Mail2Shell zero-click attack lets hackers hijack FreeScout mail servers

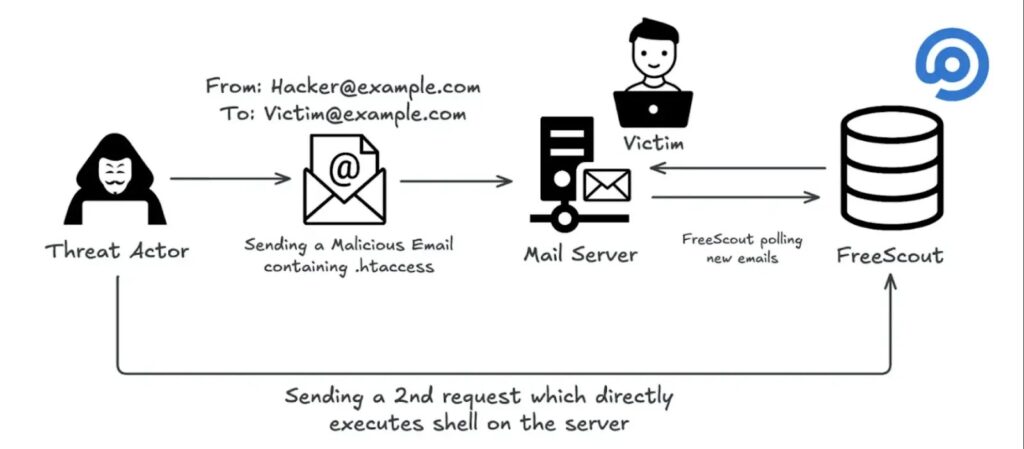
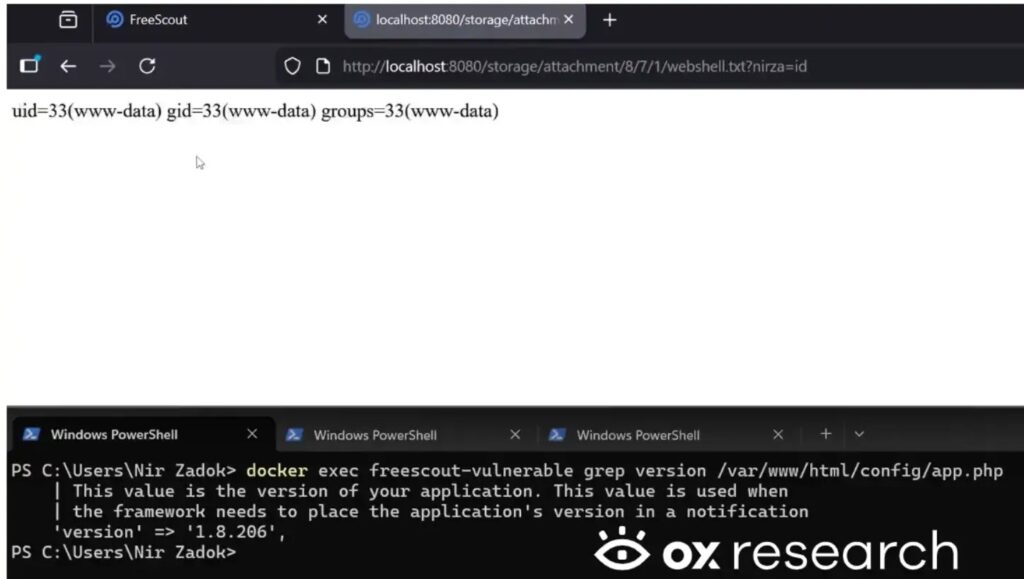
Security researchers have disclosed a critical FreeScout flaw that can let an attacker run commands on a FreeScout server by sending a single crafted email to a mailbox the server monitors. OX Security calls the technique Mail2Shell and says it turns a recently patched file-upload RCE into a zero-click, unauthenticated takeover path in real deployments.
FreeScout has already shipped a fix. The project’s security log lists CVE-2026-28289 as a patch bypass that affects versions earlier than 1.8.207, and FreeScout points users to update.
What happened
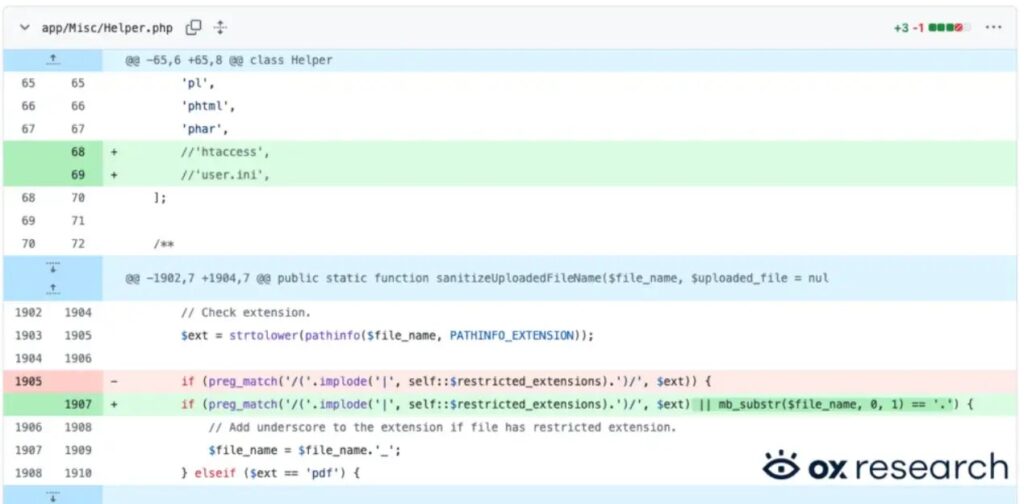
FreeScout recently fixed an Apache-related RCE issue tracked as CVE-2026-27636 (affected versions earlier than 1.8.206).
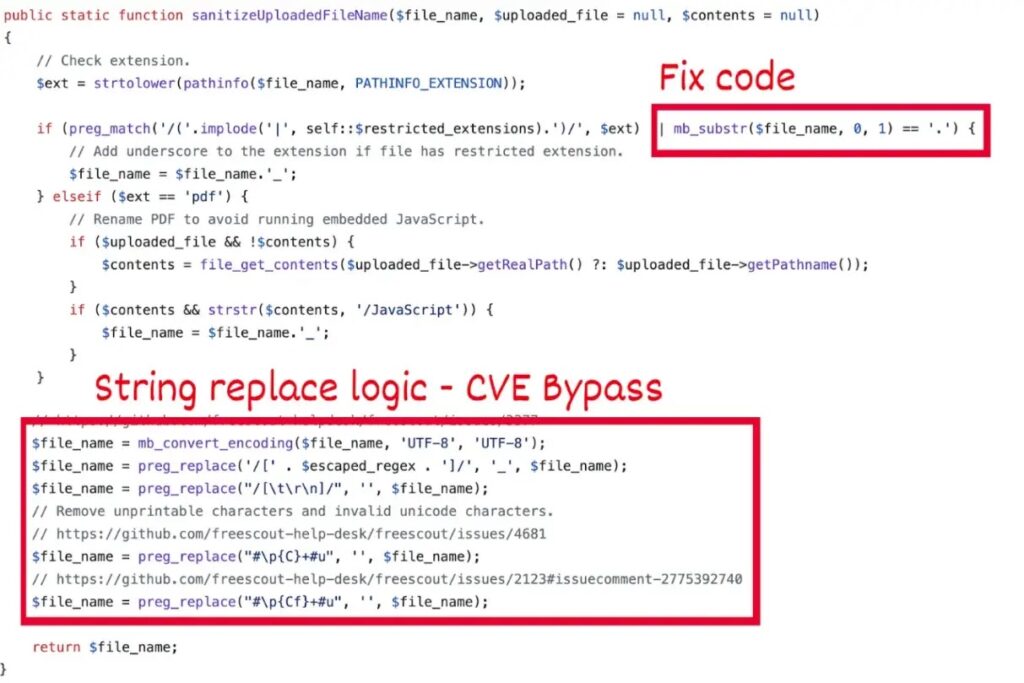
OX Security then reviewed the patch and found a filename-validation bypass that relies on a zero-width space character (Unicode U+200B) to slip a dangerous dotfile past the filter. OX says later processing strips the hidden character, and the server ends up saving the payload as a real dotfile.
OX then escalated the chain. It says FreeScout’s mail ingestion can write attacker-controlled attachments to disk, which lets the attacker reach the stored payload through the web path and trigger code execution.
Key details
| Item | Details |
|---|---|
| Name used by researchers | Mail2Shell |
| CVE | CVE-2026-28289 |
| Impact | Remote code execution |
| Attack input | Crafted email with malicious attachment names |
| Fixed version | FreeScout 1.8.207 |
| Related earlier issue | CVE-2026-27636 (earlier RCE) |
Why versions and descriptions look confusing
Public vulnerability records for CVE-2026-28289 describe an RCE path where an authenticated user with upload permissions can bypass checks using a zero-width space prefix.
OX Security’s report describes a broader real-world impact when FreeScout ingests email attachments automatically, which can remove the need for authentication or user interaction in certain deployments.
If you run FreeScout as a shared mailbox helpdesk with inbound email enabled, treat OX’s zero-click claim as the more relevant risk model and patch quickly.
Who is at risk
You face the highest risk if you meet all of these conditions:
- You run FreeScout < 1.8.207
- Your instance ingests inbound email and saves attachments to disk
- Your FreeScout server exposes web access to attackers through the internet or a reachable internal segment
What to do now
- Update FreeScout to 1.8.207 or later.
- Review your deployment for risky Apache settings. OX specifically recommends disabling AllowOverrideAll on the FreeScout host.
- Treat unexpected inbound attachments as hostile until you patch, especially archives and files that arrive with suspicious filenames.
Verification and quick checks
- Confirm your FreeScout version and upgrade if it is lower than 1.8.207.
- Search logs for unusual attachment filenames and repeated inbound emails to support addresses you publish publicly.
- Look for unexpected files under FreeScout’s attachment storage directories, then correlate with suspicious conversations created by mail ingestion.
FAQ
OX says the attacker can trigger code execution without authentication and without user interaction by sending a crafted email to a configured FreeScout address.
FreeScout lists CVE-2026-28289 as affecting versions earlier than 1.8.207.
Yes. FreeScout lists CVE-2026-28289 as a patch bypass for CVE-2026-27636.
Reduce exposure. Remove direct internet access to FreeScout, harden Apache configuration, and restrict inbound mail processing to trusted sources until you deploy the update.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages