North Korean IT Worker Scam and Contagious Interview Malware Campaigns Exposed

North Korean threat actors run dual operations targeting developers worldwide. Contagious Interview tricks candidates into running malware during fake technical interviews. Fake IT workers embed inside real companies, earning wages that fund regime operations. GitLab banned 131 DPRK accounts in 2025 alone, peaking at 11 per month in September.
Since 2022, recruiters contact developers on LinkedIn and GitHub with convincing profiles. Victims receive technical tasks requiring code execution. BeaverTail and OtterCookie malware activate silently, stealing credentials and granting remote access. Thousands impacted as campaigns scale globally.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Parallel scheme places North Korean operatives as fraudulent employees. Beijing cell manager Kil-Nam Kang oversaw 7 workers earning $1.64 million from Q1 2022-Q3 2025. Funds flow through freelance platforms using stolen identities.
GitLab detected sophisticated concealment. 80%+ cases used hidden loaders fetching payloads from Vercel instead of direct storage. Malware spread across multiple project files evades code review. Encoded staging URLs hid in .env files as config variables.
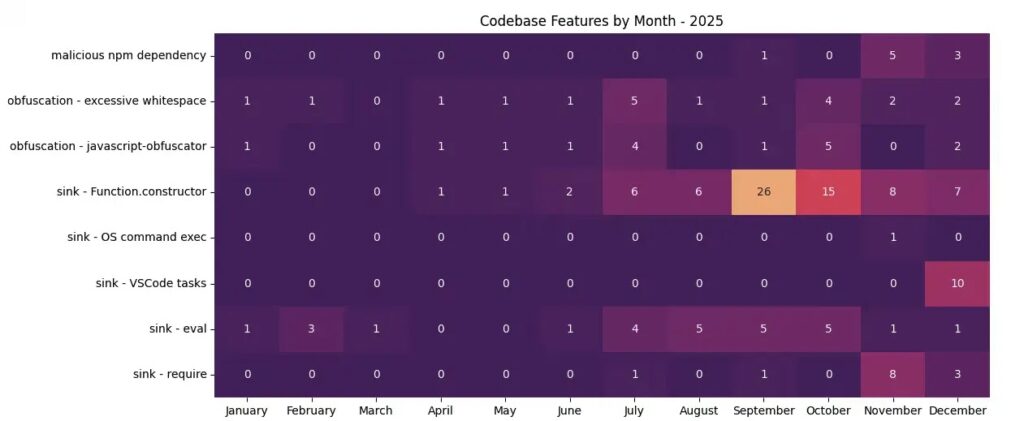
December 2025 introduced VS Code task configs decoding payloads from fake font files. JavaScript’s Function.constructor executes downloaded code dynamically. Request headers protected staging servers from casual analysis.
Malware Distribution Tactics
Primary Vector: Fake recruiter profiles → technical interview tasks → code execution
Concealment: Multi-file spread, remote payload fetch, decoy content
Evasion: Encoded URLs in .env, VS Code task configs, fake fonts
C2 Infrastructure: Vercel-hosted staging with header validation
GitLab analysis shows consistent patterns across 131 accounts. September 2025 peak correlates with crypto market volatility. DPRK shifts from exchange hacks to developer targeting.
Campaign Impact Table
| Operation | Method | Financial Gain | Detection Count |
|---|---|---|---|
| Contagious Interview | Fake interviews | Credential theft | Thousands impacted |
| IT Worker Scam | Fake employees | $1.64M (2022-25) | 131 GitLab bans |
| Malware Distribution | GitLab loaders | Remote access | 11/mo peak Sep 2025 |
Developer machines become corporate footholds. Stolen credentials access production systems. Remote control enables lateral movement and data exfiltration.
Technical Execution Flow
- Recruiter contacts developer with LinkedIn profile and GitHub repo
- Technical task requires local execution (npm install, yarn dev)
.envfile loads staging URL disguised as API endpoint- Error handler fetches payload via custom headers
Function.constructorexecutes malware granting remote shell- BeaverTail/OtterCookie activates for credential harvest
VS Code variant hides payloads in fake font files decoded at task execution. Multi-platform support targets macOS, Windows, Linux developers equally.
Defense Recommendations
- Verify recruiter LinkedIn profiles through mutual connections
- Never run code from interview tasks without sandbox isolation
- Scan
.envfiles for encoded URLs and base64 artifacts - Monitor VS Code task configs for suspicious font file references
- Block Vercel domains known for staging infrastructure
- Implement behavioral monitoring for
Function.constructorusage
Organizations face nation-state persistence once developers compromise endpoints. GitLab stresses proactive repo scanning prevents malware staging entirely.
Enterprises unknowingly paid DPRK workers through freelance platforms. Identity verification gaps persist across Upwork, Toptal, and GitHub sponsors. Multi-year operations show sophisticated opsec.
FAQ
North Korean fake job interviews delivering BeaverTail/OtterCookie malware via technical tasks.
$1.64 million across 7 operatives managed by Kil-Nam Kang (2022-2025).
131 DPRK accounts banned in 2025, peaking 11/month September.
VS Code task configs decoding malware from fake font files (Dec 2025).
Verify recruiters, sandbox interview code, scan .env files, monitor Function.constructor.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages