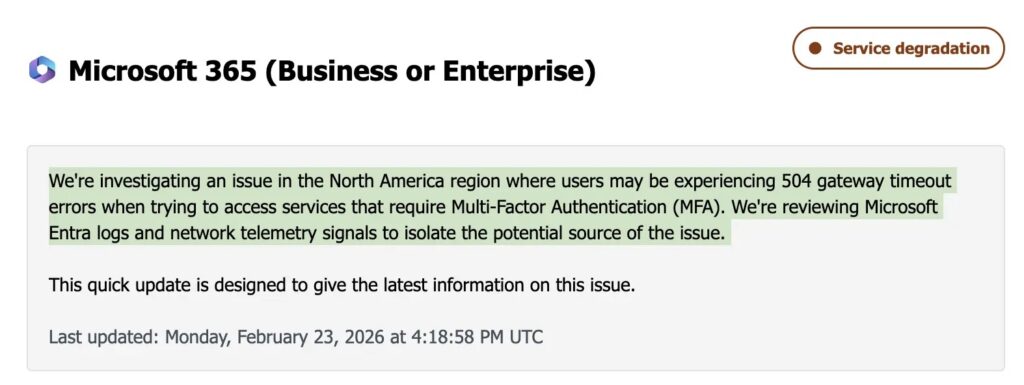
Microsoft MFA Outage Blocks U.S. Users with 504 Gateway Timeouts (MO1237461)

Microsoft 365 Multi-Factor Authentication failed for North American users starting February 23, 2026, at 8:22 PM IST. Widespread 504 Gateway Timeout errors block MFA verification across enterprise services. The incident carries ID MO1237461 with no estimated resolution time.
Users see timeouts when completing MFA challenges. Exchange Online, Teams, SharePoint, and Entra ID integrations fail completely. Conditional Access policies enforcing MFA lock out compliant devices and VPN connections. Third-party apps using federated authentication face identical disruptions.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Microsoft classifies this as service degradation, not full outage. Intermittent success occurs via request routing luck. Affected users experience total lockout from productivity tools. North America bears primary impact though global routing may hit others.
Latest update at 9:27 PM IST confirms Entra log analysis and network telemetry review. Engineering pushed status at 8:23 PM and 8:56 PM IST. No root cause identified. Public status page shows green while tenant dashboards reveal true scope.
504 errors signal upstream authentication servers failing response windows. Gateway layers timeout blocking user flows. Entra ID (formerly Azure AD) likely hosts the core issue in gateways, load balancers, or backend processors.
Enterprises face critical dilemmas. Disabling MFA risks total compromise. Maintaining policies kills business continuity. VPN drops sever remote workers completely.
Affected Services Table
| Service | Impact Level | Dependencies |
|---|---|---|
| Microsoft 365 Suite | Total lockout | MFA verification |
| Exchange Online | Email blocked | Entra ID auth |
| Microsoft Teams | Collaboration down | Conditional Access |
| SharePoint Online | Document access | MFA prompts |
| VPN/Remote Access | Device compliance | Policy enforcement |
| Third-party SSO | Federated failure | Entra ID integration |
Corporate environments run on MFA-gated access. Outage timing hits Monday workflows hardest. Finance approvals, customer support, and executive communications stall instantly.
Admin Workarounds
- Check Microsoft 365 admin center for MO1237461 updates every 15 minutes
- Test alternate networks, browsers, or incognito mode for intermittent routing
- Review Conditional Access policy exceptions carefully (high risk)
- Open priority Microsoft Support tickets for mission-critical systems
- Document outage impact for SLA claims post-resolution
- Prepare user communications explaining troubleshooting steps
Public status.cloud.microsoft shows operational. Tenant-specific health dashboard holds true details. @MSFT365Status posts real-time X updates.
Organizations maintain MFA during outages. Temporary disablement creates larger incidents than access delays. Business impact assessments guide policy decisions.
Telco carriers report VPN drops across enterprise clients. Global firms reroute US staff to EU endpoints where possible. Intermittent success varies by geographic routing.
Business Continuity Steps
- Activate offline approval workflows immediately
- Shift critical comms to phone/SMS temporarily
- Deploy secondary authentication for emergency access
- Pre-stage Conditional Access exceptions for verified safe accounts
- Test failover identity providers if multi-SSO configured
Microsoft engineering engages actively. Three updates signal progress toward isolation. Entra infrastructure telemetry narrows scope methodically.
FAQ
Upstream Entra ID servers timeout. Gateways return 504 when auth backend fails response window.
North America primary. US enterprises hit hardest by routing patterns.
Possible via policy exceptions. High security risk not recommended for production.
Microsoft 365 admin center incident MO1237461 or @MSFT365Status on X.
Teams, Exchange, SharePoint, VPNs enforcing MFA/Conditional Access policies.
February 23, 2026, 8:22 PM IST (2:52 PM UTC). Three status updates issued.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages