MIMICRAT RAT Delivered Through Sophisticated ClickFix Campaign Targets Global Enterprises

Elastic Security Labs uncovered MIMICRAT, a custom C++ remote access trojan spreading via “ClickFix” attacks on compromised legitimate websites. Malicious JavaScript injects fake Cloudflare verification pop-ups tricking users into running PowerShell commands. Five-stage infection chain disables defenses and deploys fully fileless implant in memory.
Attackers compromise trusted financial and productivity sites silently. Visiting users see browser error overlays demanding command-line fixes. Social engineering bypasses all download protections completely. Campaign localizes lures into 17 languages hitting multiple industries worldwide.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
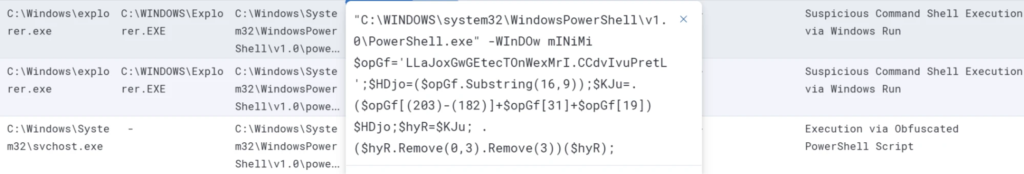
Initial PowerShell payload downloads obfuscated second-stage script. This disables Windows Event Tracing and Antimalware Scan Interface (AMSI) instantly. Security tools go blind allowing clean execution of later stages.
Lua-based loader decrypts shellcode entirely in RAM. MIMICRAT gains persistence with Windows token theft, file manipulation, and SOCKS5 tunneling capabilities. Command-and-control blends with web analytics via malleable HTTP profiles.
Native C++ construction ensures long-term stealth. Modular design enables rapid tactic adaptation. Network defenders struggle against legitimate-looking traffic patterns.

ClickFix Infection Chain
Stage 1: Malicious JS on legit site → fake Cloudflare popup
Stage 2: PowerShell disables ETW/AMSI → downloads stager
Stage 3: Lua loader decrypts shellcode in memory
Stage 4: MIMICRAT persistence + capability modules
Stage 5: C2 via malleable HTTP profiles
Compromised sites include bincheck.io loading jq.php from investonline.in. Attackers favor high-trust domains for maximum click-through rates.
MIMICRAT Capabilities Table
| Feature | Function | Evasion Method |
|---|---|---|
| Token Theft | Privilege escalation | In-memory execution |
| File Operations | Exfiltration/persistence | RAM-only storage |
| SOCKS5 Proxy | Lateral movement | Legit traffic mimicry |
| AMSI Bypass | Defender evasion | Early-stage disable |
| ETW Disable | Log evasion | Event tracing kill |
Fileless nature defeats traditional forensics completely. Custom Lua loader obscures execution flow further. Five-stage complexity overwhelms signature-based detection.
Technical Execution Details
PowerShell obfuscation spans multiple layers making static analysis useless.
AMSI bypass patches scanning interface before payload execution.
ETW disablement kills logging at kernel level preventing behavioral alerts.
Lua loader decrypts position-independent shellcode directly to memory.
Malleable C2 mimics Google Analytics, Cloudflare, and ad networks perfectly.
Enterprises face persistent threats post-infection. Token theft grants domain admin access silently. SOCKS5 tunnels enable unrestricted lateral movement across networks.
Defense Recommendations
- Train users to ignore browser verification popups demanding commands
- Enforce Constrained Language Mode for PowerShell enterprise-wide
- Deploy AMSI/ETW behavioral monitoring with memory scanning
- Block known ClickFix domains: investonline.in and jq.php endpoints
- Hunt Lua loaders and memory shellcode via EDR memory scanning
- Implement network traffic baselining for analytics profile anomalies
Global campaign scale demands proactive hunting. 17-language localization shows enterprise focus. Financial sector hits confirm high-value targeting.
Security teams report detection gaps against fileless C++ implants. MIMICRAT represents next-generation ClickFix evolution. Traditional AV signatures fail completely against memory-resident threats.
FAQ
Fake browser error popups on legit sites tricking users into running PowerShell “fixes.”
Fileless memory execution + ETW/AMSI bypass + malleable C2 profiles mimicking analytics.
Compromised legitimate domains like bincheck.io loading from investonline.in.
Token theft, SOCKS5 proxy, file ops, full Windows persistence.
Five: JS injection → PowerShell → AMSI bypass → Lua loader → memory shellcode.
Elastic Security Labs full report linked above.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages