New STX RAT uses hidden remote desktop and infostealer features to evade detection
STX RAT is a newly identified Windows remote access trojan that combines stealthy remote control with credential theft. Researchers say it gives attackers hidden desktop access through HVNC, steals credentials from tools like FileZilla, WinSCP, and Cyberduck, and uses strong encryption to protect its command traffic.
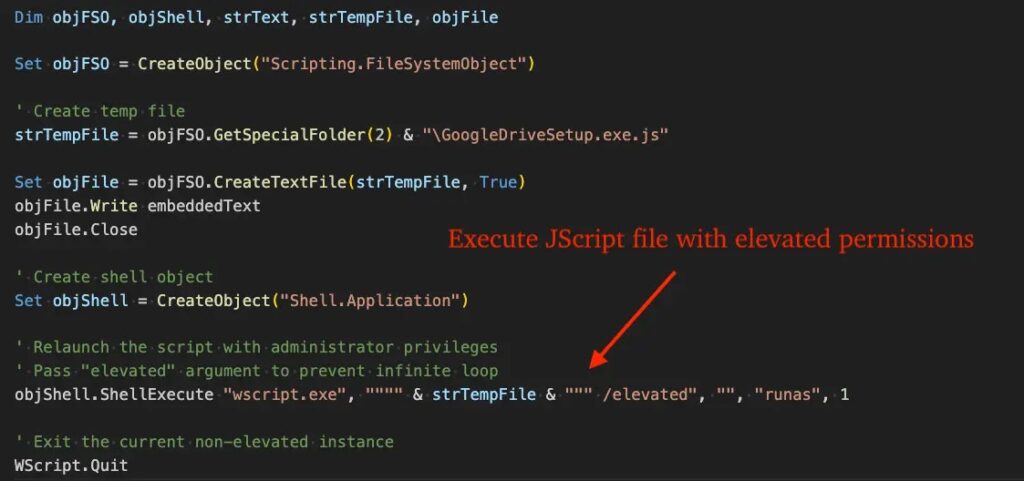
The malware first appeared in late February 2026 during an attempted intrusion against a financial sector target, according to eSentire. The researchers say the first observed delivery chain started with a browser-downloaded VBScript file, which launched a JScript stage and then a PowerShell loader that injected the final payload into memory.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes STX RAT more dangerous than a basic infostealer is its hidden remote desktop capability. Instead of taking over the victim’s visible screen, it can create a separate hidden desktop session where attackers browse, click, type, and move around the system without the user seeing any of it.
How STX RAT gets in
eSentire says the malware uses a multi-stage loader chain and memory execution to reduce its visible footprint. The report also notes that by early March 2026, another delivery path had already appeared through trojanized FileZilla installers, which suggests the operators were testing more than one infection route almost immediately.
Malwarebytes reported that the fake FileZilla campaign relied on a trojanized copy of FileZilla 3.69.5 distributed from an unofficial lookalike site. In that case, the attackers added a malicious version.dll file to the package, letting Windows load the malware inside what looked like a normal FileZilla session.
That matters because this is not a vulnerability in FileZilla itself. Malwarebytes says the infection depends on deception, such as search poisoning or lookalike domains, which means users and defenders still need to watch for poisoned downloads even when the software brand looks familiar.
Why defenders should pay attention
eSentire says STX RAT checks for analysis environments linked to VirtualBox, VMware, and QEMU. If it sees signs of a sandbox or virtual machine, it can delay and exit, which makes automated analysis harder and can reduce the chance of immediate detection.
The malware also interferes with AMSI-related protection. Microsoft says AMSI is built to help antimalware tools scan scripts, memory content, PowerShell activity, Windows Script Host, JavaScript, and VBScript. That makes any AMSI evasion tactic especially relevant in a loader chain that leans on scripts and in-memory execution.
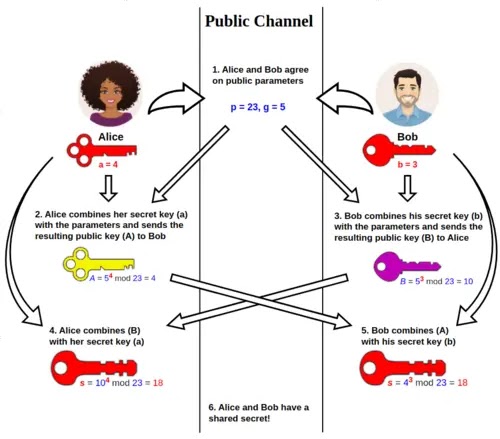
Once active, STX RAT reportedly sends host details to its command server, including the username, hostname, OS version, admin status, RAM, and detected antivirus tools. eSentire says the malware protects this traffic with X25519 key exchange and ChaCha20-Poly1305 encryption, which makes passive inspection and session decryption much harder for defenders.
Hidden desktop access changes the game
The standout feature is HVNC, short for Hidden Virtual Network Computing. eSentire says STX RAT can start hidden desktop sessions and then accept commands for keystrokes, mouse input, scrolling, pasting, and desktop switching, all while the victim continues using the normal visible desktop.
That setup gives attackers more than simple theft. It gives them a quiet operating space for logging into admin portals, moving through internal systems, opening files, or staging follow-on payloads without showing obvious signs on the user’s screen.
The credential theft side adds even more value for the operator. eSentire says the malware targets saved credentials from FileZilla, WinSCP, and Cyberduck, and can also capture a desktop screenshot before sending the stolen data out, giving the attacker both account access and visual context.
STX RAT at a glance
| Item | Verified detail |
|---|---|
| Malware name | STX RAT |
| First observed | Late February 2026 |
| Early target | Financial sector organization |
| Initial loader chain | VBScript to JScript to PowerShell to in-memory payload |
| Secondary distribution | Trojanized FileZilla installer route |
| Stealth feature | HVNC hidden desktop sessions |
| Theft targets | FileZilla, WinSCP, Cyberduck credentials |
| Traffic protection | X25519 and ChaCha20-Poly1305 |
| Analysis evasion | VM checks and delayed exit behavior |
What security teams should do
- Block the known C2 IP and related infrastructure identified by eSentire.
- Hunt for elevated WScript activity, JScript execution from Temp paths, and suspicious PowerShell stdin execution.
- Review whether VBScript and JScript remain necessary in the environment. If not, disable them.
- Enable Microsoft Defender attack surface reduction rules that block obfuscated scripts and prevent JavaScript or VBScript from launching downloaded executables. Microsoft lists both as supported ASR controls.
- Tighten software download policies so users install tools like FileZilla only from trusted official sources.
FAQ
STX RAT is a remote access trojan that blends stealthy remote control with credential theft. Researchers say it can run hidden desktop sessions, steal credentials, and communicate with its operators over encrypted channels.
HVNC lets attackers operate on a hidden desktop that the victim cannot see. That means they can browse, type, open apps, and move through a system without taking over the visible screen.
The reported FileZilla infection route did not rely on a flaw in FileZilla. Malwarebytes says attackers distributed a trojanized package from an unofficial site and inserted a malicious DLL into it.
Yes. Microsoft says AMSI helps antimalware products inspect script and memory activity, and Defender ASR rules can block potentially obfuscated scripts and prevent JavaScript or VBScript from launching downloaded executables.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages