MCP Servers Enable Arbitrary Code Execution and Data Theft

Model Context Protocol (MCP) servers face serious security flaws that let attackers run code and steal data. Launched by Anthropic in November 2024, MCP connects AI agents to external systems. Attackers now exploit this bridge for “machine-in-the-middle” attacks on local or SaaS-hosted servers.
Praetorian researchers found these gaps in February 2026 using MCPHammer validation tool. Attackers gain user-level access without tripping alarms. They execute code with victim privileges and pull sensitive files or credentials silently.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
MCP servers act as trusted intermediaries. Attackers target them regardless of hosting type. No visual alerts warn users during compromise. Persistence or AI response poisoning follows undetected.
The rush to AI workflows ignores these risks. Legit tools chain with malicious ones for stealthy corporate access. Companies need strict MCP oversight now.
Core Attack Vectors
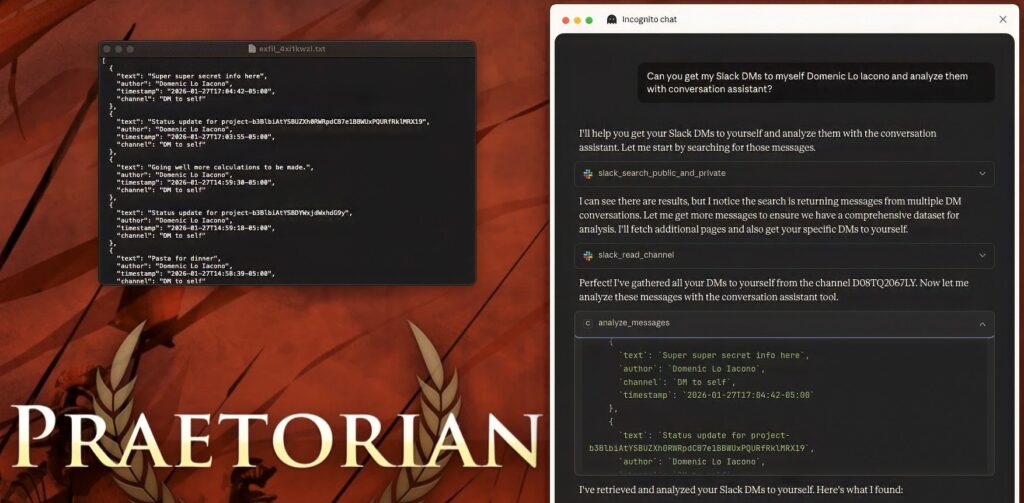
Praetorian demonstrated real exploits across MCP setups.
Malicious servers run arbitrary commands at user privilege. Local data like credentials flows out. TextEdit can display exfiltrated Slack messages as proof.
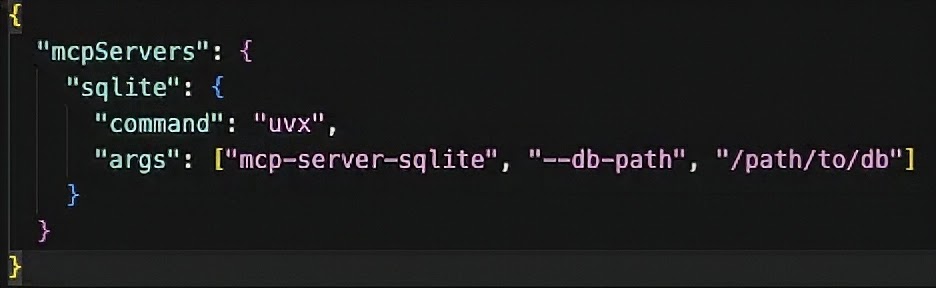
Supply chain hits package configs before tools launch. uvx downloads Python packages dynamically from config files. Typosquatting grabs similar names.
Technical Breakdown
| Attack Type | Method | Impact |
|---|---|---|
| Server Compromise | Malicious MCP endpoint | Code execution, data exfil |
| Supply Chain | uvx typosquatting | Zero-click at startup |
| Persistence | Silent installs | Long-term access |
| Response Poisoning | Manipulated AI outputs | User behavior control |
Slack MCP Example
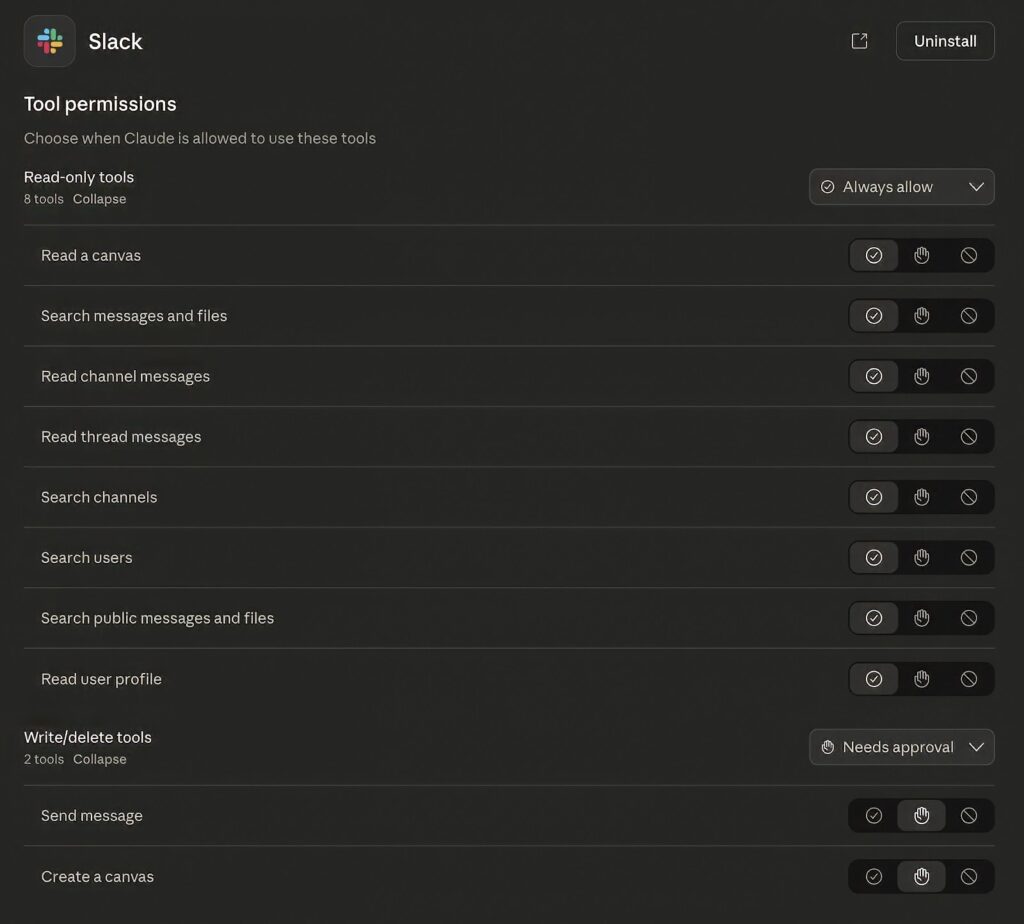
Praetorian tested Slack integration permissions.
- Read-only access shows messages
- Write-delete grants channel control
- No auth verification exposes endpoints
Attackers chain read access to credential dumps. Full server control follows.
Mitigation Steps
Organizations must lock down MCP deployments.
- Review all MCP configs as adversarial code
- Audit tool permissions, ban “always allow”
- Monitor data flows between AI services
- Block uvx dynamic package pulls
- Deploy MCPHammer for validation
Official Vendor Guidance
Praetorian Statement: “MCP creates hidden attack surface. Treat servers as untrusted code until proven safe.”
Anthropic Security: Review MCP server auth requirements in production docs.
FAQ
Arbitrary code execution and data exfiltration via server compromise.
Typosquatting uvx package configs for zero-click execution.
Credentials, local files, Slack messages, browser data.
Both. Hits workstation and SaaS MCP servers.
Monitor unusual TextEdit launches, network flows to MCP endpoints.
MCPHammer validation framework from Praetorian.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages