MioLab macOS stealer adds ClickFix delivery, wallet theft, and team API tools

MioLab, also tracked as Nova, has grown into a more capable macOS-focused stealer service that now combines ClickFix-style social engineering, browser and wallet theft, and team features for criminal operators. New research from LevelBlue says the malware targets both Intel and Apple Silicon Macs, steals a wide range of user data, and now includes tools that let affiliates generate payloads and pull stolen logs through a team-oriented API.
The latest update matters because it shows how macOS malware keeps getting more organized. MioLab is not just a basic infostealer anymore. LevelBlue describes it as a malware-as-a-service platform with a lightweight payload, a web panel, optional premium modules, and infrastructure built for scale. The uploaded draft also points to the same shift, describing MioLab as a fast-evolving macOS MaaS operation with ClickFix delivery, wallet theft, and team tooling.

What MioLab can steal
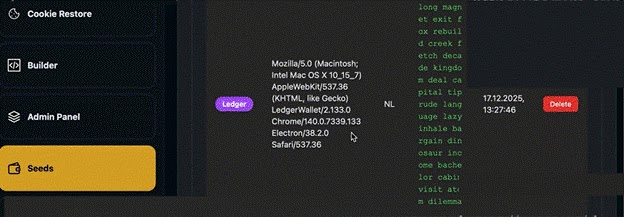
LevelBlue says MioLab can collect browser credentials, cookies, cryptocurrency wallet data, password-manager information, Apple Notes content, Telegram session data, and files from common user folders. The report also says a premium add-on targets Ledger and Trezor hardware wallets and can steal 24-word BIP39 recovery phrases, which raises the risk from ordinary credential theft to direct wallet compromise.
That is one of the clearest warning signs in this campaign. A Mac stealer that goes after both browser data and wallet recovery material can hit developers, executives, and crypto users in the same infection chain. The pasted draft highlights this broader theft set too, including Apple Notes decryption, Safari cookie theft, and hardware wallet extraction.
ClickFix pushes the infection into Terminal
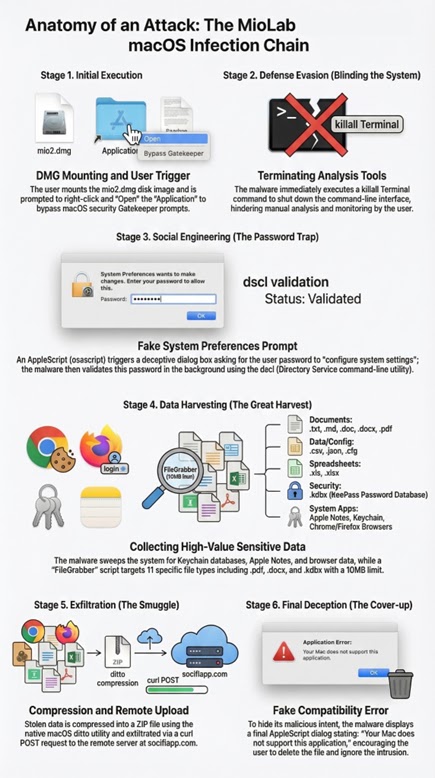
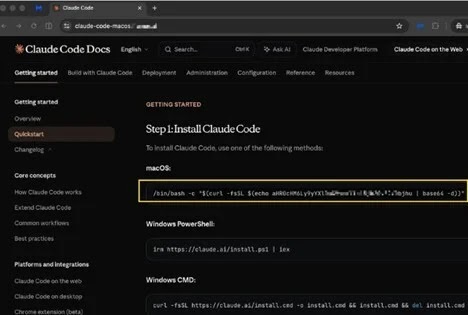
One of the newest additions is a ClickFix-style delivery chain aimed at macOS users who are comfortable with the command line. LevelBlue says operators can generate a ready-to-use Terminal payload from the panel, then deploy it through fake CAPTCHA pages or cloned software and documentation sites. In one live campaign, researchers observed a clone of the Claude Code documentation site that served legitimate-looking content to Windows visitors but delivered a malicious Terminal workflow to macOS users.
According to LevelBlue, that macOS chain used a Base64-masked URL that launched a curl-based loader, fetched a Mach-O payload into /tmp, and then ran xattr -c to remove Apple’s quarantine flag before execution. After that, the malware closed Terminal windows and displayed a fake password prompt through AppleScript, then used dscl to validate the captured local password. The uploaded draft describes the same sequence and helps confirm the chain structure you wanted covered.
Team API and Telegram support show a more mature operation
LevelBlue says MioLab’s operators have added a full Team API that lets criminal teams programmatically generate payloads and download stolen logs without using the regular admin panel. The platform also supports Telegram bot binding for real-time victim notifications. Those features make the service more attractive to organized affiliate groups because they reduce friction and speed up operations.
That operational polish stands out. A lot of macOS stealers focus only on data theft. MioLab appears to focus on workflow too, which suggests the operators want broader criminal adoption and repeat use rather than one-off infections.
Infrastructure and delivery trends
LevelBlue says MioLab’s admin infrastructure has rotated over time and links part of the ecosystem to broader fraud activity. The report says an older panel host later shifted to an Ethereum token airdrop phishing campaign, which points to an operator or hosting environment that supports multiple abuse operations. The same research also links the infrastructure to a bulletproof hosting provider operating under the Defhost brand.
That does not prove every related campaign shares a single operator, but it does show how modern stealer operations often sit inside a larger crime-support ecosystem instead of standing alone.

Quick facts
| Item | Details |
|---|---|
| Malware name | MioLab, also tracked as Nova |
| Target | macOS on Intel and Apple Silicon |
| Delivery | Fake sites, ClickFix-style Terminal commands, malicious loaders |
| Key theft targets | Browser data, password managers, Apple Notes, Telegram, crypto wallets |
| Premium theft module | Ledger and Trezor recovery phrase theft |
| Operator tooling | Web panel, Team API, Telegram bot binding |
Source: LevelBlue SpiderLabs research.
What defenders should do
- Train users to distrust Terminal commands copied from pop-ups, fake verification pages, and cloned documentation sites.
- Watch for suspicious use of curl, xattr, osascript, dscl, and system_profiler, especially when unsigned apps or newly downloaded files trigger them.
- Audit access to browser profile folders, wallet data, Apple Notes stores, and login.keychain-db on managed Macs.
- Block known malicious domains and inspect unusual curl POST traffic to external infrastructure. The uploaded draft specifically mentions socifiapp[.]com as one domain defenders should block.
- Treat fake software documentation and developer-tool landing pages as a growing malware delivery risk on macOS, not just Windows.
FAQ
It is a macOS-focused infostealer service, also tracked as Nova, that steals credentials, wallet data, notes, and other files while giving operators a web panel and team-oriented tooling.
Because it tricks users into running malicious Terminal commands themselves. That sidesteps some of the suspicion users might show toward a normal app installer.
Yes. LevelBlue says it targets software wallets and includes a premium hardware wallet module for Ledger and Trezor seed-phrase theft.
The combination of lightweight payloads, Team API access, Telegram notifications, fake documentation delivery, and specialized wallet theft makes it a more mature MaaS platform than a simple grab-and-go stealer.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages