NoVoice malware hid in 50+ Google Play apps and reached at least 2.3 million downloads

A newly detailed Android malware campaign called Operation NoVoice hid inside more than 50 apps on Google Play and reached at least 2.3 million downloads before removal. McAfee says the campaign used a rootkit that targeted older, unpatched Android devices and could persist even after a factory reset on some affected phones.
The malware did not need obvious dangerous permissions to get started. McAfee says the carrier apps looked like normal cleaners, gallery tools, and games, and the attack began after the app was opened, with no sideloading required. The malicious components were blended into common app structures, including Facebook SDK-related naming, to look less suspicious.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The headline number needs care. McAfee confirmed at least 2.3 million downloads, not 2.3 million proven successful root compromises. The real infection count could be lower because the rootkit depended on device-specific exploit success and older patch levels. McAfee says devices with a security patch level of 2021-05-01 or higher were not susceptible to the exploits it recovered from the command-and-control server.
Why NoVoice stands out
NoVoice is more serious than a typical Android trojan because it tries to gain root access and then modify core system behavior. McAfee says the malware overwrites a core system library so every app on the device can run attacker-controlled code at launch. That gives the operators a much deeper foothold than ordinary app-level spyware.
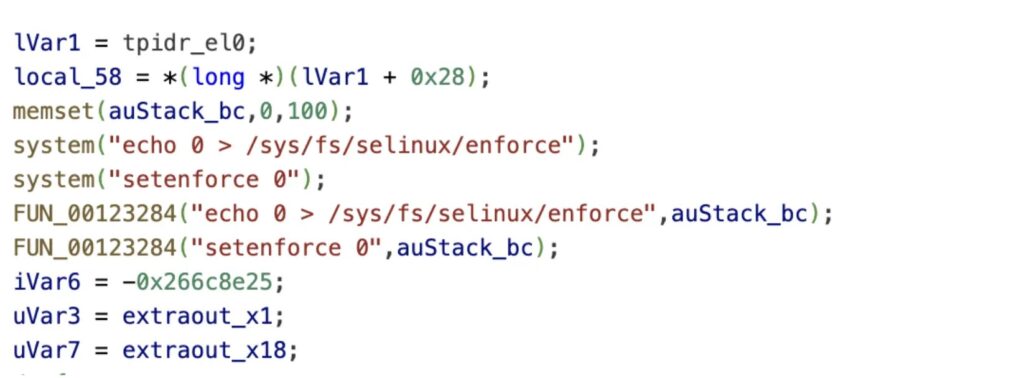
The campaign also used a large exploit toolkit. McAfee says it recovered 22 exploits from the attack infrastructure, and one analyzed chain used an IPv6 use-after-free, a Mali GPU driver bug, and credential patching plus SELinux disablement to finish the compromise.
That makes older Android phones the biggest concern. McAfee says Android 7 and lower devices that stopped receiving Android security updates remain at particular risk, and a normal factory reset will not fully remove the rootkit once it writes into the system partition.
How the malware stayed quiet
McAfee says the campaign name comes from a silent audio resource called R.raw.novioce, a deliberate misspelling of “no voice.” The file plays at zero volume to keep a foreground service alive while staying effectively invisible to the user.
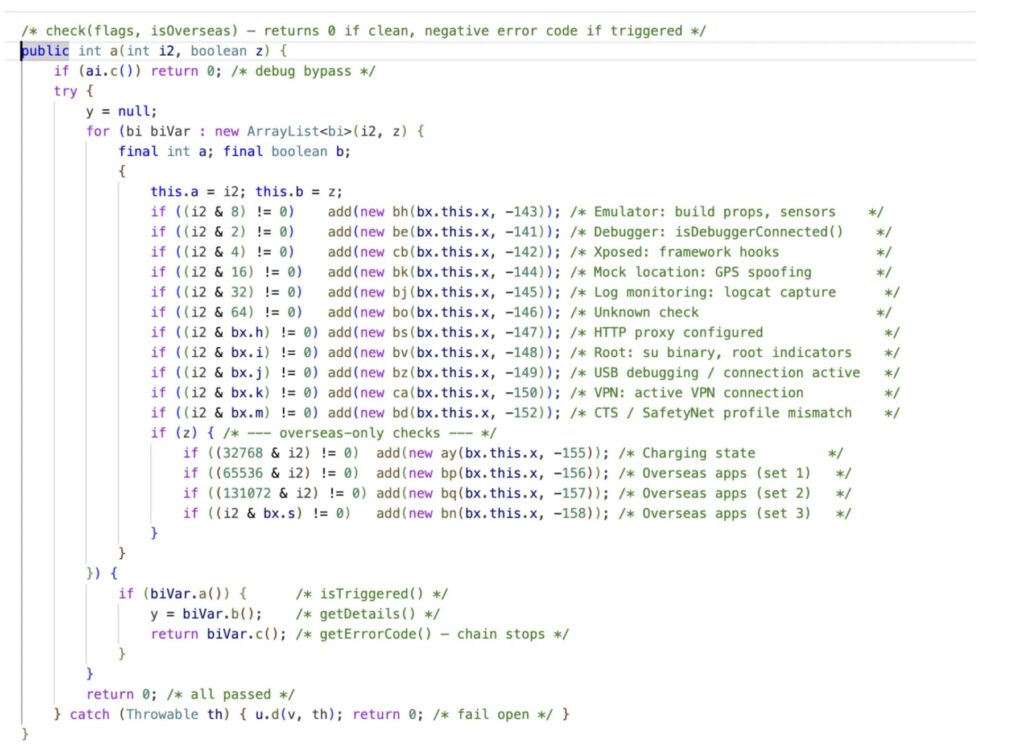
The malware also hid its early payload in what looked like a normal image file. McAfee says the encrypted malicious content sat after the PNG end marker, so the file still rendered normally while carrying a hidden payload. That helped the apps pass casual inspection and simple scanning.
Google says Play Protect checks apps and devices for harmful behavior, can warn users about malicious apps, and may disable or remove harmful apps automatically. Even so, this campaign shows that bad apps can still get through and stay live long enough to rack up major install numbers before detection and removal.
What the attackers wanted
McAfee says the only theft module it recovered targeted WhatsApp. The payload copied WhatsApp’s encrypted database, extracted session-related keys and account data, and sent the stolen information to attacker infrastructure so the operators could clone the victim’s session on another device.
That does not mean WhatsApp was the only goal. McAfee says the framework was plugin-based and designed to accept any objective at runtime, which means the operators could push new payloads later without changing the original carrier app.
The attack infrastructure also remained active when McAfee published its research. That suggests the campaign had room to evolve even after the first public disclosure.
Key facts
| Item | Verified detail |
|---|---|
| Campaign name | Operation NoVoice |
| Distribution | More than 50 apps on Google Play |
| Reach | At least 2.3 million downloads |
| Exploit count recovered | 22 exploits |
| Most exposed devices | Older Android devices, especially Android 7 and lower |
| Patch threshold McAfee cited | 2021-05-01 or higher not susceptible to the recovered exploits |
| Persistence | Can survive factory reset on some rooted devices |
| Recovered theft payload | WhatsApp session cloning module |
What Android users should do now
- Check your Android security patch level and update it if your device still receives updates. Google says Play Protect works alongside Android security updates, and Android’s May 2021 bulletin states that security patch levels of 2021-05-01 or later address all issues associated with that patch level.
- Keep Google Play Protect turned on. Google says it checks apps on install, scans devices periodically, and may disable or remove harmful apps automatically.
- Remove suspicious cleaner, gallery, and utility apps you do not recognize, especially on older phones. McAfee says those app categories were common carriers in this campaign.
- If you suspect a rooted infection on an older unsupported device, do not rely on a factory reset alone. McAfee says a full firmware reflash is required to fully restore a compromised device.
- Treat WhatsApp and other account sessions as exposed if the device shows signs of compromise. Change passwords, re-register accounts, and review active sessions from a clean device. This recommendation follows from McAfee’s finding that the recovered payload targeted WhatsApp session data.
FAQ
Yes. McAfee says all carrier apps in the campaign were distributed through Google Play and required no sideloading.
Not necessarily. McAfee confirmed at least 2.3 million downloads across the malicious apps, but successful exploitation depended on device age, patch level, and exploit compatibility.
Not on the older rooted devices McAfee described. The researchers say the rootkit can survive a standard factory reset because it writes to the system partition, and only a clean firmware reflash fully removes it.
McAfee says the only recovered payload targeted WhatsApp session cloning by stealing encryption databases, keys, and related account data.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages