MSHTML Zero-Day CVE-2026-21513: APT28 Exploitation Before February 2026 Patch
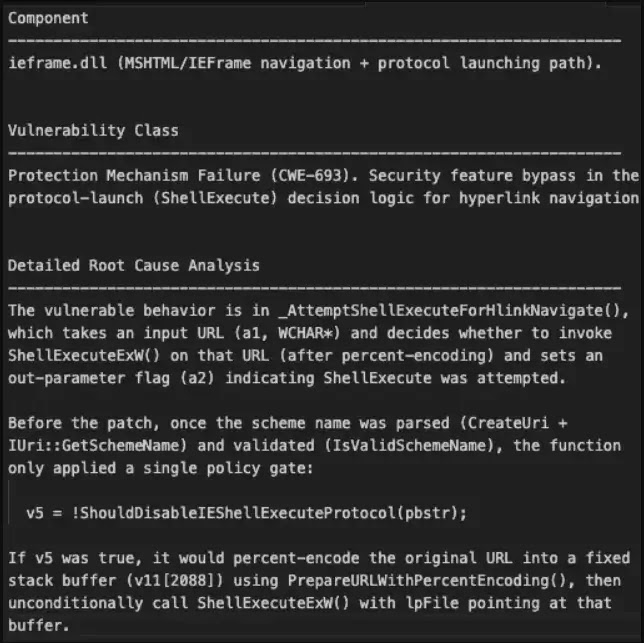
APT28 hackers exploited a zero-day flaw in Microsoft’s MSHTML framework before the February 2026 Patch Tuesday fix. Tracked as CVE-2026-21513, this vulnerability carries a CVSS score of 8.8. It allows security bypass and arbitrary code execution on all Windows versions through ieframe.dll.
Akamai researchers spotted the attacks in the wild. They linked the exploits to APT28, a Russian state-sponsored group. The team used PatchDiff-AI to analyze the root cause in the _AttemptShellExecuteForHlinkNavigate function.
Attackers tricked the system with poor URL validation. This let attacker input hit ShellExecuteExW paths. Local or remote files then ran outside browser protections.
Akamai Report: “We analyzed the MSHTML exploit chain used by APT28. Patch immediately.”
Vulnerability Details
| Feature | Details |
|---|---|
| CVE ID | CVE-2026-21513 |
| CVSS Score | 8.8 (High) |
| Affected File | ieframe.dll |
| Impact | Security bypass, code execution |
| Patch Released | February 2026 Patch Tuesday |
The flaw hit hyperlink handling hard. Nested iframes and DOM tricks broke trust zones. This dodged Mark of the Web and IE Enhanced Security.
A VirusTotal sample from January 30, 2026, showed the tactic. Named document.doc.LnK.download, it used a crafted .LNK with embedded HTML. It called out to wellnesscaremed[.]com, tied to APT28 campaigns.
Attack Flow
- User opens malicious .LNK file.
- Embedded HTML triggers MSHTML navigation.
- Bad URL validation invokes ShellExecuteExW.
- Payload runs with elevated rights.
Microsoft patched it by tightening protocol checks. Now file://, http://, and https:// stay in browser context. No more direct shell jumps.

Indicators of Compromise
- Hash: aefd15e3c395edd16ede7685c6e97ca0350a702ee7c8585274b457166e86b1fa
- Domain: wellnesscaremed[.]com
- MITRE Tactics: T1204.001 (LNK), T1566.001 (Phishing)
Apply patches now if not done. Watch for other MSHTML embeds beyond .LNK files.
FAQ
A high-severity MSHTML flaw for code execution via bad URL checks.
APT28, per Akamai threat intel.
Install February 2026 Windows security updates.
Yes, any MSHTML-hosting component.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages