Malicious npm packages disguised as Solara executor stole Discord data, browser secrets, and crypto wallets
Two malicious npm packages posed as tools related to the Solara Roblox executor and delivered a Windows-based infostealer that targeted Discord accounts, browser data, and cryptocurrency wallets, according to JFrog Security researchers. The packages, bluelite-bot-manager and test-logsmodule-v-zisko, have since been removed from npm.
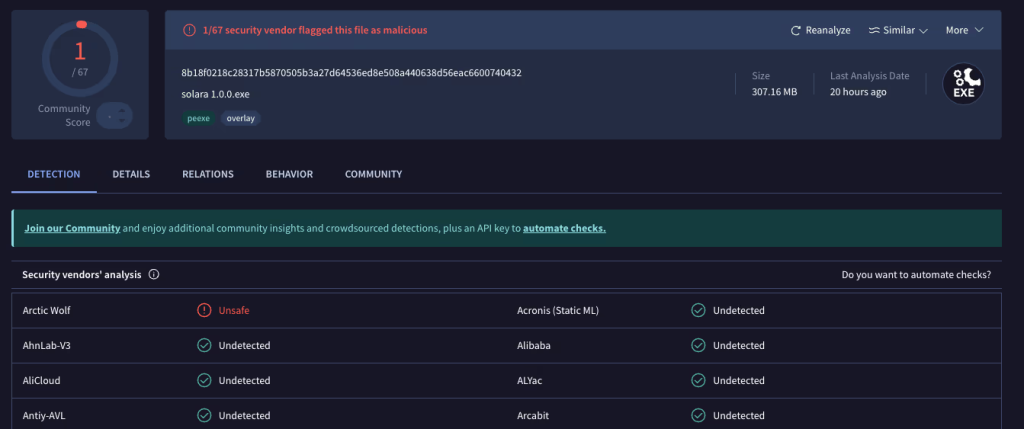
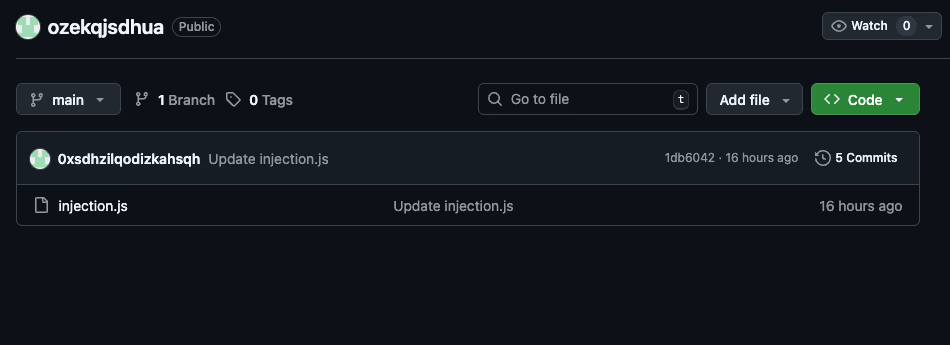
JFrog says both packages used a preinstall script to silently download and run a Windows executable named solara 1.0.0.exe or solara 1.0.1.exe from Dropbox. That executable acted as a dropper for what the malware called Cipher stealer, which bundled obfuscated JavaScript, a full Node.js runtime, an embedded Python script, and a second-stage payload fetched from GitHub.
The campaign stands out because it blended several theft techniques into one package chain. JFrog says the malware stole Discord tokens, browser passwords, cookies, browsing data, and files from cryptocurrency wallets, then compressed the stolen data and sent it to attacker-controlled infrastructure.
What the malicious npm packages did
According to JFrog, the two packages were built to execute automatically during installation on Windows systems. Instead of shipping obvious malware in plain view, they downloaded the solara executable from Dropbox, which then unpacked the next stages locally. JFrog said the dropper hid a 321 MB archive that contained all the runtime components needed to launch the stealer without much extra setup.
That design helped the malware evade basic static inspection. JFrog noted that the outer executable showed almost no antivirus detections at first because the malicious logic was buried deeper inside the package chain and runtime payloads.
Discord theft was a major focus
JFrog says Cipher stealer aggressively targeted Discord. It searched LevelDB databases used by Discord clients and Chromium-based browsers to steal stored session tokens, then validated them against Discord’s live API.
On systems with BetterDiscord installed, the malware reportedly patched core files to disable webhook protections. On the official Discord desktop client, JFrog says it pulled a secondary JavaScript payload from GitHub and injected it into the app, forcing users to log back in so the malware could capture email addresses, passwords, two-factor codes, and even payment card details entered during reauthentication.
JFrog also says the Discord modification could persist across reboots by changing startup-related files. That gave the attackers a way to keep harvesting data after the first compromise.
Browsers and wallets were also in scope
Browser theft happened on more than one layer. JFrog says the JavaScript component used Windows DPAPI-related methods to extract browser encryption keys from Local State files, then queried saved login databases to steal passwords from browsers such as Chrome, Brave, Edge, Opera, and Yandex.
The embedded Python component widened the reach further. JFrog says it targeted additional browsers, including Firefox, Vivaldi, CocCoc, and QQ Browser, and stole cookies, stored payment cards, autofill entries, bookmarks, and browsing history.
The malware also searched for cryptocurrency wallet directories tied to Bitcoin, Ethereum, Exodus, Electrum, Atomic Wallet, and others. JFrog says it copied wallet files into a staging folder and even attempted to decrypt the Exodus wallet seed file.
Known malicious packages
| Package name | Reported role |
|---|---|
| bluelite-bot-manager | Malicious npm package used to deliver Cipher stealer |
| test-logsmodule-v-zisko | Malicious npm package used to deliver Cipher stealer |
Source: JFrog Security Research.
Why this attack matters
This case shows how threat actors still use npm as a delivery channel for Windows malware, even when the final payload has little to do with normal JavaScript package use. The attacker did not need a complex exploit chain. A malicious install script was enough to pull down the Windows executable and begin the compromise. That conclusion follows directly from JFrog’s analysis of the preinstall behavior.
It also shows how developer and gaming-themed lures continue to overlap with credential theft and crypto theft. By branding the payload around Solara, the attackers tried to attract users already looking for Roblox executor tools, which often come from unofficial and risky sources. This is an inference based on the package disguise and payload naming described by JFrog.
What exposed users should do
- Remove the malicious packages from affected systems.
- Reinstall the Discord desktop client if it was present on the machine, because JFrog says the malware modified Discord files.
- Rotate passwords, session tokens, and any credentials stored in browsers. This is a practical response based on the reported theft of browser and Discord secrets.
- Review crypto wallets for unauthorized access or suspicious transfers.
- Check whether Python or other unexpected runtime components were silently installed during the infection window. This step follows from JFrog’s description of the malware chain.
FAQ
JFrog identified bluelite-bot-manager and test-logsmodule-v-zisko as the malicious packages in this campaign.
JFrog says the packages delivered a Windows executable that launched a payload called Cipher stealer.
According to JFrog, it targeted Discord credentials and tokens, browser passwords and cookies, browsing data, and cryptocurrency wallet files.
JFrog says both malicious packages were removed from npm.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages