LeakNet scales ransomware attacks with ClickFix pages and a stealthy Deno loader

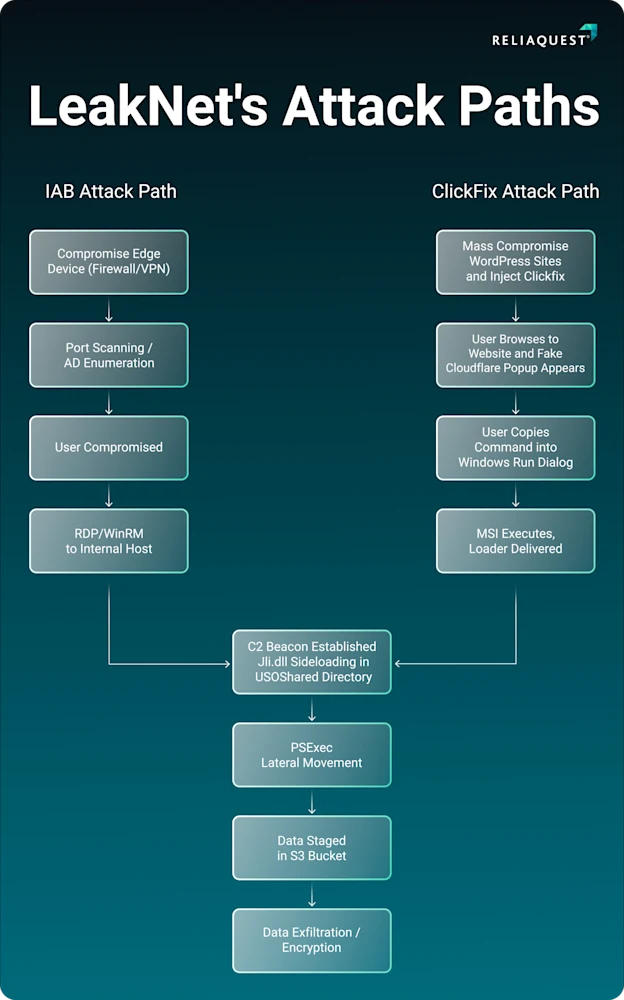
LeakNet is changing how it breaks into networks, and that shift matters. New research says the ransomware group now uses ClickFix lures on compromised websites and a memory-focused loader built on the legitimate Deno runtime, which gives it a broader victim pool and a stealthier path into Windows environments.
That combination marks a real escalation. Instead of leaning as heavily on stolen access from brokers, LeakNet can now trick users into launching the attack themselves through fake verification prompts, then move into a repeatable post-compromise chain that includes jli.dll sideloading, PsExec-based lateral movement, and payload staging through S3 buckets.
ReliaQuest says it has seen LeakNet average about three victims per month, but the group has started scaling up with these newer methods. The report ties the activity to LeakNet with high confidence based on shared infrastructure and recurring tactics, techniques, and procedures across incidents.
Why ClickFix gives LeakNet a wider reach
ClickFix is not new, but it remains effective because it targets people instead of software flaws. Microsoft says a typical ClickFix attack leads users from phishing emails, malicious ads, or compromised websites to a fake page that tells them to run a command, often by opening the Windows Run box or Terminal and pasting code themselves.
That matters for LeakNet because compromised legitimate sites look less suspicious than attacker-owned domains. In the cases ReliaQuest analyzed, users landed on pages that mimicked Cloudflare-style verification checks and were instructed to run an msiexec.exe command, which helped the attackers sidestep some of the signals that domain or reputation-based defenses usually catch first.

Microsoft has also warned that ClickFix can slip past conventional and automated protections because the victim performs the action directly. Once the user runs the command, attackers can download malware, loaders, or remote access tools and push the intrusion forward quickly.
The Deno loader is what makes this campaign harder to spot
LeakNet’s other major change sits deeper in the attack chain. ReliaQuest says the group deploys a previously unreported loader based on Deno, the open source JavaScript and TypeScript runtime, and uses it to execute a base64-encoded payload largely in memory.
That approach gives attackers a practical advantage. Deno itself is a legitimate developer tool, and the attackers bring the real runtime onto the victim’s system instead of dropping a custom binary that many tools would inspect more aggressively. According to ReliaQuest, the loader starts through PowerShell and VBScript files, fingerprints the machine, reaches out to attacker infrastructure for a second-stage payload, and continues fetching and running code in memory.
This kind of execution path fits a wider trend Microsoft has described in ClickFix campaigns. Threat actors increasingly lean on fileless or memory-loaded stages and living-off-the-land tools because those methods reduce obvious artifacts on disk and make traditional signature-based detection less reliable on their own.
What defenders should watch for
The good news is that LeakNet appears to follow a consistent playbook after it gets in. ReliaQuest says every confirmed incident it studied hit the same broad stages, which gives defenders clear opportunities to detect and contain the activity before encryption starts.
Security teams should pay close attention to suspicious msiexec use tied to fake verification prompts, unexpected installs or execution of Deno on endpoints that do not normally need it, jli.dll sideloading activity in C:\ProgramData\USOShared, unusual PsExec use, and outbound connections to recently registered domains or unfamiliar S3 buckets.
CISA’s ransomware guidance also supports that approach. The agency advises organizations to monitor for anomalous binaries, persistence, and lateral movement, and to isolate affected systems immediately once a compromise is confirmed to stop the spread.
LeakNet’s updated attack chain at a glance
| Stage | What LeakNet does | Why it matters |
|---|---|---|
| Initial access | Uses ClickFix lures on compromised legitimate sites | Broadens reach and lowers suspicion |
| User action | Tricks the victim into running a malicious command | Helps bypass some automated protections |
| Loader execution | Launches a Deno-based in-memory loader | Reduces disk artifacts and blends in with a legitimate runtime |
| Post-exploitation | Uses repeatable tools and movement patterns | Creates reliable detection points for defenders |
| Ransomware prep | Stages payloads and expands access | Speeds the path to encryption |
Key signs enterprises should prioritize
- Watch for fake verification or CAPTCHA pages that tell users to open Run and paste commands.
- Alert on unusual msiexec.exe, PowerShell, or VBScript activity launched from browser-driven workflows.
- Flag unexpected Deno installation or execution on endpoints outside developer teams.
- Restrict PsExec to approved administrators and review every unusual use case.
- Isolate compromised hosts quickly once lateral movement or payload staging begins.
FAQ
ReliaQuest says LeakNet has added ClickFix lures on compromised sites and a new Deno-based loader. That gives the group a larger funnel for initial access and a stealthier way to run code after the victim takes the bait.
It pushes the victim to run the malicious command themselves. Microsoft says that user-driven step can help the attack slip past protections that look for more automatic malware delivery patterns.
Because Deno is a legitimate runtime, its presence may not look suspicious by itself. LeakNet then uses it to decode and run payloads mostly in memory, which cuts down on the kind of files many tools inspect first.
Start with user awareness around fake verification prompts, tighter monitoring for suspicious command execution, stronger restrictions on PsExec, and immediate isolation of affected systems when post-exploitation activity appears.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages