Microsoft says Storm-2755 is hijacking paychecks in payroll pirate attacks on Canadian workers

Microsoft says a financially motivated threat actor it tracks as Storm-2755 has been targeting Canadian employees in payroll redirection attacks designed to divert salary payments into attacker-controlled accounts. The company says the campaign relies on adversary-in-the-middle phishing to hijack authenticated Microsoft 365 sessions, not just steal passwords.
That distinction matters because the attackers can bypass older forms of MFA by replaying stolen session cookies and OAuth tokens after a victim signs in. Microsoft says the campaign uses SEO poisoning and malvertising to place a fake Microsoft 365 login page in front of Canadian users searching for terms like “Office 365” or even misspellings such as “Office 265.”

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The end goal is simple and highly profitable. Once inside an account, Storm-2755 looks for payroll and HR processes, hides related email replies from the victim, and either tricks HR into changing direct deposit details or logs into payroll platforms such as Workday to change the banking information directly.
How the attack starts
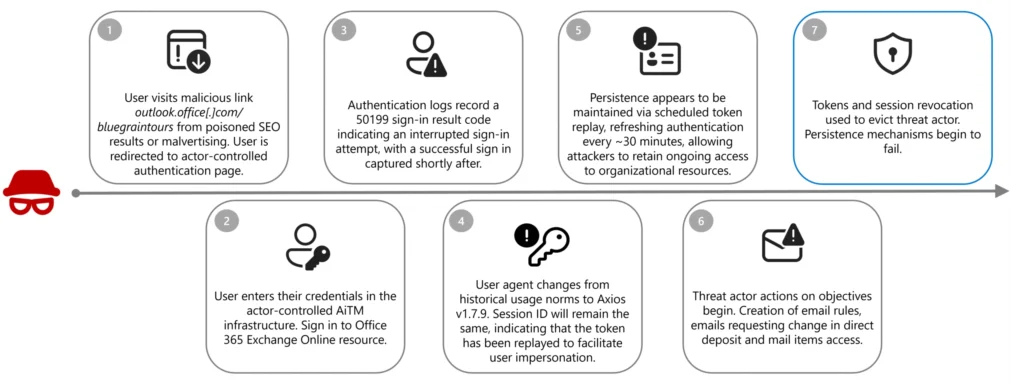
Microsoft says the campaign begins when a victim clicks a malicious search result or ad that leads to an actor-controlled phishing domain, including one example the company shared, bluegraintours[.]com. The fake page imitates the Microsoft 365 sign-in flow and captures the user’s session during authentication.
The company says one sign of compromise appears in sign-in logs as a 50199 sign-in interrupt error immediately before the attacker takes over the session. Microsoft also says the user-agent often changes to Axios, commonly version 1.7.9, while the session ID remains the same, which strongly suggests token replay rather than a fresh login.
Microsoft describes this as an AiTM attack, where malicious infrastructure sits between the victim and the real authentication service, captures session cookies and access tokens in real time, and then reuses them to access Microsoft services without another MFA prompt.
What Storm-2755 does after account takeover
Once the attackers gain access, Microsoft says they establish persistence by replaying the stolen tokens about every 30 minutes through non-interactive sign-ins to OfficeHome. The company says those sessions typically stay active until remediation revokes them, and in some cases they can remain usable for about 30 days if the attackers keep them alive.
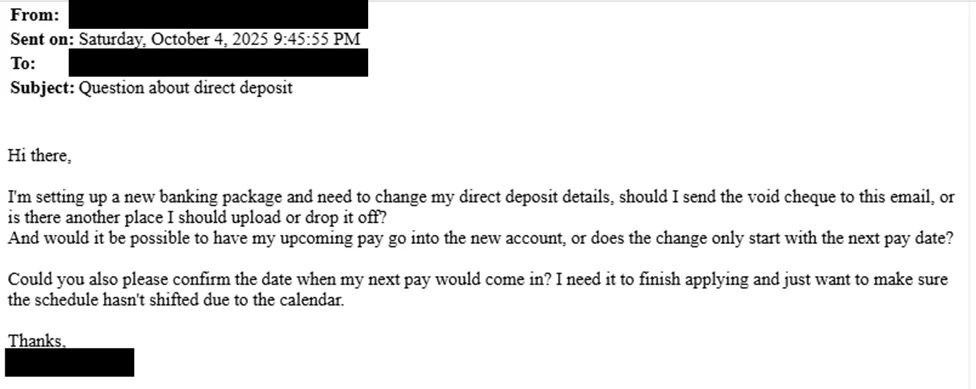
From there, Storm-2755 searches for payroll-related terms such as “payroll,” “HR,” “direct deposit,” and “finance.” Microsoft says the actor often emails HR staff from the compromised account using the subject line “Question about direct deposit” to push through fraudulent changes with minimal hands-on activity.
The actor also uses a quiet but effective defense-evasion step. Microsoft says Storm-2755 creates inbox rules that move messages containing “direct deposit” or “bank” into hidden folders and stop further rule processing, which prevents victims from seeing replies from HR about the fraudulent request.
Why this campaign stands out
Microsoft says this campaign differs from earlier payroll pirate operations because it does not focus on one industry or one employer. Instead, Storm-2755 appears to target Canadian users broadly through geographically focused search poisoning and malvertising.
That broad targeting makes the threat harder to dismiss as a niche HR scam. Any Canadian employee who uses Microsoft 365 and can influence or access payroll-related workflows could become a target, especially if their organization still relies on non-phishing-resistant MFA. This assessment is an inference based on Microsoft’s description of the victim profile and targeting method.
Microsoft also connects this campaign to a wider trend. The company previously documented Storm-2657 targeting US university employees in payroll pirate attacks, which suggests threat actors increasingly see salary redirection as a repeatable business model rather than a one-off scam.
Storm-2755 payroll pirate attack at a glance
| Item | Confirmed detail |
|---|---|
| Threat actor | Storm-2755 |
| Main target | Canadian employees |
| Initial lure | SEO poisoning and malvertising for Microsoft 365 login searches |
| Phishing method | Adversary-in-the-middle session hijacking |
| MFA bypass | Reuse of stolen session cookies and OAuth tokens |
| Follow-on action | Emails to HR or direct payroll changes in platforms like Workday |
| Evasion tactic | Hidden inbox rules for “direct deposit” and “bank” messages |
Source: Microsoft Incident Response.
What defenders should do now
- Deploy phishing-resistant MFA, such as FIDO2 or passkeys, because Microsoft says legacy MFA can be bypassed by token replay in AiTM attacks.
- Block legacy authentication protocols and tighten conditional access policies around risky sign-ins and new session behavior.
- Revoke compromised tokens and active sessions immediately if you detect suspicious sign-ins or payroll-related inbox rules.
- Review HR and payroll workflows for out-of-band verification before any direct deposit change, especially when the request arrives by email. This is a practical inference from the social-engineering method Microsoft documented.
FAQ
It is a form of payroll redirection fraud in which attackers hijack an employee account and change direct deposit details so salary payments go to an attacker-controlled bank account. Microsoft says Storm-2755 used this method against Canadian employees.
Microsoft says the actor captures authenticated session cookies and OAuth access tokens through an AiTM phishing flow, then replays them instead of trying to log in again with stolen credentials alone.
Microsoft says the attackers create rules that hide messages containing terms like “direct deposit” or “bank,” which helps them keep the victim unaware while they communicate with HR or payroll staff.
Yes. Microsoft says Storm-2755 sometimes pivoted to direct interaction with HR SaaS platforms such as Workday when social engineering alone did not succeed.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages