New ACRStealer variant uses syscall evasion, TLS C2, and flexible payload switching

A newly documented ACRStealer variant shows a clear jump in stealth and flexibility. Security researchers say the malware now relies on low-level Windows syscalls to avoid common user-mode monitoring, uses TLS for encrypted command-and-control traffic, and can work within a delivery chain that swaps final payloads without rebuilding the full infection flow. Those changes make detection harder and incident response more complex.
The latest findings come from G DATA, which analyzed samples delivered through HijackLoader and tied to the long-running PiviGames lure infrastructure. According to the researchers, ACRStealer arrives as the final payload after victims are pushed through malicious links and redirected to archives that pose as legitimate installers. G DATA said the same infrastructure has also delivered LummaStealer, which suggests the operators can rotate payloads while keeping the rest of the distribution chain intact.
Proofpoint had already linked Amatera Stealer to ACRStealer in 2025, describing it as a rebranded and actively maintained information stealer sold as malware-as-a-service. That earlier research highlighted improved evasion and the use of NTSockets and direct WoW64 syscalls. G DATA’s newer report builds on that picture and shows the malware’s continued development.
What changed in this ACRStealer variant
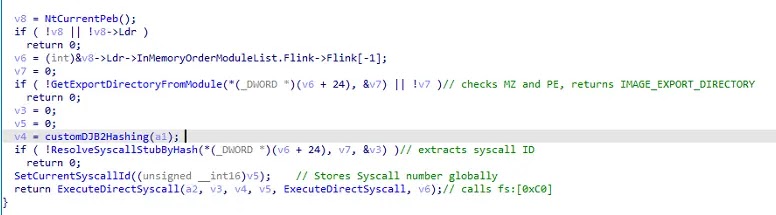
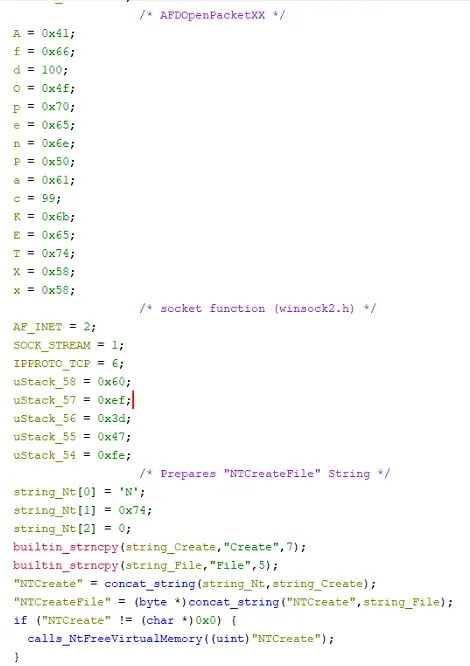
G DATA says this version resolves functions by locating ntdll.dll through the Process Environment Block and parsing the Export Address Table, rather than leaning on the higher-level Win32 APIs that many security tools watch more closely. The malware then executes syscalls through the WoW64 transition gate, a method that can bypass user-mode hooks used by EDR products.
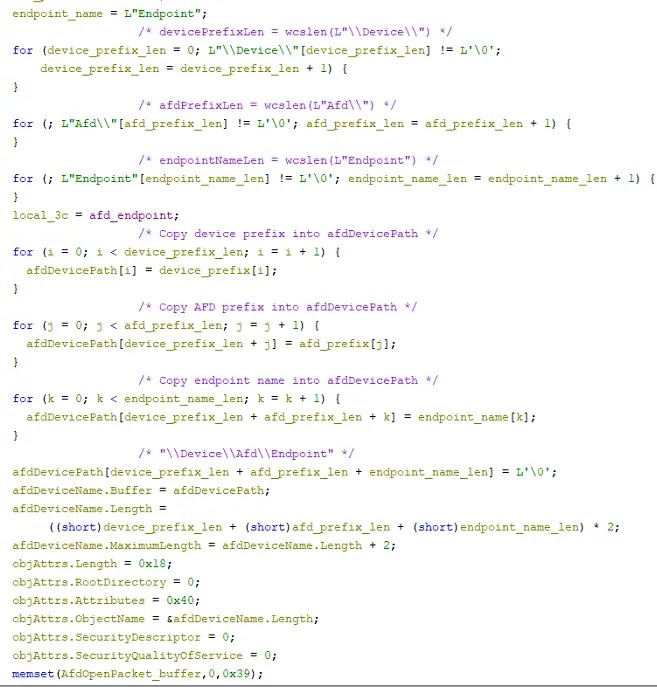
For network activity, the malware avoids standard Winsock APIs and instead builds an AFD endpoint path and opens it with NtCreateFile. After connecting, it completes a TLS handshake through Microsoft’s SSPI framework. G DATA said this variant used playtogga[.]com in the HTTP Host header and communicated with 157[.]180[.]40[.]106, which helped the traffic blend in with normal encrypted web sessions.
The stealer also broadens its data theft profile. Researchers said it targets browser credentials, cookies, login data, and Steam-related information, then writes stolen data to a hardcoded text file before exfiltration. The report also describes system fingerprinting that collects details such as machine GUID, username, architecture, locale, and build time.
Why defenders should pay attention
This is not just another browser credential stealer. The technical changes show an effort to reduce visibility at both the endpoint and network level. By mixing direct syscalls, AFD-based socket creation, and TLS-wrapped traffic, the malware removes several of the easier signals defenders often use for detection.
The delivery model matters too. G DATA said the PiviGames infection chain remained active into early 2026 and had started serving LummaStealer through a Mega-hosted Setup.exe in some cases. That means defenders cannot focus only on one payload family. They need to watch the loader, redirection chain, and infrastructure behind it.
Key technical details at a glance
| Area | Reported behavior |
|---|---|
| Initial delivery | HijackLoader through malicious PiviGames-themed distribution |
| Evasion | Direct WoW64 syscalls, dynamic API resolution via ntdll.dll |
| Network method | AFD endpoint creation with NtCreateFile instead of Winsock |
| C2 protection | TLS handshake via Microsoft SSPI |
| Theft targets | Browser data, cookies, login data, Steam credentials, system details |
| Infrastructure flexibility | Same chain also observed delivering LummaStealer |
Indicators and defensive steps
- Monitor for unusual use of low-level APIs such as
NtCreateFile,NtOpenFile, andNtQueryDirectoryFile. - Hunt for suspicious AFD-based socket activity that bypasses normal Winsock telemetry.
- Block or investigate traffic involving
157[.]180[.]40[.]106andplaytogga[.]comwhere appropriate. - Watch for HijackLoader behavior and staged malware delivered through gaming forums, social platforms, and fake software links.
- Educate users not to open installers from unverified links shared through Discord, Reddit, Steam communities, or file-sharing redirects.
FAQ
Researchers say it adds direct syscall-based evasion, TLS-protected C2 traffic, and continued use in flexible loader-based campaigns.
It avoids many higher-level Windows APIs and instead uses direct WoW64 syscalls plus AFD-based networking, which can reduce visibility for some security products.
G DATA said the malware targets browser credentials, cookies, login data, Steam-related information, and system fingerprinting data.
Because the same delivery chain can push different stealers, defenders need to detect the infrastructure and loader behavior, not just one malware family.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages