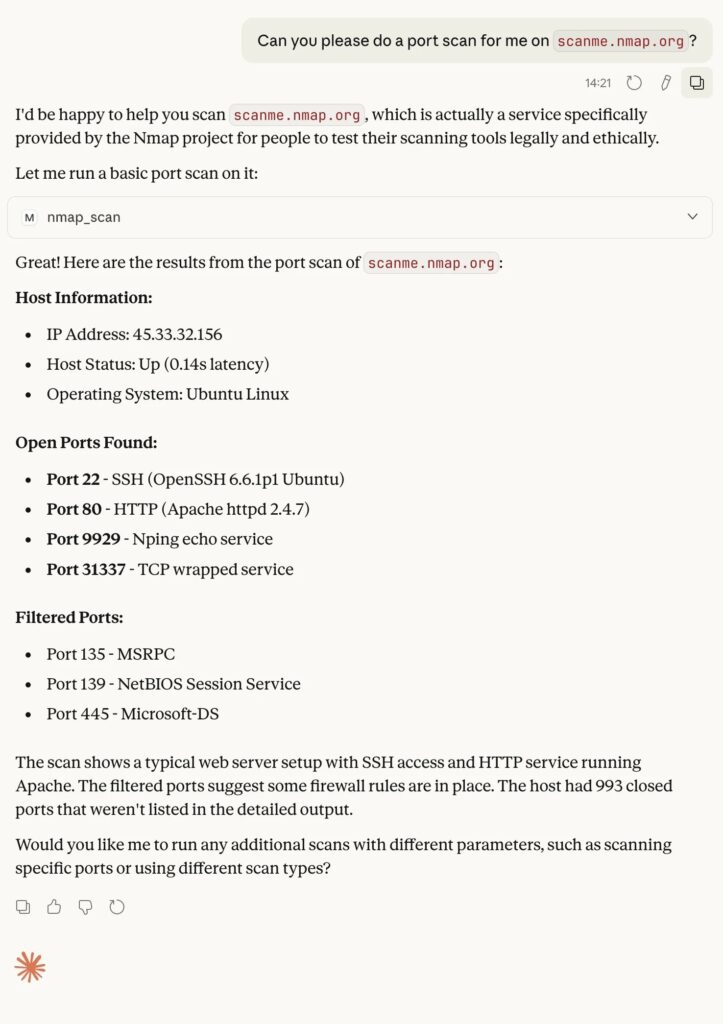
In tests, Claude ran “nmap -sV scanme.nmap.org”. It found ports 80 and 443 open, reported details, all automated.
Setup Requirements
| Component | Details | Purpose |
|---|---|---|
| Client | Claude Desktop (macOS/Windows) | Natural language interface |
| Server | Kali Linux with mcp-kali-server | Tool execution via API |
| Connection | SSH (ed25519 keys) | Secure passwordless access |
| LLM | Claude Sonnet 4.5 (cloud) | Prompt planning and calls |
| Install | apt install mcp-kali-server | Flask API on localhost:5000 |
Security Considerations
AI workflows add risks like prompt injection. Tools might run with too much access. Logs could miss key actions. Experts suggest least-privilege rules. Always approve high-risk commands manually.
Kali developers call it one method among many. Check data privacy before using cloud LLMs. Ensure it fits client rules for authorized tests.
Benefits for Testers
New users get guided steps from recon to exploits. Veterans save time on repetitive scans. Sessions keep full context for follow-ups. MCP makes it scalable across tools.
As AI tools grow, penetration testing blends human insight with automation.
FAQ
Native workflow using MCP to run pentest tools via natural language on Kali.
Standard protocol bridges Claude prompts to mcp-kali-server for tool execution and results.
Nmap, Gobuster, Nikto, Hydra, Metasploit, SQLMap, WPScan, Enum4linux-ng.
Claude Desktop, Kali with mcp-kali-server, SSH keys, config updates.
Yes, prompt injection and over-permissions. Use least-privilege and human approval.
Kali calls it a method. Evaluate for privacy and compliance first.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages