Leak Bazaar turns stolen corporate data into a more organized criminal marketplace
A new cybercrime service called Leak Bazaar appears to show how data extortion is evolving beyond the usual leak-site model. Instead of just dumping stolen files online, the platform says it can process raw corporate data, clean it up, sort it into useful categories, and package it for criminal buyers. That makes the stolen information easier to resell and potentially more valuable over time.
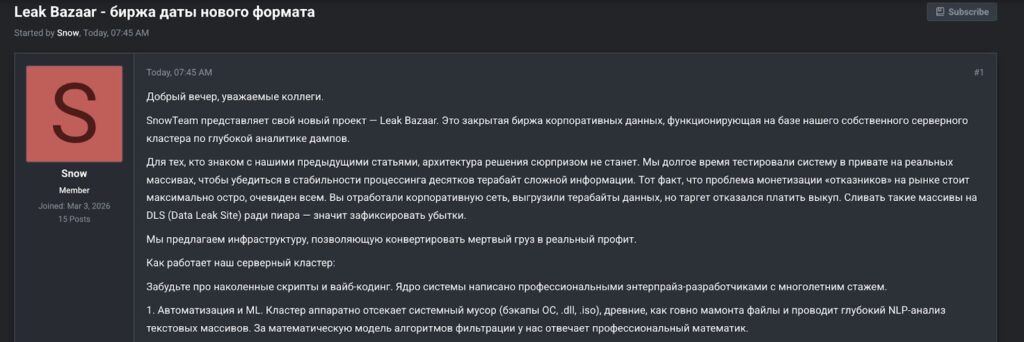
According to Flare, Leak Bazaar was advertised on March 25 by a threat actor known as Snow from SnowTeam on the Russian-speaking TierOne forum. Flare says the platform’s hidden service went live the same day and presents itself as a post-exfiltration processing service rather than a traditional leak blog.
That distinction matters. In many ransomware and data theft cases, raw archives contain huge amounts of noise, such as duplicate files, system junk, damaged exports, and bulky database dumps that buyers cannot use quickly. Leak Bazaar claims it solves that problem by turning messy stolen data into structured intelligence products that are easier to search, price, and sell.
How Leak Bazaar says it works
Flare says the service markets itself as a mix of automation and analyst review. The platform reportedly uses machine-learning-assisted text analysis, automated removal of system debris, database reverse engineering, ERP parsing, and human validation before material reaches buyers. That puts it closer to a managed criminal data-processing service than a simple leak repository.
The platform also appears to apply clear quality filters. Flare says Leak Bazaar prefers unpublished, mostly English-language corporate data from organizations with annual revenue above $10 million, and wants at least 100 GB of data, with a preference for 1 TB or more. That suggests the operators are targeting large, commercially useful breach datasets rather than random consumer dumps.
Transactions reportedly run through the Exploit guarantor service, and the platform advertises a 70/30 revenue split in favor of the data supplier. Flare says sellers can choose between an exclusive one-time sale or a multi-buyer model that allows the same processed dataset to be sold repeatedly. That gives criminals a stronger long-tail monetization model after a victim refuses to pay.
Why this is more dangerous than a normal leak dump
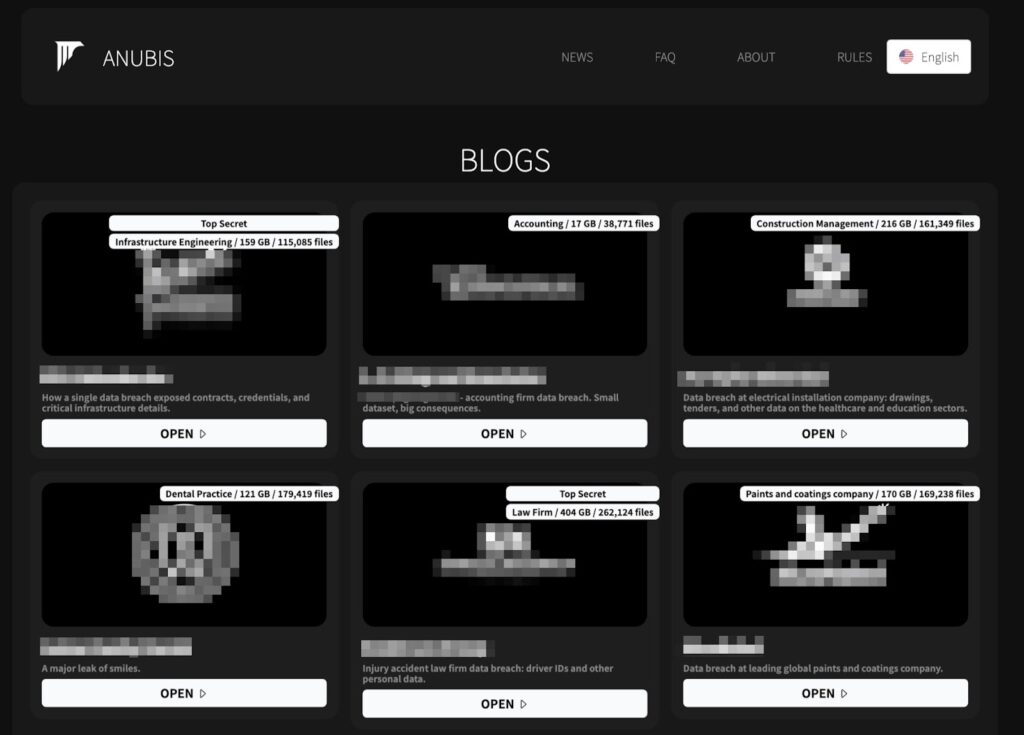
The biggest shift is not the theft itself. It is the packaging. Flare says Leak Bazaar breaks data into high-value categories such as quarterly financial reports, mergers and acquisitions documents, research and development files, and personal data records. That structure makes the marketplace more useful for different kinds of buyers, from fraud actors to competitors to financially motivated criminals.
That approach mirrors a broader pattern in cybercrime, where specialization keeps growing. Instead of one group handling the entire chain, different actors now focus on access, exfiltration, negotiation, resale, and downstream exploitation. Leak Bazaar appears to formalize the resale step by turning stolen archives into more refined criminal products. This is an inference based on Flare’s description of the service model and the way cybercrime marketplaces have matured in recent years.
For defenders, the warning is clear. A failed ransom negotiation no longer means the risk fades after a leak post goes live. If services like Leak Bazaar gain traction, stolen data may continue to generate criminal value long after the initial breach by being cleaned, segmented, and sold to multiple buyers over time.
Leak Bazaar at a glance
| Area | Reported details |
|---|---|
| Threat actor | Snow from SnowTeam |
| Forum used | TierOne (T1) cybercrime forum |
| Service type | Post-exfiltration processing and resale platform |
| Launch timing | Advertised March 25, 2026, with hidden service going live the same day |
| Preferred data | Unpublished, mainly English-language corporate data |
| Dataset size | Minimum 100 GB, prefers 1 TB or more |
| Claimed processing | ML-assisted analysis, debris removal, database reverse engineering, ERP parsing, human validation |
| Sales model | Exclusive sale or multi-buyer repeated sale |
| Revenue split | 70/30 in favor of the supplier |
| Payment discipline | Reportedly uses Exploit guarantor service |
What security teams should take from this
- Treat exfiltration as a long-term monetization risk, not a one-time leak event.
- Prioritize data classification so teams know which files, databases, and records would carry the highest resale value. This recommendation follows directly from the categories Flare says Leak Bazaar wants to sell.
- Expand dark web and threat intelligence monitoring beyond standard leak-site tracking, because processed resale markets may surface stolen data in different ways. This is an inference based on the platform’s stated business model.
- Build incident response plans that cover downstream resale, repeat exposure, and long-tail intelligence monitoring after an initial breach.
FAQ
Leak Bazaar is a newly reported criminal service that claims it can process raw stolen corporate data into organized, higher-value intelligence products for resale.
Flare published a March 25 report describing the platform, its advertisement by Snow from SnowTeam, and its operational model.
Instead of only publishing stolen files, Leak Bazaar says it cleans, parses, categorizes, and validates data before selling it.
Because stolen data may remain valuable for months or longer if criminals can repeatedly repackage and resell it to different buyers. This conclusion follows from Flare’s description of the platform’s multi-buyer model.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages