New Perseus Android malware steals notes and enables full device takeover
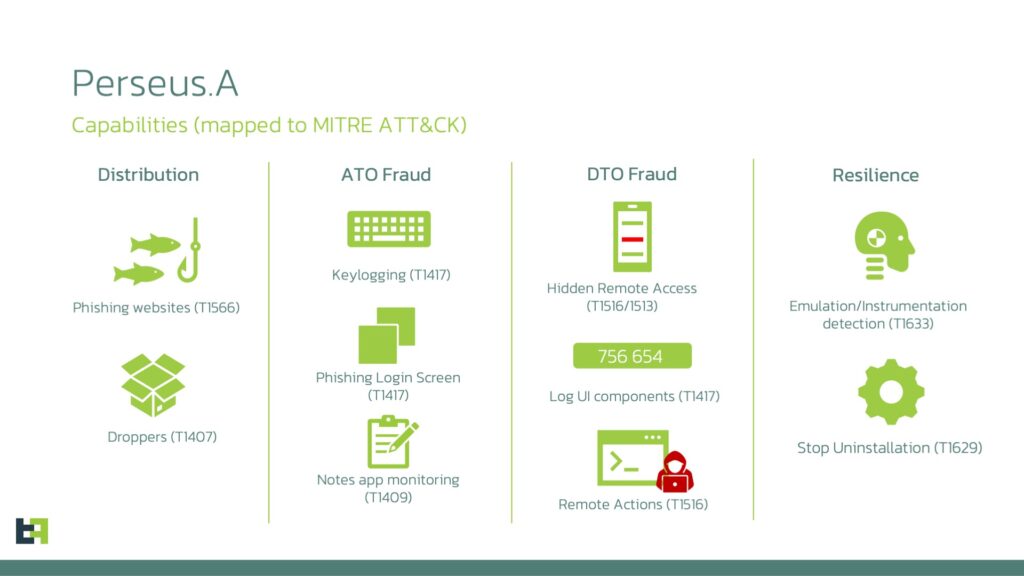
A newly documented Android banking trojan called Perseus can do more than steal credentials. ThreatFabric says the malware supports full device takeover, uses overlay attacks and keylogging, and includes an unusual feature that lets it silently inspect note-taking apps for sensitive data such as passwords, wallet recovery phrases, and financial details.
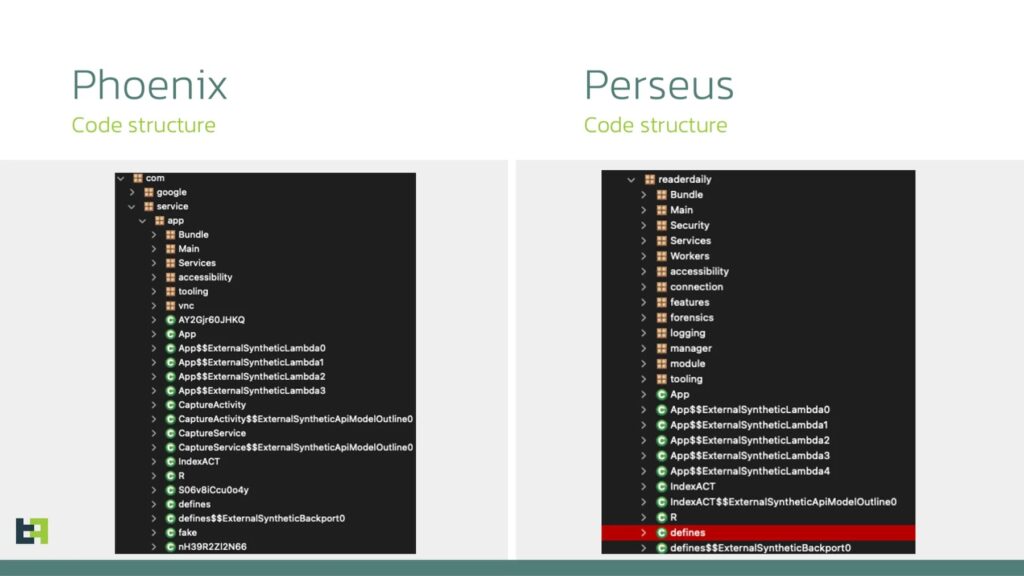
Perseus appears to build on old but still influential Android malware code. ThreatFabric says the family is based on leaked Cerberus source code and shows strong ties to the Phoenix codebase, with attackers refining those foundations into a more modern device-takeover threat. That makes Perseus less of a one-off malware sample and more of an example of how leaked banking trojan code keeps fueling new Android threats.
The malware has been observed in campaigns targeting users mainly in Turkey and Italy, though researchers say the targeting also extends to Poland, Germany, France, Portugal, the UAE, and cryptocurrency-related services. ThreatFabric says the operators often distribute Perseus through fake IPTV apps outside the Play Store, and use a dropper to help bypass Android 13 and newer sideloading restrictions.
What makes Perseus stand out is its ability to go after private notes. ThreatFabric says a command called scan_notes checks whether note-taking apps are installed, then opens them one by one and moves through saved entries with Accessibility Services. The malware can capture note content in the background without direct user interaction, which gives attackers a way to collect secrets many people wrongly treat as safe on their phones.
That feature raises the stakes because note apps often hold high-value data. Users frequently store passwords, one-time backup codes, crypto seed phrases, account numbers, and other personal details in simple text notes. If malware can quietly pull that data, attackers may not need to break into a password manager or wait for a banking login.
ThreatFabric also says Perseus uses Accessibility Services as the backbone of its operation. Once granted those permissions, the malware can monitor screens, log input, automate taps, and help criminals take control of the device remotely. Combined with banking overlays and credential theft, that creates a full fraud toolkit that can support unauthorized transactions and account abuse.
How Perseus works
Perseus relies on several familiar Android banking trojan tactics, but it combines them in a way that makes it more dangerous:
- Overlay attacks that place fake login screens over real banking apps
- Keylogging that captures typed information
- Accessibility abuse for navigation and remote actions
- Device takeover features that let attackers interact with the phone
- Note-stealing behavior aimed at apps that may contain sensitive text
ThreatFabric says the malware inherits several of these capabilities from Phoenix, especially around overlays, keylogging, and remote interaction.
Why the note-stealing feature matters
Most Android banking trojans focus on app credentials, SMS interception, or screen control. Perseus adds a quieter but highly valuable data source: personal notes. ThreatFabric says the malware can identify installed note apps, open entries, extract text, and move back through the interface automatically.
That gives attackers access to information users may have typed months earlier and then forgotten about. A stored recovery phrase or copied password can be enough to empty a crypto wallet, take over an email account, or unlock broader financial fraud. This is a direct risk inference from the kinds of secrets ThreatFabric says Perseus targets in note apps.
Targeted apps and regions
ThreatFabric says Perseus monitors popular note-taking apps including:
- Google Keep
- Xiaomi Notes
- Samsung Notes
- ColorNote
- Evernote
- Microsoft OneNote
- Simple Notes Pro
- Simple Notes
The researchers also say Perseus targets more than 50 institutions across eight countries and nine cryptocurrency platforms, with a strong focus on Turkey and Italy.
Perseus Android malware at a glance
| Item | Details |
|---|---|
| Malware name | Perseus |
| Threat type | Android banking trojan / device takeover malware |
| Reported by | ThreatFabric |
| Main delivery lure | Fake IPTV apps |
| Core abuse method | Accessibility Services |
| Key capabilities | Overlay attacks, keylogging, remote control, note theft |
| Notable feature | Silent scanning of note-taking apps |
| Main target regions | Turkey and Italy, with broader regional reach |
| Code lineage | Built on leaked Cerberus code, with Phoenix links |
What Android users should do
Users can cut their risk by keeping installs inside trusted app stores, leaving Google Play Protect enabled, and refusing Accessibility permissions unless an app clearly needs them. ThreatFabric also warns users not to store passwords, wallet recovery phrases, or other sensitive credentials inside note apps, because malware abusing Accessibility can read that information without obvious warnings.
A few practical steps matter most:
- Avoid sideloading APK files from unknown sites
- Be skeptical of streaming, IPTV, or utility apps offered outside official stores
- Review Accessibility permissions regularly
- Remove apps that ask for excessive access
- Keep Android and installed apps fully updated
- Move sensitive secrets out of plain-text notes
FAQ
Perseus is a newly reported Android banking trojan that supports credential theft, overlays, keylogging, remote device interaction, and silent collection of data from note-taking apps.
ThreatFabric says Perseus includes a scan_notes command that can open note apps and extract text from saved entries, which is not commonly seen in similar malware families.
Researchers say attackers distribute it through fake IPTV apps and use a dropper to help get around sideloading restrictions on newer Android versions.
ThreatFabric says the campaign mainly targets Turkey and Italy, but also extends to Poland, Germany, France, Portugal, the UAE, and cryptocurrency platforms.
Users should avoid storing passwords, recovery phrases, financial credentials, and similar secrets in note apps, because Perseus can silently inspect and steal that data.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages