Linux rootkits are getting stealthier with eBPF and io_uring tricks
Linux rootkits are evolving. Security researchers at Elastic Security Labs say modern Linux malware no longer relies only on classic loadable kernel modules or simple userland tricks. Newer rootkit designs increasingly abuse eBPF and io_uring, two legitimate Linux features that can give attackers stealth, flexibility, and less visible execution paths.
That shift matters because Linux now powers a huge share of cloud servers, containers, network appliances, and embedded systems. When attackers can hide inside kernel-level or kernel-adjacent features that administrators already trust, detection becomes much harder than it was with older rootkit techniques. Elastic says this newer tradecraft can reduce the usefulness of traditional tools that look mainly for classic kernel modules or obvious userland hooks.
What the new research says
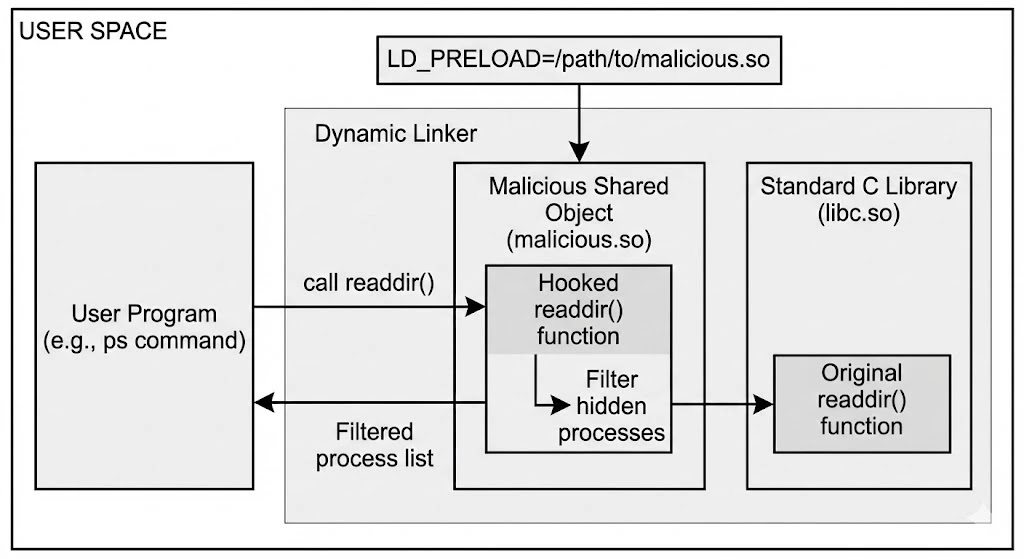
Elastic Security Labs published a two-part research series in early March 2026 on Linux rootkit taxonomy, hooking techniques, and tradecraft. In the first part, the researchers trace the progression from older shared object hijacking and loadable kernel module methods to newer approaches that use eBPF- and io_uring-powered techniques. Elastic specifically highlights examples such as TripleCross, Boopkit, and RingReaper as part of that broader evolution.
The core concern is not that eBPF or io_uring are malicious by design. They are not. Both features serve legitimate purposes inside Linux. The problem is that attackers can bend those features into stealth tools that hide activity from defenders who still expect rootkits to look like older kernel implants.
Why eBPF changes the rootkit playbook
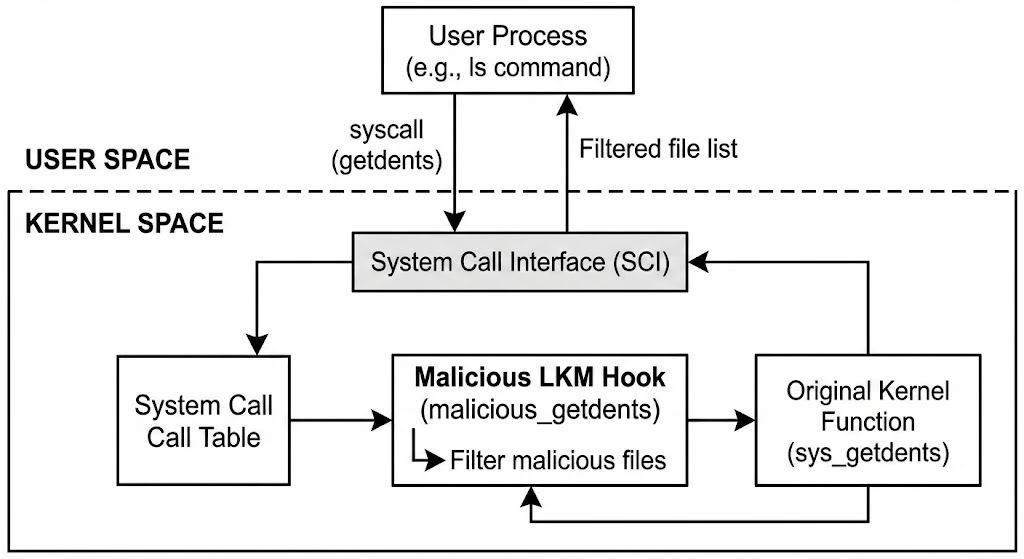
Elastic says eBPF rootkits can attach in-kernel bytecode to syscall tracepoints or Linux Security Module hooks. That gives attackers a way to observe or influence system behavior without loading a traditional out-of-tree kernel module. In practical terms, that can make the implant harder to spot on systems where defenders mainly check module lists or look for signs of classic kernel tampering.
Elastic also notes that this makes eBPF-based rootkits especially relevant in environments that use Secure Boot or module signing policies. Those controls can block older module-based rootkits, but they do not automatically solve the problem of malicious or unexpected eBPF programs already running inside the kernel context.
Why io_uring helps attackers stay quieter
io_uring is Linux’s high-performance asynchronous I/O interface. The Linux man pages describe it as a mechanism that lets software submit work through shared ring buffers and register resources like files and buffers to reduce overhead. That design improves performance for legitimate workloads, but it can also reduce the visibility that defenders get from ordinary syscall-heavy activity.
Elastic’s research says attackers can abuse io_uring to batch operations in ways that blur per-syscall telemetry. That matters because many detection tools still rely heavily on syscall patterns to understand what a process is doing. If malicious activity moves through a quieter I/O path, security monitoring can lose useful context.
Why older tools may miss this
Traditional Linux rootkit scanners were built for older threats. They often look for suspicious kernel modules, altered binaries, or userland hooks that fit patterns defenders have known for years. Elastic says eBPF implants do not show up like ordinary kernel modules, which means tools focused on /proc/modules or old module-loading behavior may miss them.
That does not mean defenders are helpless. It means the detection model needs to change. Instead of asking only whether a suspicious module exists, defenders need to ask whether unexpected eBPF programs are loaded, what they attach to, and whether processes are using io_uring in ways that do not match the system’s normal role. This is an inference drawn from Elastic’s detection guidance and the Linux interface behavior documented in the man pages.
At a glance
| Topic | Verified detail |
|---|---|
| Main research source | Elastic Security Labs published a two-part Linux rootkit series in March 2026 |
| Modern rootkit direction | Elastic highlights eBPF- and io_uring-powered techniques as part of current Linux rootkit tradecraft |
| eBPF role | eBPF programs can attach to syscall tracepoints or LSM hooks in the kernel |
| io_uring role | io_uring uses shared rings and registered resources to reduce per-I/O overhead |
| Detection challenge | eBPF implants may evade checks that focus on classic kernel modules |
What defenders should do
Elastic’s research points toward more targeted monitoring. Teams should audit loaded eBPF programs, especially on systems where eBPF tooling is not normally expected. They should also review what those programs attach to, since unexpected tracepoint or LSM attachments can signal compromise.
For io_uring, defenders should watch for unusual use of io_uring_enter and io_uring_register, especially from processes that have no obvious reason to use high-performance asynchronous I/O. The Linux man pages confirm these interfaces handle work submission and resource registration, which makes them useful observation points when trying to spot abnormal behavior.
Elastic also argues for stronger kernel integrity monitoring, memory forensics, and telemetry collected below normal userland visibility. In plain terms, if the malware aims to hide from ordinary operating system views, defenders need visibility that sits deeper than ordinary process and file listings.
Key points
- Elastic says Linux rootkits now increasingly use eBPF and io_uring techniques.
- eBPF can let attackers hook into kernel activity without a classic loadable kernel module.
- io_uring can reduce observable syscall patterns by batching work through ring-based interfaces.
- Older rootkit detection tools may miss implants that do not appear as normal kernel modules.
- Defenders need better monitoring of loaded eBPF programs and unusual io_uring usage.
FAQ
Elastic says newer rootkits increasingly move away from classic loadable kernel modules and toward eBPF- and io_uring-related techniques.
No. Both are legitimate Linux features. The risk comes from attackers abusing them for stealth and evasion.
Elastic says eBPF-based implants do not present like traditional out-of-tree kernel modules, so older checks may miss them.
Because it can reduce the amount of normal syscall-level visibility that some detection systems rely on.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages