North Korean IT worker allegedly used stolen identity and AI-written resume in failed job scam

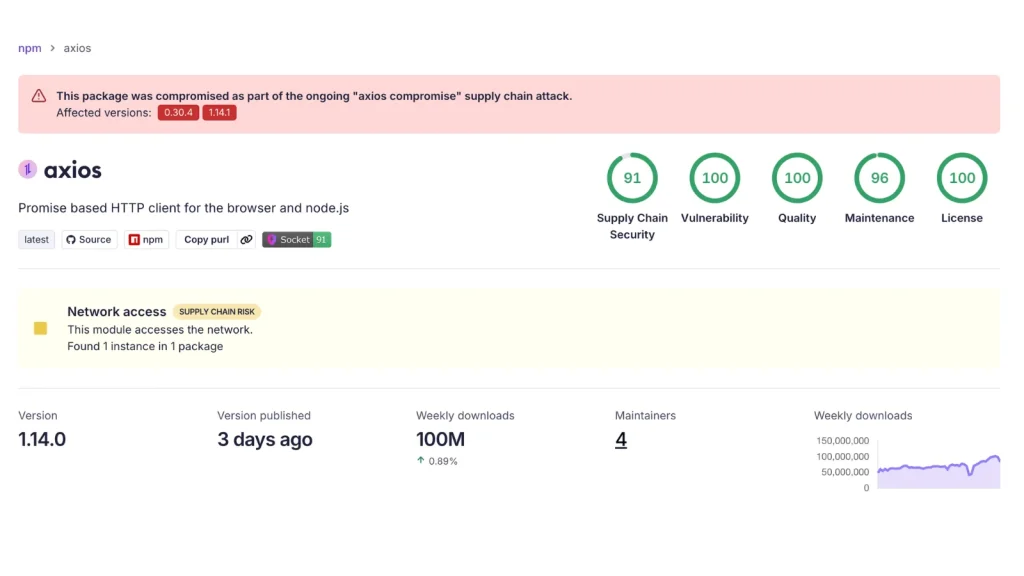
A suspected North Korean operative allegedly tried to land a remote cybersecurity job by posing as a U.S.-based AI architect, using a stolen identity, a likely AI-assisted resume, and a VoIP phone number to appear legitimate. The attempt failed, but the case shows how remote hiring fraud has become harder to spot as threat actors mix identity theft, resume tailoring, and interview assistance tools.
Nisos disclosed the case after investigating an applicant for a Lead AI Architect role who claimed to be based in Palm Beach Gardens, Florida. According to the company, the applicant used IP addresses that likely belonged to the Astrill VPN network, a service that multiple researchers have linked to North Korean remote worker activity.
The broader threat is already well established. The FBI says North Korean IT workers use fake or stolen identities, U.S.-based facilitators, shipped laptops, remote access tools, and even AI services to gain jobs at American firms and route money back to the regime in violation of sanctions.
How the applicant was flagged
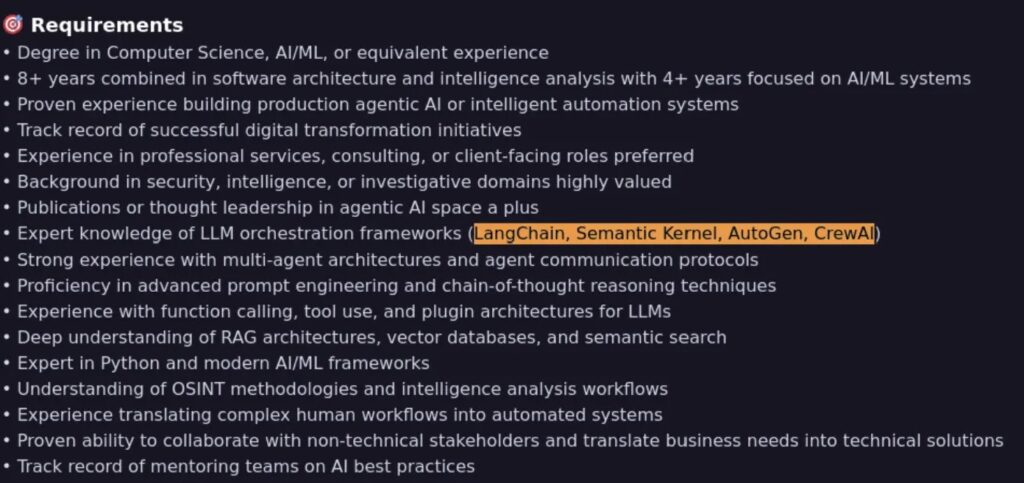
Nisos said the applicant’s resume mirrored large parts of the job description, including long lists of technical skills and summary language tied to agentic AI work. The firm concluded the document likely came from an AI chatbot or heavy copy-paste editing designed to beat keyword filters in hiring systems.
Investigators also found that the phone number on the application was likely a VoIP number. On its own, that does not prove fraud, but Nisos said scammers often use internet-based numbers that match the area code of the place they claim to live.
The interview raised more concerns. Nisos said that during a virtual interview on June 24, 2025, the applicant repeatedly looked away from the camera and stumbled when asked about a fake hurricane that had never struck Florida. The answer pattern suggested he may have been waiting for help from a script or chatbot.
Multiple resumes, one real victim
The firm said it discovered three separate resume accounts under the same name, but with different universities, employers, and Florida locations. All of them appeared tied to a real person whose personal details were allegedly misused without his knowledge.
That detail matters because this case fits a much larger enforcement picture. In June 2025, the U.S. Department of Justice announced nationwide actions tied to North Korean remote IT worker schemes, saying the actors used fake and stolen identities, front companies, fraudulent websites, and laptop farms across 16 states, and that some had gained jobs at more than 100 U.S. companies.
Treasury also warned in March 2026 that these overseas IT operatives use fabricated personas, fraudulent documents, and stolen identities to secure jobs, then generate revenue that supports North Korea’s weapons and missile programs.
Why this case matters to employers
This was not just a fake resume problem. It was a possible insider-risk attempt aimed at a cybersecurity company, which shows that even security-focused employers can face well-prepared hiring fraud. The DOJ has said some North Korean workers stole sensitive employer data and, in at least one case, virtual currency worth more than $900,000.
The FBI says U.S.-based enablers sometimes receive company laptops, set up remote access, open financial accounts, create job-site profiles, and even attend interviews on behalf of the real operator. That means a company can complete what looks like a normal remote hire while the actual worker sits overseas behind multiple layers of deception.
In this case, Nisos said a company-issued laptop later appeared in a closet with other devices, remotely controlled through PiKVM hardware and connected through Tailscale. That detail supports a common law enforcement warning: remote hiring fraud does not end with a bad interview or a fake CV. It can become a direct access path into a company’s systems and data.
Key red flags in this case
- Resume language closely mirrored the job posting.
- The applicant used a likely VoIP phone number tied to the claimed U.S. location.
- The login IPs likely belonged to the Astrill VPN network.
- Three resume profiles showed different schools, employers, and cities.
- The candidate struggled in a live video interview and appeared to rely on another screen.
- The mailing address for equipment did not match the resume address.
- The laptop reportedly ended up in a multi-device laptop farm setup.
What companies should check during remote hiring
| Risk area | What happened in this case | What employers should do |
|---|---|---|
| Identity | Real person’s details were allegedly reused | Cross-check ID, address, phone, and public records |
| Resume | Skills and summary mirrored the job post | Look for unnatural overlap with the job listing |
| Interview | Candidate appeared to rely on off-screen help | Use live follow-up questions and screen-sharing |
| Contact details | Phone number was likely VoIP-based | Verify carrier type and ownership history |
| Location | VPN-linked IPs masked true origin | Log and review IP reputation and geo patterns |
| Equipment | Device shipment details reportedly changed | Confirm shipping address and recipient identity |
| Access risk | Laptop allegedly ended up in a laptop farm | Lock down remote access and monitor device behavior |
FAQ
Nisos described the applicant as a suspected DPRK operative and tied the behavior to known North Korean IT worker tactics. U.S. agencies have separately documented the same broader methods in official alerts and enforcement actions.
According to Nisos, the resume likely used AI assistance because it repeated job-description language and skill lists in an unusually direct way. The firm also suspected chatbot or scripted assistance during the interview.
The FBI, DOJ, and Treasury say these schemes generate revenue for the North Korean regime, evade sanctions, and can also expose victim companies to theft, extortion, and data loss.
Do not treat hiring as only an HR function. In remote roles, hiring is also a security checkpoint. Identity checks, live verification, device controls, and behavioral screening now matter as much as technical interviews.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages